Interlogix GE-DSSG-244-POE User Manual User Manual
Page 176
IFS NS3601-24P/4S GE-DSSG-244 and 244-POE User Manual
174
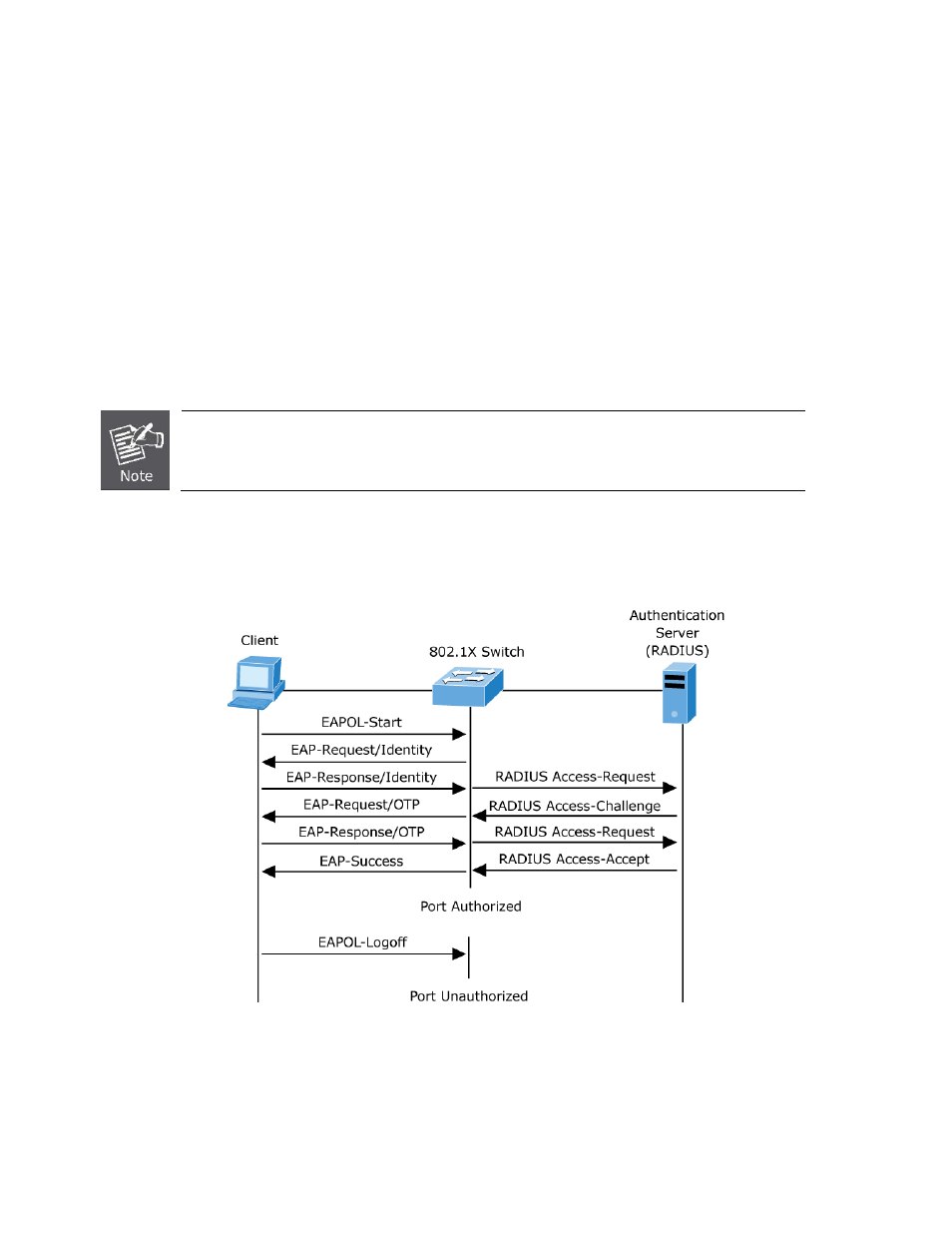
switch acts as an intermediary (proxy) between the client and the authentication server, requesting identity information from
the client, verifying that information with the authentication server, and relaying a response to the client. The switch includes
the RADIUS client, which is responsible for encapsulating and decapsulating the Extensible Authentication Protocol (EAP)
frames and interacting with the authentication server. When the switch receives EAPOL frames and relays them to the
authentication server, the Ethernet header is stripped and the remaining EAP frame is re-encapsulated in the RADIUS
format. The EAP frames are not modified or examined during encapsulation, and the authentication server must support
EAP within the native frame format. When the switch receives frames from the authentication server, the server's frame
header is removed, leaving the EAP frame, which is then encapsulated for Ethernet and sent to the client.
Authentication Initiation and Message Exchange
The switch or the client can initiate authentication. If you enable authentication on a port by using the dot1x port-control auto
interface configuration command, the switch must initiate authentication when it determines that the port link state transitions from
down to up. It then sends an EAP-request/identity frame to the client to request its identity (typically, the switch sends an initial
identity/request frame followed by one or more requests for authentication information). Upon receipt of the frame, the client
responds with an EAP-response/identity frame.
However, if during bootup, the client does not receive an EAP-request/identity frame from the switch, the client can initiate
authentication by sending an EAPOL-start frame, which prompts the switch to request the client's identity
If 802.1X is not enabled or supported on the network access device, any EAPOL frames from the
client are dropped. If the client does not receive an EAP-request/identity frame after three attempts
to start authentication, the client transmits frames as if the port is in the authorized state. A port in
the authorized state effectively means that the client has been successfully authenticated.
When the client supplies its identity, the switch begins its role as the intermediary, passing EAP frames between the client and the
authentication server until authentication succeeds or fails. If the authentication succeeds, the switch port becomes authorized.
The specific exchange of EAP frames depends on the authentication method being used. “
Figure 4-11-2
” shows a message
exchange initiated by the client using the One-Time-Password (OTP) authentication method with a RADIUS server.
Figure 4-11-2
EAP message exchange
Ports in Authorized and Unauthorized States
The switch port state determines whether or not the client is granted access to the network. The port starts in the unauthorized state.
While in this state, the port disallows all ingress and egress traffic except for 802.1X protocol packets. When a client is successfully
authenticated, the port transitions to the authorized state, allowing all traffic for the client to flow normally.
