Uam user types, Uam access control settings, Authorization – H3C Technologies H3C Intelligent Management Center User Manual
Page 20
2
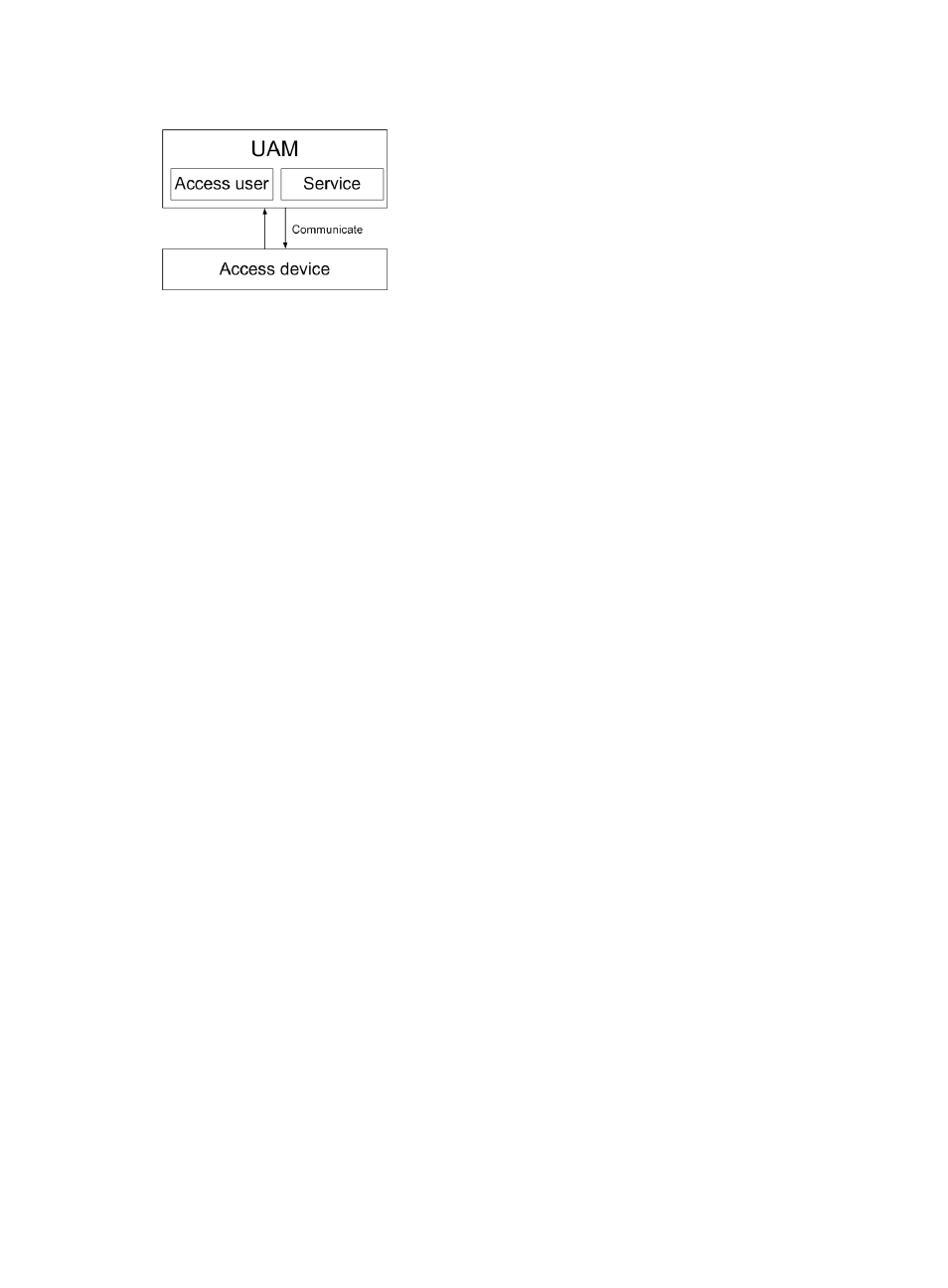
Figure 1 UAM functional structure
UAM user types
To satisfy access requirements in different scenarios, UAM contains the following user types:
•
Normal access users—Uses an account name-password or certificate to pass identity
authentication. UAM saves and maintains user access information.
•
Mute terminal users—Refers to a network terminal without an authentication operating interface,
such as an IP phone and a printer. A mute terminal uses its MAC address for identity authentication.
•
LDAP users—UAM users who are bound with an LDAP server. When UAM receives an
authentication request from such a user, it delivers the username and password to the LDAP server
for identity authentication. LDAP user information is saved in both the LDAP server and the UAM
server. The LDAP server maintains user information. UAM periodically synchronizes user
information with the LDAP server.
If a network already uses an LDAP server to manage users, HP recommends using LDAP users
when you deploy the UAM system to the network.
•
Guests—Refers to a user who needs to access the network. In UAM, you can specify a normal user
as a guest administrator, who can add guest users and process the preregistration requests for guest
users.
•
Device management users—Manages network devices. When a device management user logs in
to a network device through Telnet or SSH, UAM authenticates the user's account and password.
UAM supports only RADIUS authentication for device management users. After a device
management user passes authentication, UAM assigns corresponding management rights to the
user, and then the user can manage and maintain the network device.
UAM access control settings
Access control policies are used in UAM services to control user access behaviors and avoid insecure
user access. Access control policy categories include authorization, binding, and access area control.
Authorization
Authorization for users includes the following:
•
Control user access time—UAM lets you define time ranges during which users can or cannot
access the network. To implement time-range based network access, specify different access time
ranges for different users.
