Association, Wlan data security – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 354
333
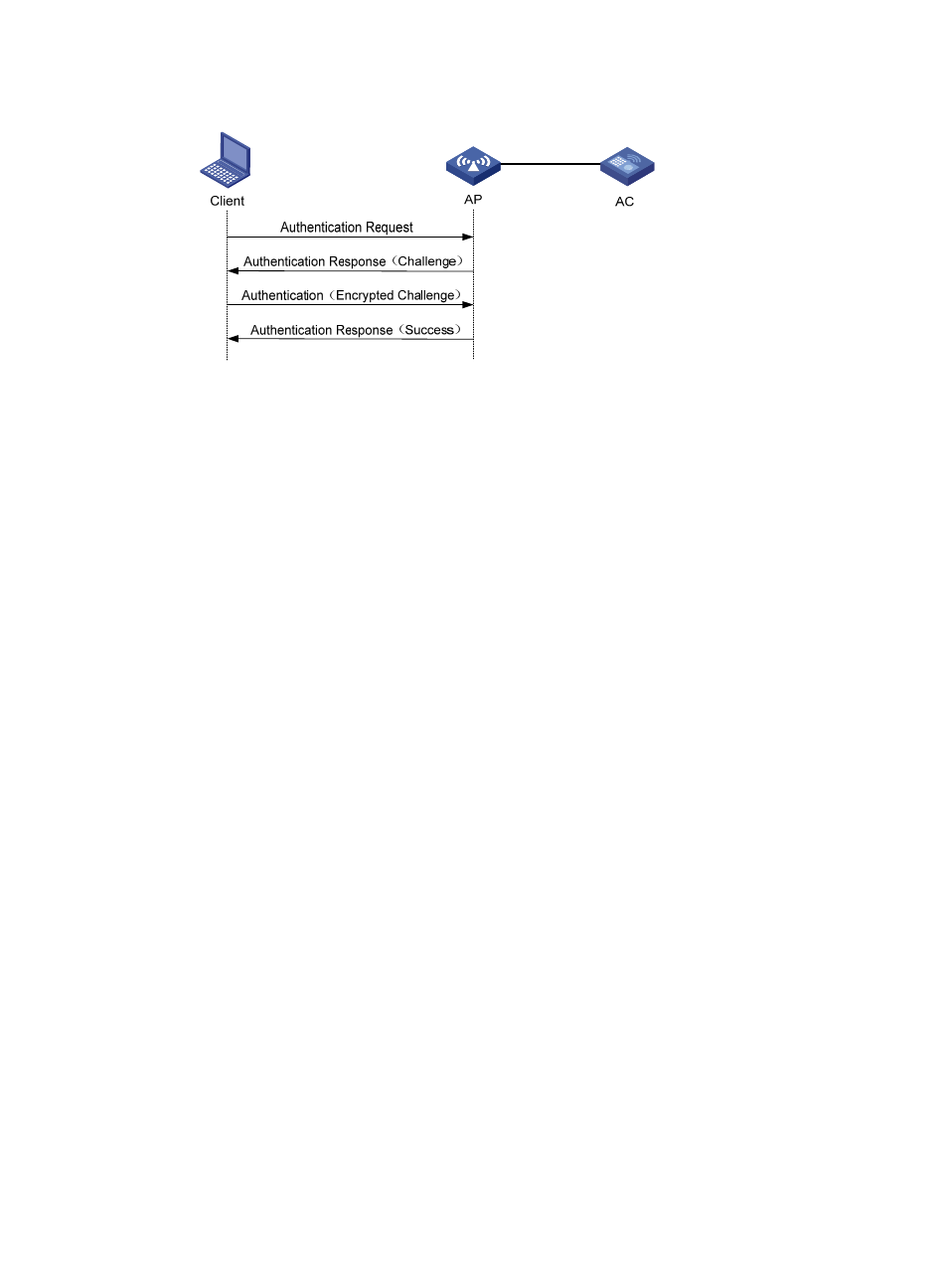
Figure 325 Shared key authentication process
Association
To access a wireless network through an AP, a client must associate with that AP. After the client passes
authentication on the AP, the client sends an association request to the AP. The AP verifies the capability
information in the association request to determine the capability supported by the wireless client, and
sends an association response to notify the client of the association result. A client can associate with only
one AP at a time, and an association process is always initiated by the client.
WLAN data security
Compared with wired networks, WLAN networks are more susceptible to attacks because all WLAN
devices share the same medium and every device can receive data from any other sending device. If no
security service is provided, plain-text data is transmitted over the WLAN.
To secure data transmission, 802.11 protocols provide encryption methods to make sure devices without
the right key cannot read encrypted data.
•
Plain-text data.
It is a WLAN service without security protection. No data packets are encrypted.
•
WEP encryption.
Wired Equivalent Privacy (WEP) was developed to protect data exchanged among authorized
users in a wireless LAN from casual eavesdropping. WEP uses RC4 encryption (a stream
encryption algorithm) for confidentiality. WEP encryption uses static and dynamic encryption
depending on how a WEP key is generated.
Static WEP encryption
With Static WEP encryption, all clients using the same SSID must use the same encryption key.
If the encryption key is deciphered or lost, attackers will access all encrypted data. In addition,
periodical manual key update enhances the management workload.
Dynamic WEP encryption
Dynamic WEP encryption is an improvement over static WEP encryption. With dynamic WEP
encryption, WEP keys are negotiated between the client and server through the 802.1X
protocol so that each client is assigned a different WEP key, which can be updated
periodically to further improve unicast frame transmission security.
Although WEP encryption increases the difficulty of network interception and session hijacking,
it has weaknesses due to limitations of RC4 encryption algorithm and static key configuration.
•
TKIP encryption.
- H3C WX5500E Series Access Controllers H3C WX3500E Series Access Controllers H3C WX2500E Series Access Controllers H3C WX6000 Series Access Controllers H3C WX5000 Series Access Controllers H3C LSUM3WCMD0 Access Controller Module H3C LSUM1WCME0 Access Controller Module H3C LSRM1WCM2A1 Access Controller Module
