H3C Technologies H3C Intelligent Management Center User Manual
Page 205
187
{
Modify Password at Next Login—Requires that the access user must change the password the
next time the user passes authentication. This option can be configured only when the Enable
Password Strategy option is selected. After the access user changes the password, this
parameter is automatically unselected.
{
Validity Time—Enter the date and time when the access user becomes valid. Leave this field
empty if you want the access user to become valid immediately after being created.
{
Expiration Time—Enter the date and time when the access user expires and becomes invalid.
An empty field indicates that the access user never expires.
{
Max. Idle Time—Enter the maximum idle time permitted for an online user. When the time
expires, the user is forcibly logged off. An empty field indicates that the access user can always
be online without performing any operations.
{
Max. Smart Device Bindings for Portal—Select the maximum number of device MAC addresses
that can be bound to the access user account or select Not Supported from the list. Not
Supported indicates the account does not support transparent portal authentication.
{
Login Message—Enter the message that the access user sees when the user passes
authentication.
{
Max. Concurrent Logins—Enter the maximum number of concurrent online users for the account.
An empty field indicates no restriction on the number of concurrent online users using the
account.
{
WLAN Cell Phone Number/WLAN Password/Confirm Password—Phone number and
password to which the access user is bound. These fields appear only when Third-Party System
Authentication is enabled in the UAM system settings. When this function is enabled, UAM
sends the phone number and password for second authentication by the third-party
authentication system. For more information about third-party system authentication, see
"
Configuring the third-party authentication system
." For more information about phone number
configuration restrictions, see "
Configuring the cell phone number ranges
5.
Configure the access services.
When Apply for Service by User Group is enabled, UAM hides this area and automatically
assigns services of each user group to their respective users. For information about configuring
Apply for Service by User Group, see "
32 Configuring global system settings
."
Select the access services on the access service list. You can select multiple services with different
suffixes for the access user.
The access service list contains the following parameters:
{
Service Name—Name of the access service, which must be unique in UAM.
{
Service Suffix—Identifies the name of the domain to be used for endpoint user authentication.
For more information, see
. The username and service suffix entered for user
authentication are closely related to the domain where the access device authenticates the user.
{
Allocate IP—IP address that the access service allocates to the user. An empty field indicates that
the access service does not allocate any IP address.
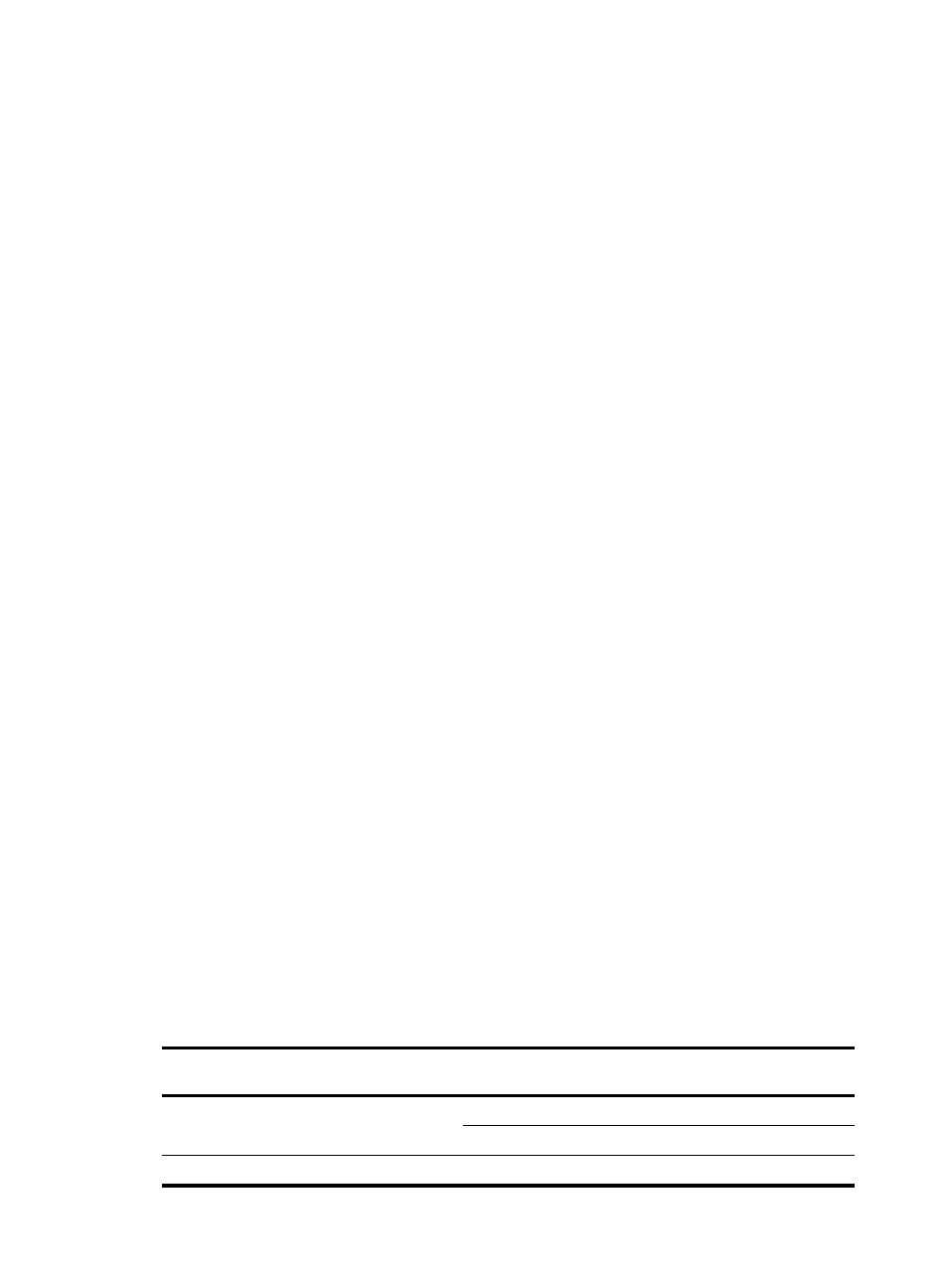
Table 20 Service suffix and other configurations
Authentication
username
Authentication domain
on the access device
Commands configured on the
access device
Service suffix in
UAM
X@Y Y
user-name-format with-domain
Y
user-name-format without-domain
None
X [Default
Domain]
user-name-format with-domain
[Default Domain]
