3 ead configuration, Introduction to ead, Typical network application of ead – H3C Technologies H3C S3600 Series Switches User Manual
Page 552: Ead configuration
3-1
3
EAD Configuration
Introduction to EAD
Endpoint Admission Defense (EAD) is an attack defense solution. Using this solution, you can enhance
the active defense capability of network endpoints, prevents viruses and worms from spreading on the
network, and protects the entire network by limiting the access rights of insecure endpoints.
With the cooperation of switch, AAA sever, security policy server and security client, EAD is able to
evaluate the security compliance of network endpoints and dynamically control their access rights.
With EAD, a switch:
z
Verifies the validity of the session control packets it receives according to the source IP addresses
of the packets: It regards only those packets sourced from authentication or security policy server
as valid.
z
Dynamically adjusts the VLAN, rate, packet scheduling priority and Access Control List (ACL) for
user terminals according to session control packets, whereby to control the access rights of users
dynamically.
Typical Network Application of EAD
EAD checks the security status of users before they can access the network, and forcibly implements
user access control policies according to the check results. In this way, it can isolate the users that are
not compliant with security standard and force these users to update their virus databases and install
system patches.
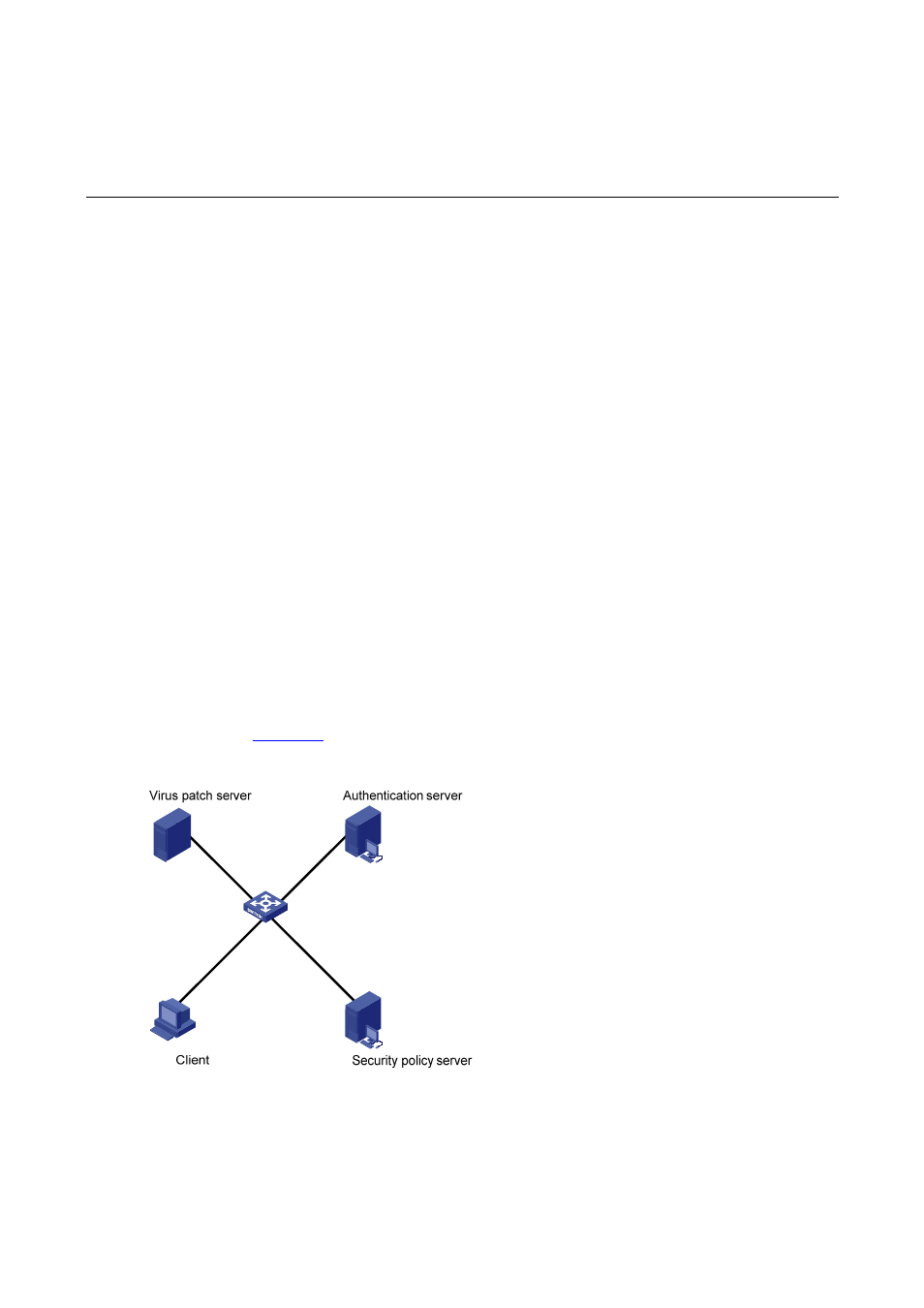
shows a typical network application of EAD.
Figure 3-1 Typical network application of EAD
After a client passes the authentication, the security Client (software installed on the client PC) interacts
with the security policy server to check the security status of the client. If the client is not compliant with
the security standard, the security policy server issues an ACL to the switch, which then inhibits the
client from accessing any parts of the network except for the virus/patch server.
