Steps for connecting to a tklm appliance, Steps for connecting to a tklm appliance 1 – Brocade Network Advisor SAN + IP User Manual v12.3.0 User Manual
Page 1093
Brocade Network Advisor SAN + IP User Manual
1021
53-1003155-01
Steps for connecting to a TKLM appliance
25
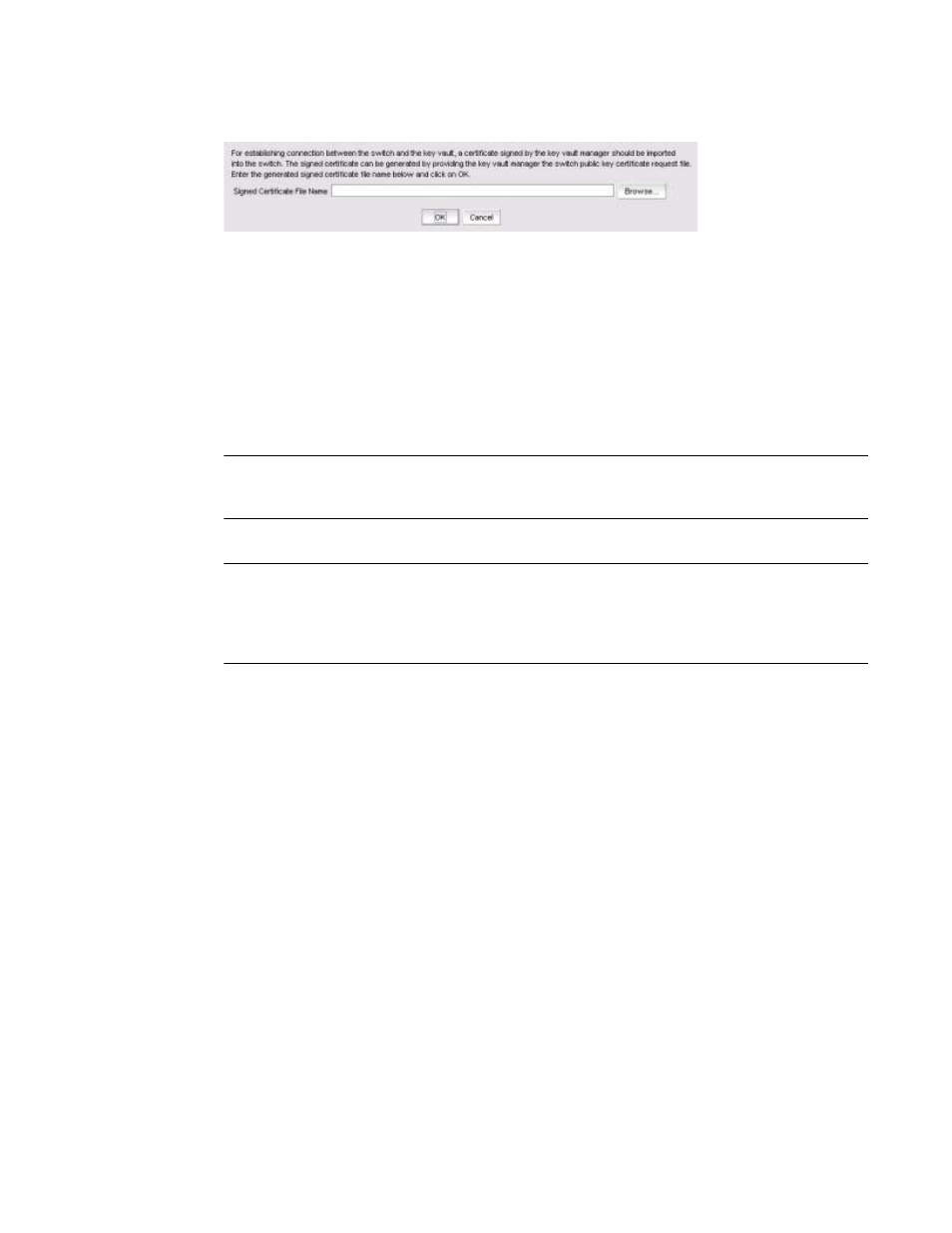
FIGURE 395
Import Signed Certificate dialog box
2. Browse to the location where the signed certificate is stored, then click OK.
The signed certificate is stored on the switch.
Steps for connecting to a TKLM appliance
All switches you plan to include in an encryption group must have a secure connection to the Tivoli
Key Lifecycle Manager (TKLM). A local LINUX host must be available to transfer certificates.
NOTE
Ensure that the time zone and clock time setting on the TKLM server and encryption nodes are the
same. A difference of only a few minutes can cause the TLS connectivity to fail.
Repeat the same steps for configuring both the primary and secondary key vaults.
NOTE
The primary and secondary key vaults should be registered before you export the master key or
encrypting LUNs. If the secondary key vault is registered after encryption is done for some of the
LUNs, then the key database should be backed up and restored on the secondary TKLM from the
registered primary TKLM before registering the secondary TKLM.
The following is a suggested order for the steps needed to create a secure connection to TKLM:
1. Initialize all encryption nodes to generate KAC certificates.
2. Export the signed KAC certificates to a local LINUX host. Refer to
3. Obtain the necessary user credentials and log in to the TKLM server appliance from the TKLM
management web console.
4. Create a default key store on TKLM. Refer to
“Establishing a default key store and device group
5. Create a device group named BRCD_ENCRYPTOR with device family LTO.
6. Add devices to the group. Refer to
“Adding a device to the device group”
7. Create a certificate for the TKLM server. Refer to
“Creating a self-signed certificate for TKLM”
8. Import the node KAC certificates. Refer to
“Importing the Fabric OS encryption node KAC
9. Export the server CA certificate to a LINUX or Windows host. Refer to
self-signed server certificate”
10. Add encryption group members as needed. The first node added to an encryption group
functions as the Group Leader. It is valid to have only one node in an encryption group.
