Definition of "weak encryption"(p. 35), Definition of "weak encryption – Canon imageCLASS MF753Cdw Multifunction Wireless Color Laser Printer User Manual
Page 45
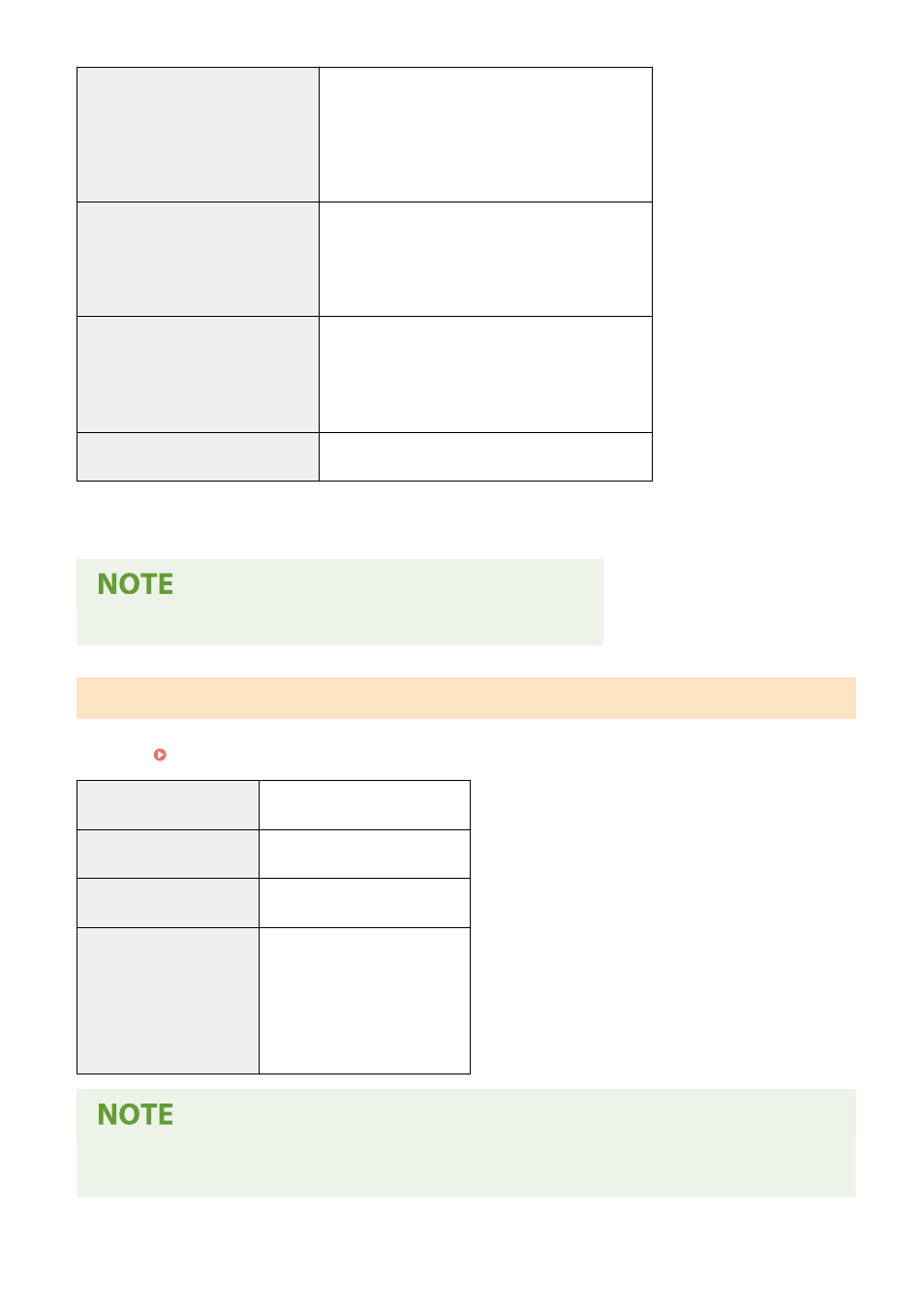
File extension
Key
".p12" or ".pfx"
CA certificate
".cer" or ".pem"
Public key algorithm (and key length) RSA (512 bits, 1024 bits, 2048 bits, 4096 bits)
DSA (1024 bits, 2048 bits, 3072 bits)
ECDSA (P256, P384, P521)
Certificate signature algorithm
RSA: SHA-1, SHA-256, SHA-384
*2
, SHA-512
*2
, MD2, MD5
DSA: SHA-1
ECDSA: SHA-1, SHA-256, SHA-384, SHA-512
Certificate thumbprint algorithm
SHA1
*1
Requirements for the certificate contained in a key are pursuant to CA certificates.
*2
SHA384-RSA and SHA512-RSA are available only when the RSA key length is 1024 bits or more.
●
The machine does not support use of a certificate revocation list (CRL).
Definition of "Weak Encryption"
When [Prohibit Use of Weak Encrypt.] in [Encryption Settings] is set to [On], the use of the following algorithms is
prohibited. [Encryption Settings](P. 575)
Hash
MD4, MD5, SHA-1
HMAC
HMAC-MD5
Common key encryption
RC2, RC4, DES
Public key encryption
RSA encryption (512 bits/1024 bits)
RSA signature (512 bits/1024 bits)
DSA (512 bits/1024 bits)
DH (512 bits/1024 bits)
●
Even when [Prohibit Weak Encryp. Key/Cert.] in [Encryption Settings] is set to [On], the hash algorithm
SHA-1, which is used for signing a root certificate, can be used.
About the Machine
35
