Managing public keys, Asymmetric key algorithm overview, Basic concepts – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 273: Key algorithm types, Asymmetric key algorithm applications
259
Managing public keys
Asymmetric key algorithm overview
Basic concepts
•
Algorithm: A set of transformation rules for encryption and decryption.
•
Plain text: Information without being encrypted.
•
Cipher text: Encrypted information.
•
Key: A string of characters that controls the transformation between plain text and cipher text. It is
used in both the encryption and decryption.
Key algorithm types
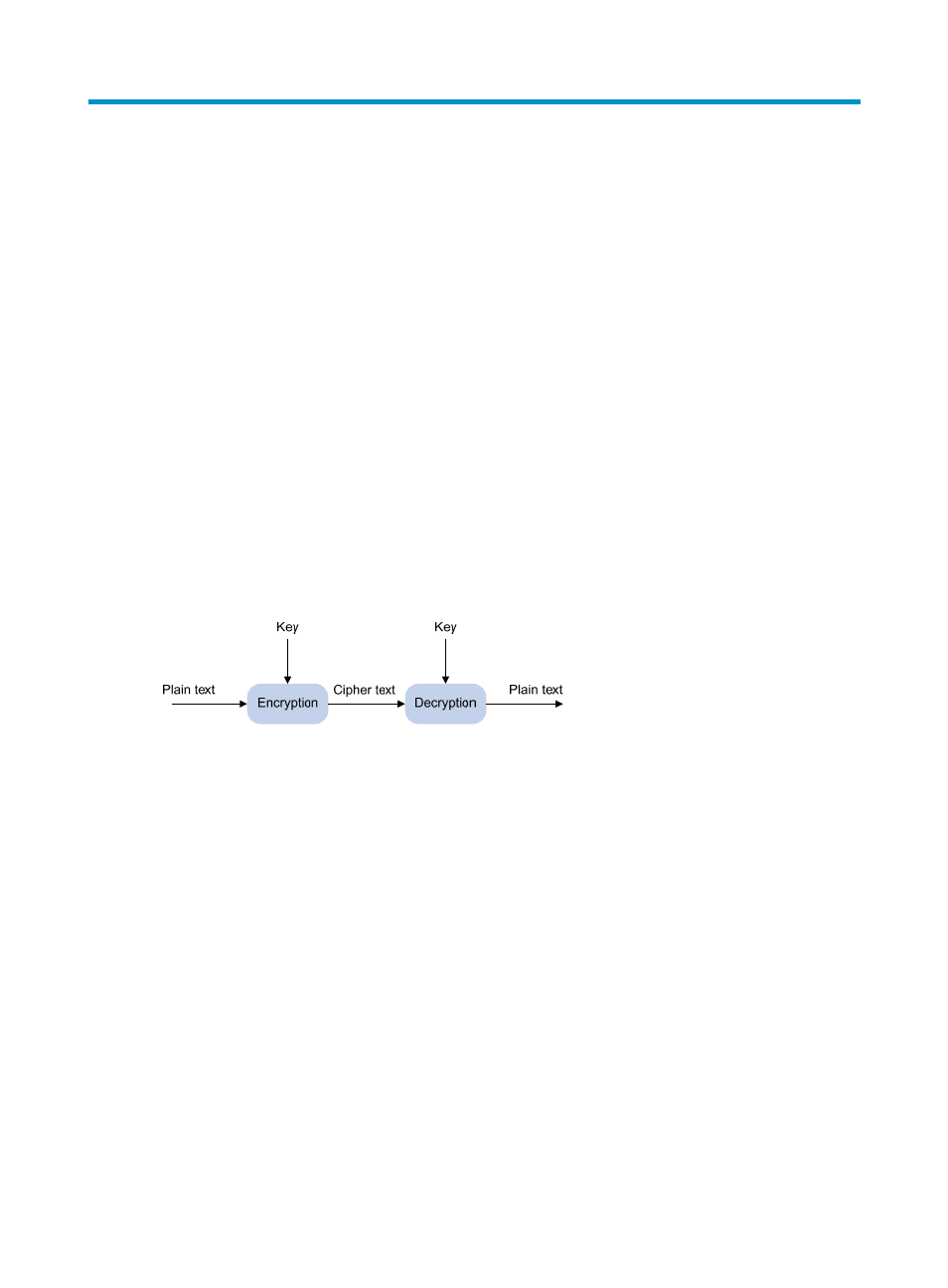
As shown in
, the information in plain text is encrypted by an algorithm with the help of a key
before being sent. The resulting cipher text is transmitted across the network to the receiver, where it is
decrypted by the same algorithm also with the help of a key to obtain the original plain text.
Figure 119 Encryption and decryption
The following types of key algorithms are available, based on whether the keys for encryption and
decryption are the same:
•
Symmetric key algorithm—The keys for encryption and decryption are the same. Commonly used
symmetric key algorithms include Advanced Encryption Standard (AES) and Data Encryption
Standard (DES).
•
Asymmetric key algorithm—The keys for encryption and decryption are different, one is the public
key, and the other is the private key. The information encrypted with the public key can only be
decrypted with the corresponding private key, and vice versa. The private key is kept secret, and the
public key may be distributed widely. The private key cannot be practically derived from the public
key.
Asymmetric key algorithm applications
Asymmetric key algorithms can be used for encryption and digital signature.
•
Encryption—The sender uses the public key of the intended receiver to encrypt the information to be
sent. Only the intended receiver, the holder of the paired private key, can decrypt the information.
This mechanism guarantees confidentiality.
- H3C WX5500E Series Access Controllers H3C WX3500E Series Access Controllers H3C WX2500E Series Access Controllers H3C WX6000 Series Access Controllers H3C WX5000 Series Access Controllers H3C LSWM1WCM10 Access Controller Module H3C LSUM3WCMD0 Access Controller Module H3C LSUM1WCME0 Access Controller Module H3C LSWM1WCM20 Access Controller Module H3C LSQM1WCMB0 Access Controller Module H3C LSRM1WCM2A1 Access Controller Module H3C LSBM1WCM2A0 Access Controller Module H3C WA3600 Series Access Points H3C WA2600 Series WLAN Access Points H3C S10500 Series Switches H3C S5800 Series Switches H3C S5820X Series Switches H3C S12500 Series Switches H3C S9500E Series Switches H3C MSR 5600 H3C MSR 50 H3C MSR 3600 H3C MSR 30 H3C MSR 2600 H3C MSR 20-2X[40] H3C MSR 20-1X H3C MSR 930 H3C MSR 900 H3C SR8800 H3C SR6600-X H3C SR6600 H3C SecPath F5020 H3C SecPath F5040 H3C VMSG VFW1000
