Protecting configuration settings, Table 24, Encryption of configuration files – B&B Electronics WLNN-AN(ER,SE,SP.EK)-DP551 - Manual User Manual
Page 73: 0 protecting configuration settings
Airborne Enterprise CLI Reference Manual
73
12.0 Protecting Configuration Settings
Included in the module is the ability to protect sensitive configuration settings from prying
eyes. This is achieved through enabling the encryption of those parts of the configuration
that are considered sensitive. When enabled the sensitive settings like passwords,
passphrase and keys are removed from the displayed configurations and stored in a
separate encrypted file.
The default configuration for the module is to include all settings when the
user_config.txt file is viewed. In this case passwords, passphrases and WEP keys
are stored in plain text, in the configuration file. Although access to this file still requires
authentication to the module, once authenticated anyone can view the settings.
The encryption setting for the device removes the sensitive parameters for the
user_config.txt and places them in an encrypted file that cannot be directly viewed
even when fully authenticated to the module. The following table describes the settings
used to enable and disable the encryption of the sensitive settings; it also describes the
impacted parameters.
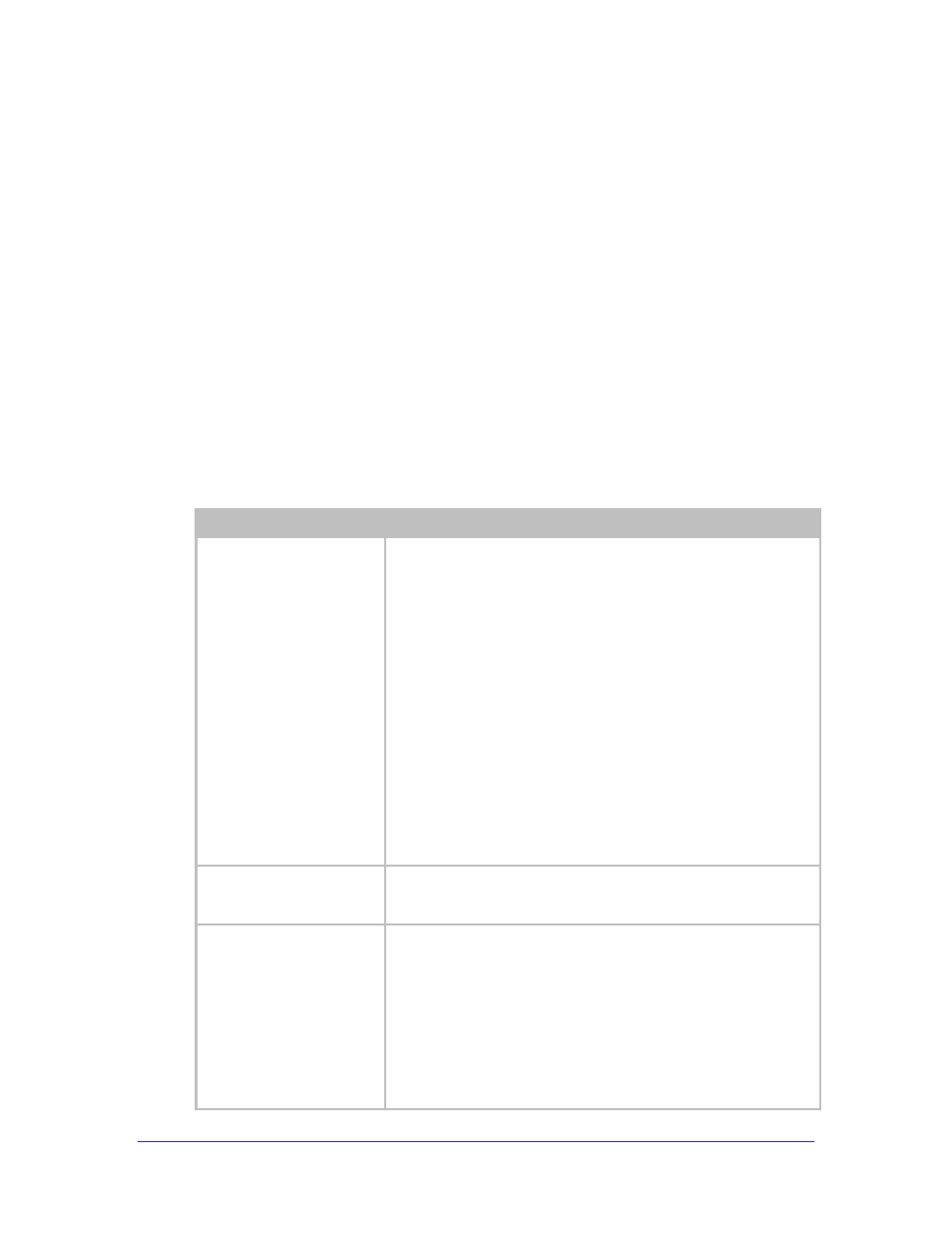
Table 24 - Encryption of Configuration Files
Command
Description
cfg-encrypt
[enable|disable|locked|
protected|permanent]
The command controls the securing of parameters in the
user_config.txt
file by removing them from the user_config.txt
and creating an encrypted file user_enc_config.uue that contain the
parameters.
When enable is selected the module will split the contents of the
unencrypted user_config.txt (if it exists) into two files by removing the
sensitive parameters that are present in the files into encrypted versions of
the file. These encrypted files will be visible when the configuration files
are listed by the list-cfg command but cannot be viewed in a plain text
editor. A full description of the parameters is shown in section 19.0.
The new file created is named user_enc_config.uue.
If disable is selected subsequent to enable being selected the contents
of the encrypted file are merged with the user_config.txt file and the
parameters in the encrypted file become visible in plain text. This is useful
for testing out the process and confirming the parameter encryption is
working.
When deploying in the field it is recommended that locked, protected
or permanent be used.
list-cfg
This command lists the configuration files available on the module. If cfg-
encrypt
is enabled the encrypted file (user_enc_config.uue) will be
listed in the response.
clear cfg-encrypt
Clears the state of the cfg-encrypt setting when one of the encrypted
option has been enabled. The resultant state of the module depends upon
the option applied.
If the state is locked, issuing the command will change the state of cfg-
encrypt
to enable. This is a Level 5 (manufacturer) command.
If the state is protected, issuing the command will change the state of
cfg-encrypt
to disable and will delete the user_enc_config.uue
file. This will remove all protected settings. This is a Level 5 (manufacturer)
command. Caution should be taken when using this option as it may impact
the user‟s ability to connect to the module.
