Configuration procedure, Figure 41-15 – H3C Technologies H3C WX6000 Series Access Controllers User Manual
Page 483
41-14
The AC acquires CRLs for certificate verification.
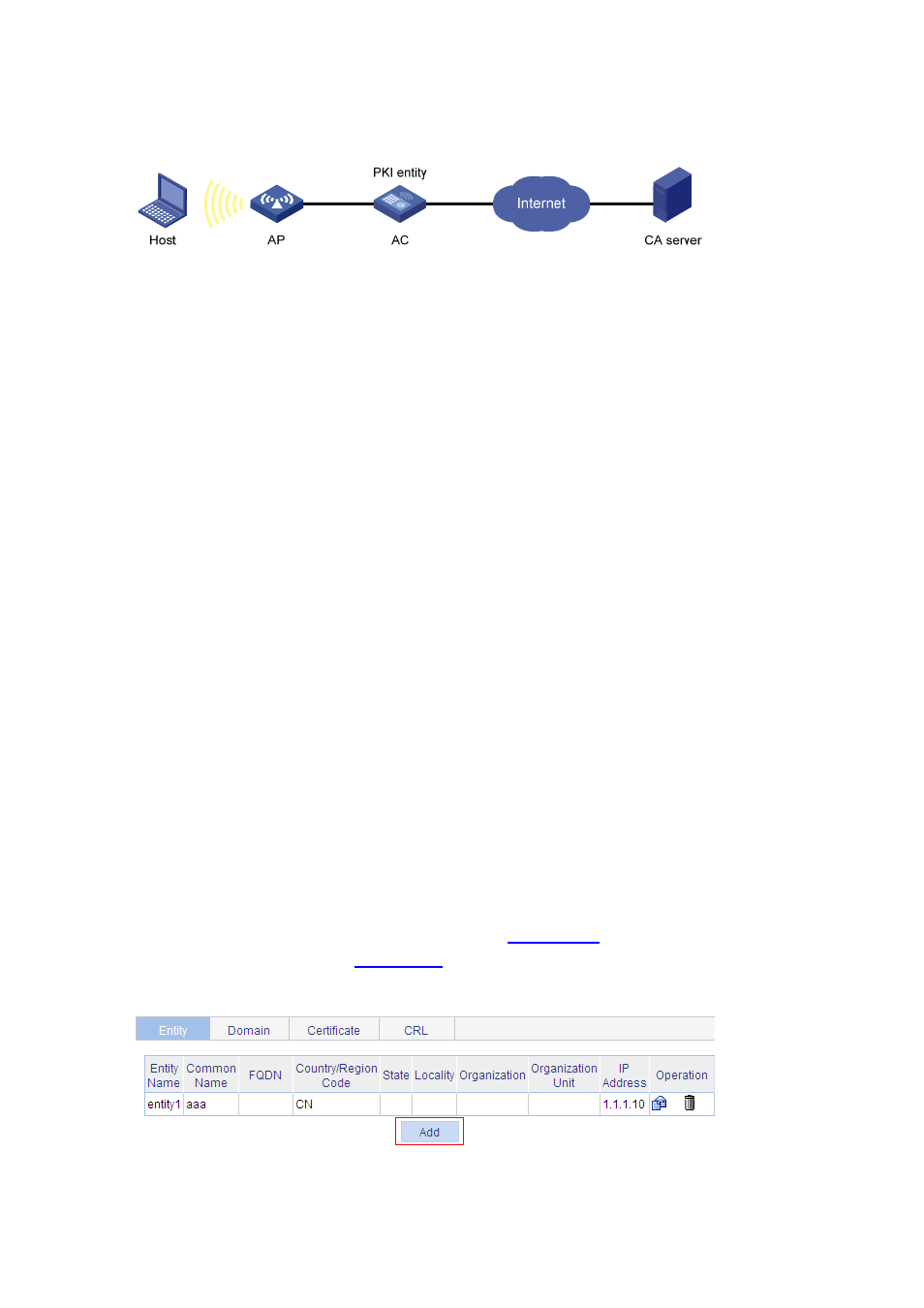
Figure 41-15 Network diagram for configuring a PKI entity to request a certificate from a CA
Configuration procedure
1) Configure the CA server
# Create a CA server named myca.
In this example, you need to configure the basic attributes of Nickname and Subject DN on the CA
server at first:
Nickname: Name of the trusted CA.
Subject DN: DN information of the CA, including the Common Name (CN),
Organization Unit (OU),
Organization (O), and
Country (C).
The other attributes may use the default values.
# Configure extended attributes
After configuring the basic attributes, you need to perform configuration on the Jurisdiction
Configuration page of the CA server. This includes selecting the proper extension profiles, enabling
the SCEP autovetting function, and adding the IP address list for SCEP autovetting.
# Configure the CRL publishing behavior
After completing the above configuration, you need to perform CRL related configurations.
In this example, select the local CRL publishing mode of HTTP and set the HTTP URL to
http://4.4.4.133:447/myca.crl.
After the above configuration, make sure that the system clock of the AC is synchronous to that of the
CA, so that the AC can request certificates and retrieve CRLs properly.
2) Configure
AC
# Create a PKI entity.
Select Authentication > PKI from the navigation tree. The PKI entity list page is displayed by
default. Click Add on the page, as shown in
, and then perform the following
.
Figure 41-16 PKI entity list
