Network requirements, Configuration procedure – H3C Technologies H3C SecPath F1000-E User Manual
Page 334
322
NOTE:
The configuration procedure covers only the configurations for IKE negotiation using RSA digital
signature. For an IPsec tunnel to be established, you also need to perform IPsec configurations. For more
information about IPsec configuration commands, see
VPN Command Reference.
Configuring a certificate attribute-based access control policy
Network requirements
•
The client accesses the remote HTTP Security (HTTPS) server through the HTTPS protocol.
•
Configure SSL to make sure that only legal clients log into the HTTPS server.
•
Create a certificate attribute-based access control policy to control access to the HTTPS server.
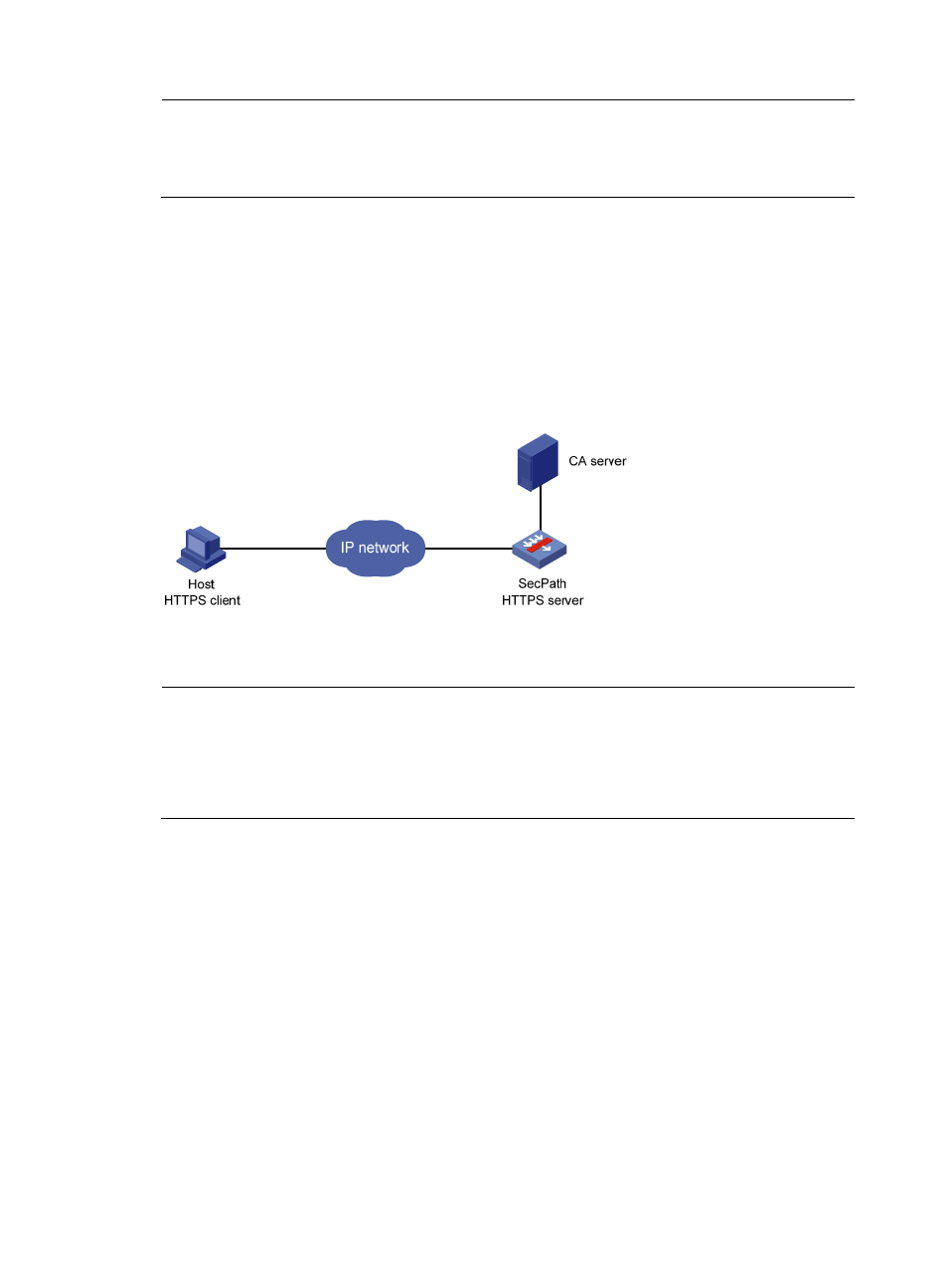
Figure 210 Network diagram
Configuration procedure
NOTE:
•
For more information about SSL configuration, see
Network Management Configuration Guide.
•
For more information about HTTPS configuration, see
Getting Started Guide.
•
The PKI domain to be referenced by the SSL policy must be created in advance. For how to configure a
PKI domain, see "
."
1.
Configure the HTTPS server:
# Configure the SSL policy for the HTTPS server to use.
[SecPath] ssl server-policy myssl
[SecPath-ssl-server-policy-myssl] pki-domain 1
[SecPath-ssl-server-policy-myssl] client-verify enable
[SecPath-ssl-server-policy-myssl] quit
2.
Configure the certificate attribute group:
# Create certificate attribute group mygroup1 and add two attribute rules. The first rule defines
that the DN of the subject name includes the string aabbcc, and the second rule defines that the IP
address of the certificate issuer is 10.0.0.1.
[SecPath] pki certificate attribute-group mygroup1
[SecPath-pki-cert-attribute-group-mygroup1] attribute 1 subject-name dn ctn aabbcc
[SecPath-pki-cert-attribute-group-mygroup1] attribute 2 issuer-name ip equ 10.0.0.1
[SecPath-pki-cert-attribute-group-mygroup1] quit
- H3C SecPath F5000-A5 Firewall H3C SecPath F1000-A-EI H3C SecPath F1000-E-SI H3C SecPath F1000-S-AI H3C SecPath F5000-S Firewall H3C SecPath F5000-C Firewall H3C SecPath F100-C-SI H3C SecPath F1000-C-SI H3C SecPath F100-A-SI H3C SecBlade FW Cards H3C SecBlade FW Enhanced Cards H3C SecPath U200-A U200-M U200-S H3C SecPath U200-CA U200-CM U200-CS
