Aaa configuration examples, Remote radius authentication of telnet/ssh users, Network requirements – H3C Technologies H3C S3600 Series Switches User Manual
Page 545
2-29
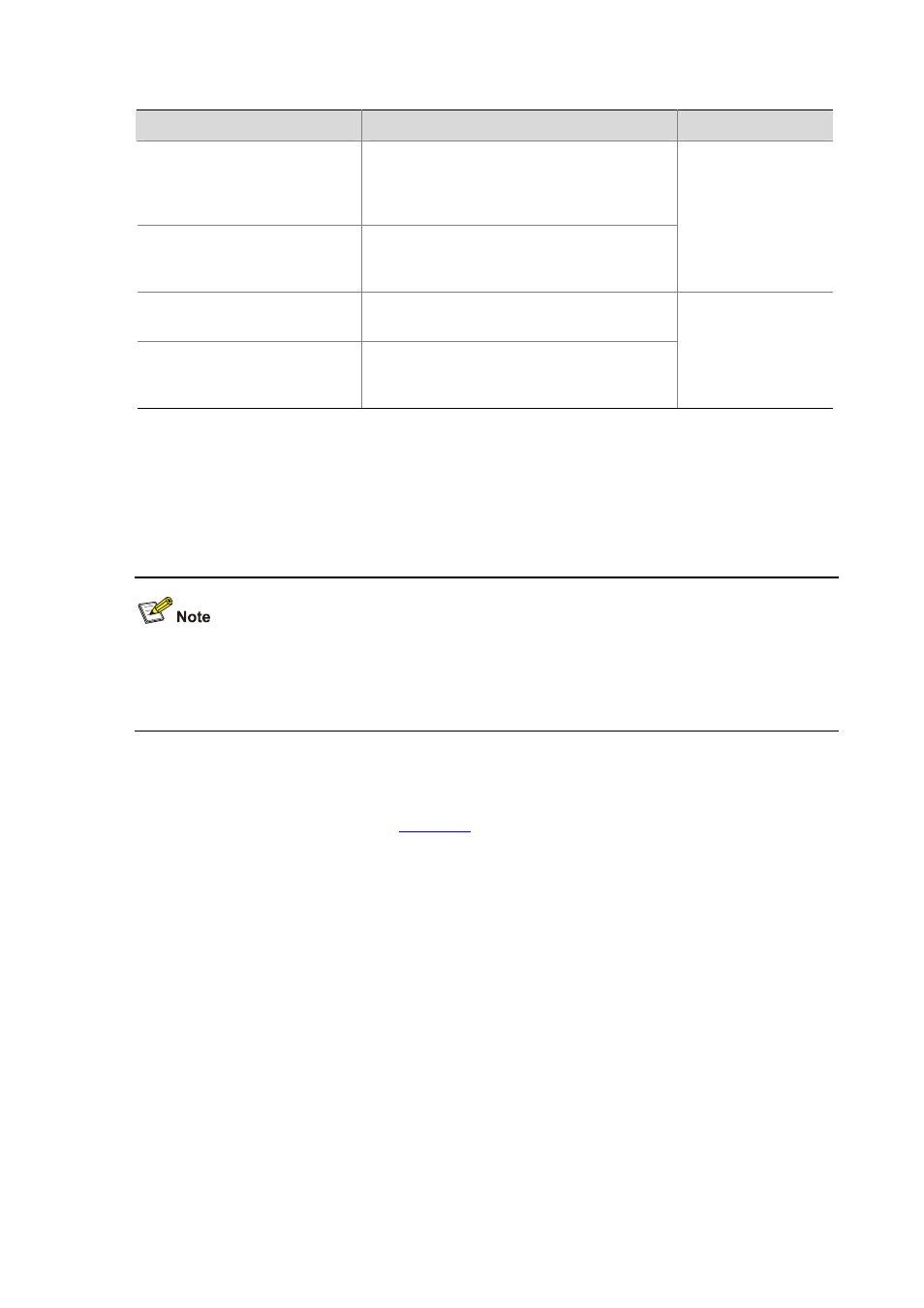
Displaying and Maintaining HWTACACS Protocol Configuration
To do…
Use the command…
Remarks
Display the configuration or
statistic information about one
specific or all HWTACACS
schemes
display hwtacacs
[ hwtacacs-scheme-name [ statistics ] ]
Display buffered
non-response
stop-accounting requests
display stop-accounting-buffer
{ hwtacacs-scheme
hwtacacs-scheme-name
Available in any
view
Clear HWTACACS message
statistics
reset hwtacacs statistics { accounting |
authentication | authorization | all }
Delete buffered non-response
stop-accounting requests
reset stop-accounting-buffer
hwtacacs-scheme
hwtacacs-scheme-name
Available in user
view
AAA Configuration Examples
Remote RADIUS Authentication of Telnet/SSH Users
The configuration procedure for remote authentication of SSH users by RADIUS server is similar to that
for Telnet users. The following text only takes Telnet users as example to describe the configuration
procedure for remote authentication.
Network requirements
In the network environment shown in
, you are required to configure the switch so that the
Telnet users logging into the switch are authenticated by the RADIUS server.
z
A RADIUS authentication server with IP address 10.110.91.164 is connected to the switch.
z
On the switch, set the shared key it uses to exchange messages with the authentication RADIUS
server to aabbcc.
z
A CAMS server is used as the RADIUS server. You can select extended as the server-type in a
RADIUS scheme.
z
On the RADIUS server, set the shared key it uses to exchange messages with the switch to
aabbcc, set the authentication port number, and add Telnet usernames and login passwords.
The Telnet usernames added to the RADIUS server must be in the format of userid@isp-name if you
have configured the switch to include domain names in the usernames to be sent to the RADIUS server
in the RADIUS scheme.
