Brocade Mobility Access Point System Reference Guide (Supporting software release 5.5.0.0 and later) User Manual
Page 169
Brocade Mobility Access Point System Reference Guide
159
53-1003100-01
5
8. Select + Add Row to define the network address of a target peer and its security settings.
9. Select OK to save the changes made within the IKE Policy screen. Select Reset to revert to the
last saved configuration. Select the Delete Row icon to remove a peer configuration.
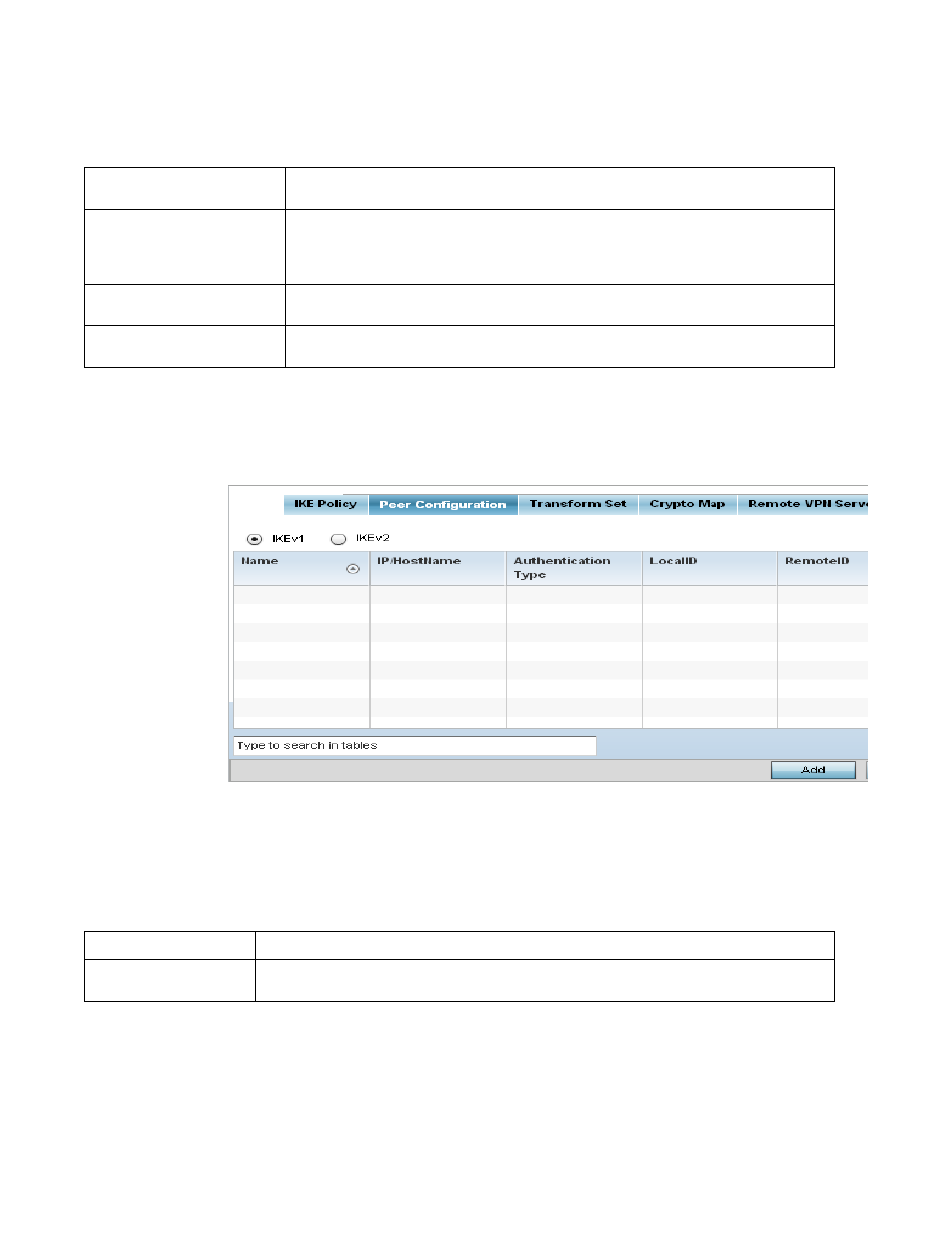
10. Select the Peer Configuration tab to assign additional network address and IKE settings to the
an intended VPN tunnel peer destination.
FIGURE 62
Profile Security - VPN Peer Destination screen (IKEv1 example)
11. Select either the IKEv1 or IKEv2 radio button to enforce VPN key exchanges using either IKEv1
or IKEv2.
12. Refer to the following to determine whether a VPN Peer Configuration requires creation,
modification or removal:
Name
If creating a new IKE policy, assign the target peer (tunnel destination) a 32 character maximum
name to distinguish it from others with a similar configuration.
DH Group
Use the drop-down menu to define a Diffie-Hellman (DH) identifier used by the VPN peers to
derive a shared secret password without having to transmit. DH groups determine the strength of
the key used in key exchanges. The higher the group number, the stronger and more secure the
key. Options include 2, 5 and 14. The default setting is 5.
Encryption
Select an encryption method used by the tunnelled peers to securely interoperate. Options
include 3DES, AES, AES-192 and AES-256. The default setting is AES-256.
Authentication
Select an authentication hash algorithm used by the peers to exchange credential information.
Options include SHA and MD5. The default setting is SHA.
Name
Lists the 32 character maximum name assigned to each listed peer configuration.
IP/Hostname
Displays the IP address (or host address FQDN) of the IPSec VPN peer targeted for secure tunnel
connection and data transfer.
