Hwtacacs, Differences between hwtacacs and radius, Basic hwtacacs message exchange process – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 21
7
Figure 5 Segment of a RADIUS packet containing an extended attribute
HWTACACS
HW Terminal Access Controller Access Control System (HWTACACS) is an enhanced security protocol
based on TACACS (RFC 1492). Similar to RADIUS, it uses a client/server model for information
exchange between the NAS and the HWTACACS server.
HWTACACS mainly provides AAA services for Point-to-Point Protocol (PPP) users, Virtual Private Dial-up
Network (VPDN) users, and terminal users. In a typical HWTACACS scenario, some terminal users need
to log in to the NAS for operations. Working as the HWTACACS client, the NAS sends the usernames
and passwords of the users to the HWTACACS sever for authentication. After passing authentication and
being authorized, the users log in to the device and performs operations, and the HWTACACS server
records the operations that each user performs.
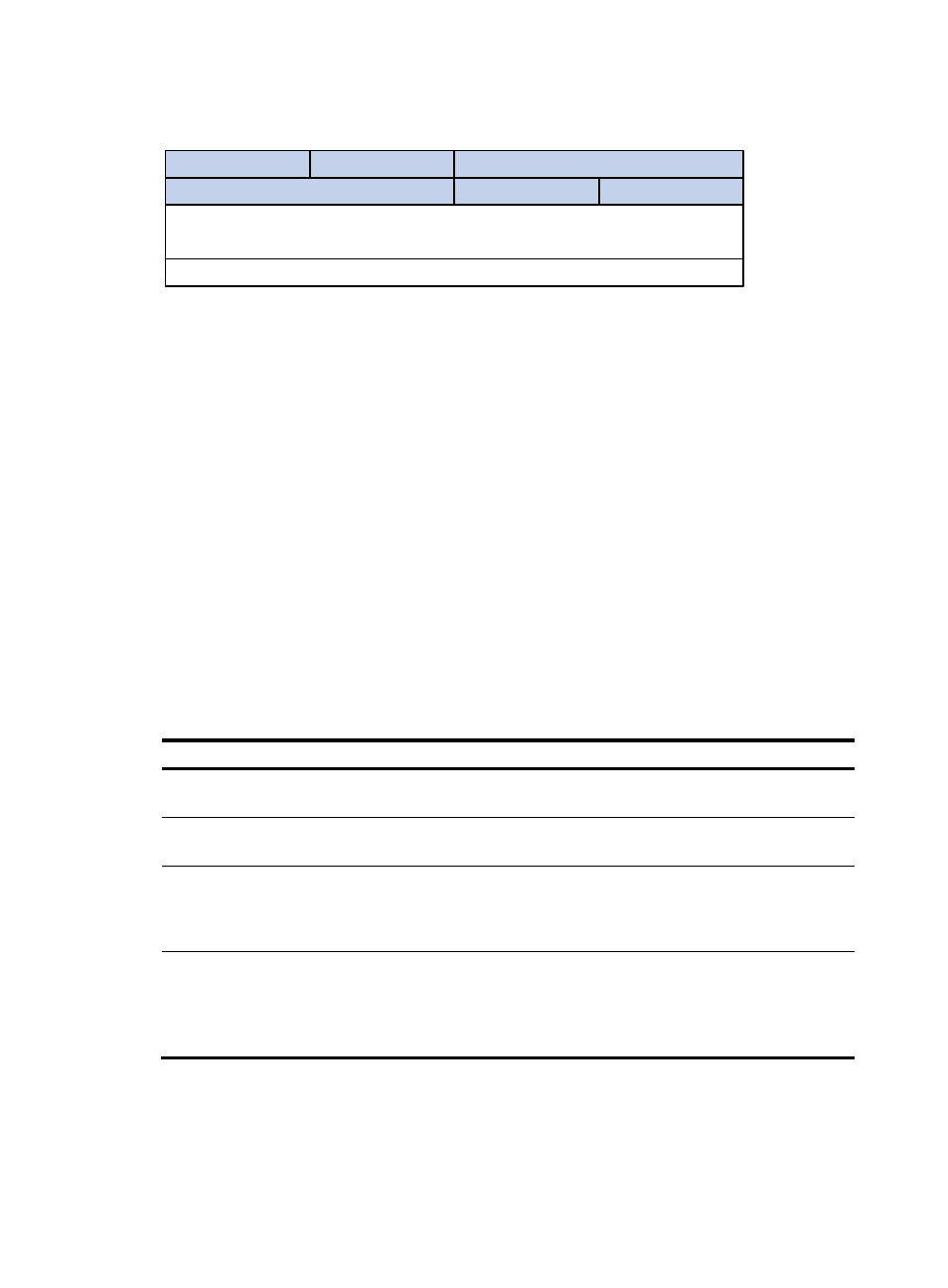
Differences between HWTACACS and RADIUS
HWTACACS and RADIUS both provide authentication, authorization, and accounting services. They
have many features in common, like using a client/server model, using shared keys for user information
security, and providing flexibility and extensibility. HWTACACS and RADIUS do have differences, as
listed in
.
Table 3 Primary differences between HWTACACS and RADIUS
HWTACACS RADIUS
Uses TCP, providing more reliable network
transmission.
Uses UDP, providing higher transport efficiency.
Encrypts the entire packet except for the HWTACACS
header.
Encrypts only the user password field in an
authentication packet.
Protocol packets are complicated and authorization is
independent of authentication. Authentication and
authorization can be deployed on different
HWTACACS servers.
Protocol packets are simple and the authorization
process is combined with the authentication process.
Supports authorization of configuration commands.
Which commands a user can use depends on both the
user level and AAA authorization. A user can use only
commands that are not only of, or lower than, the user
level but also authorized by the HWTACACS server.
Does not support authorization of configuration
commands. Which commands a user can use
depends on the level of the user and a user can use all
the commands of, or lower than, the user level.
Basic HWTACACS message exchange process
The following example describes how HWTACACS performs authentication, authorization, and
accounting for a Telnet user.
Type
Length
0
Vendor-ID
7
15
31
Vendor-ID (continued)
Vendor-Type
Vendor-Length
Vendor-Data
(Specified attribute value……)
23
……
- H3C WX5500E Series Access Controllers H3C WX3500E Series Access Controllers H3C WX2500E Series Access Controllers H3C WX6000 Series Access Controllers H3C WX5000 Series Access Controllers H3C LSWM1WCM10 Access Controller Module H3C LSUM3WCMD0 Access Controller Module H3C LSUM1WCME0 Access Controller Module H3C LSWM1WCM20 Access Controller Module H3C LSQM1WCMB0 Access Controller Module H3C LSRM1WCM2A1 Access Controller Module H3C LSBM1WCM2A0 Access Controller Module H3C WA3600 Series Access Points H3C WA2600 Series WLAN Access Points H3C S10500 Series Switches H3C S5800 Series Switches H3C S5820X Series Switches H3C S12500 Series Switches H3C S9500E Series Switches H3C MSR 5600 H3C MSR 50 H3C MSR 3600 H3C MSR 30 H3C MSR 2600 H3C MSR 20-2X[40] H3C MSR 20-1X H3C MSR 930 H3C MSR 900 H3C SR8800 H3C SR6600-X H3C SR6600 H3C SecPath F5020 H3C SecPath F5040 H3C VMSG VFW1000
