Configuring ssh2.0, Overview, How does ssh work – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 302: Version negotiation
288
Configuring SSH2.0
Overview
Secure Shell (SSH) offers an approach to logging in to a remote device securely. Using encryption and
strong authentication, SSH protects devices against attacks such as IP spoofing and plain text password
interception.
The access controller can not only work as an SSH server to support connections with SSH clients, but
also work as an SSH client to allow users to establish SSH connections with a remote device acting as the
SSH server. When acting as an SSH server, the access controller supports SSH2.0 and SSH1. When
acting as an SSH client, the access controller supports SSH2.0 only.
Unless otherwise noted, SSH in this document refers to SSH2.0.
How does SSH work
To establish an SSH connection and communicate with each other through the connection, an SSH client
and the SSH server go through the stages listed in
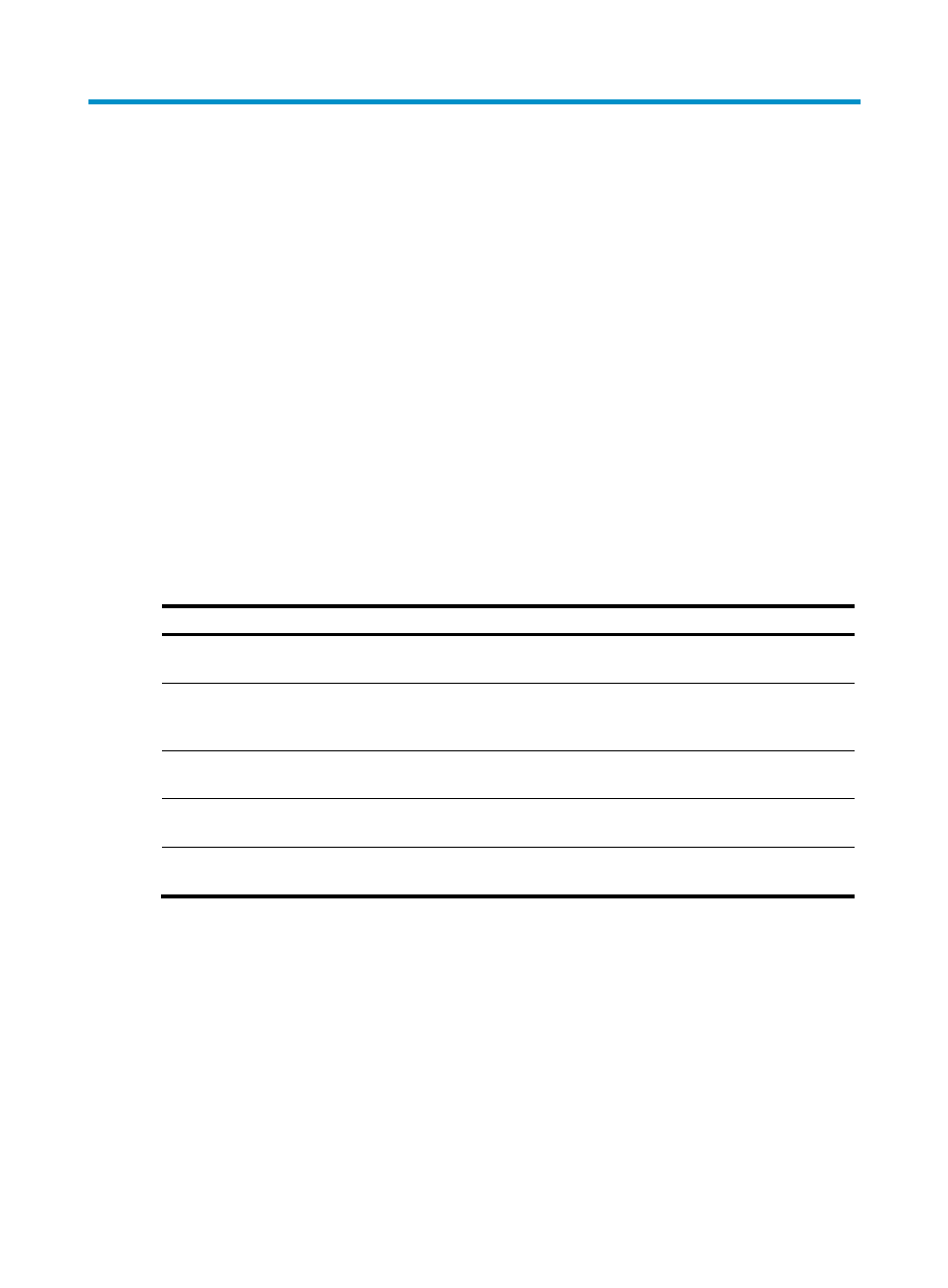
Table 13 Stages in session establishment and interaction between an SSH client and the server
Stages Description
SSH1 and SSH2.0 are supported. The two parties negotiate a version to
use.
SSH supports multiple algorithms. The two parties negotiate algorithms
for communication, and use the DH key exchange algorithm to generate
the same session key and session ID.
The SSH server authenticates the client in response to the client's
authentication request.
After passing authentication, the client sends a session request to the
server.
After the server grants the request, the client and the server start to
communicate with each other.
Version negotiation
1.
The server opens port 22 to listen to connection requests from clients.
2.
The client sends a TCP connection request to the server.
3.
After the TCP connection is established, the server sends a packet that carries a version information number>. secondary protocol version numbers constitute the protocol version number. The software version 4. After receiving the packet, the client resolves the packet and compares the server's protocol client uses the protocol version of the server; otherwise, the client uses its own protocol version. In
string to the client. The version information string is in the format SSH-
number is used for debugging.
version number with that of its own. If the server's protocol version is lower and supportable, the
- H3C WX5500E Series Access Controllers H3C WX3500E Series Access Controllers H3C WX2500E Series Access Controllers H3C WX6000 Series Access Controllers H3C WX5000 Series Access Controllers H3C LSWM1WCM10 Access Controller Module H3C LSUM3WCMD0 Access Controller Module H3C LSUM1WCME0 Access Controller Module H3C LSWM1WCM20 Access Controller Module H3C LSQM1WCMB0 Access Controller Module H3C LSRM1WCM2A1 Access Controller Module H3C LSBM1WCM2A0 Access Controller Module H3C WA3600 Series Access Points H3C WA2600 Series WLAN Access Points H3C S10500 Series Switches H3C S5800 Series Switches H3C S5820X Series Switches H3C S12500 Series Switches H3C S9500E Series Switches H3C MSR 5600 H3C MSR 50 H3C MSR 3600 H3C MSR 30 H3C MSR 2600 H3C MSR 20-2X[40] H3C MSR 20-1X H3C MSR 930 H3C MSR 900 H3C SR8800 H3C SR6600-X H3C SR6600 H3C SecPath F5020 H3C SecPath F5040 H3C VMSG VFW1000
