Device and user level background information, Device and user level background information 173, Configuring authentication database location 205 – Enterasys Networks CSX6000 User Manual
Page 173
Central Site Remote Access Switch 173
C
ONFIGURING
S
ECURITY
L
EVEL
Device and User Level Security
D
EVICE
AND
U
SER
L
EVEL
B
ACKGROUND
I
NFORMATION
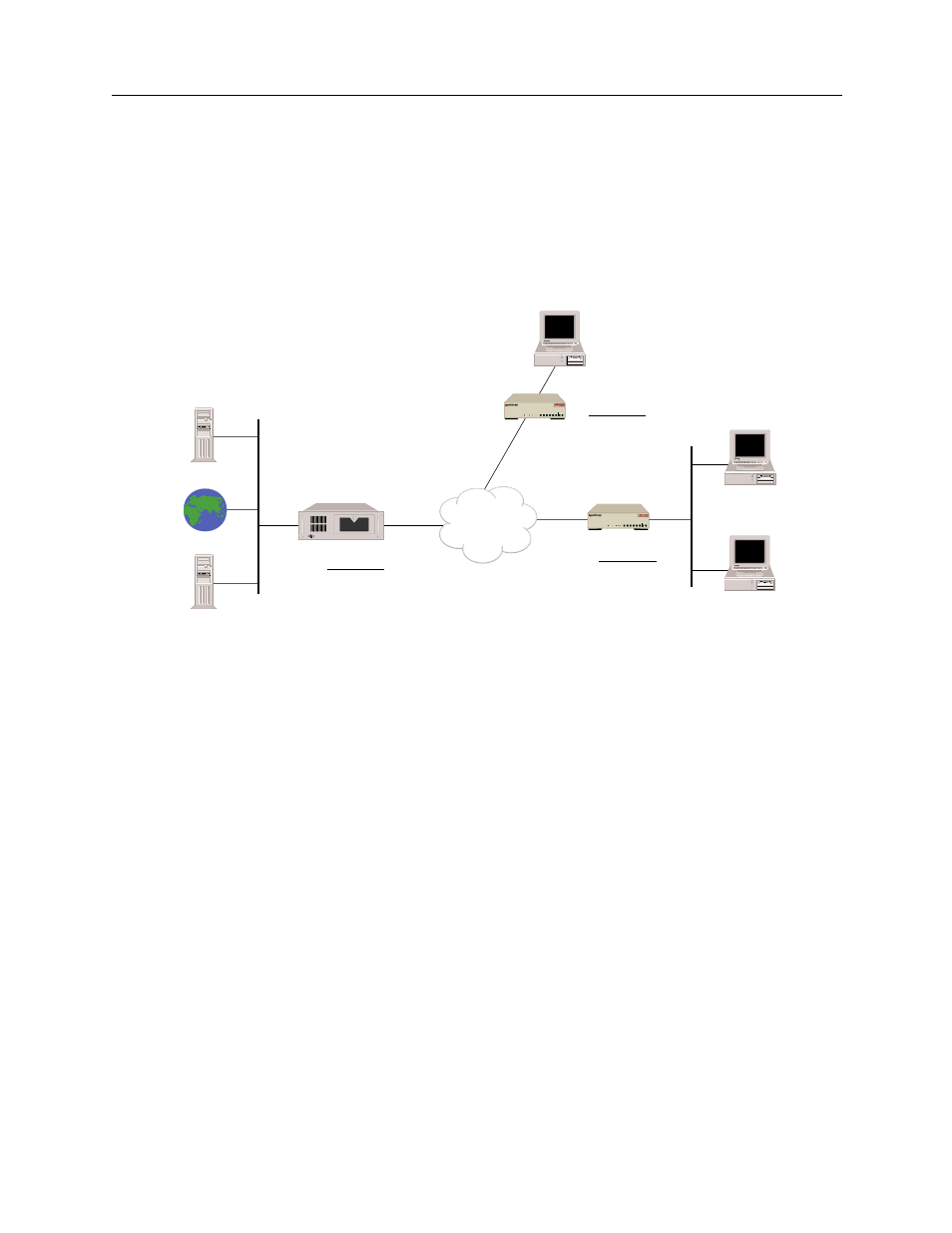
Multi-level security (device and user level) provides you with increased security options for your
network. This feature supports device level security for all remote devices. User-level
authentication can be performed on top of device level authentication for IP, IPX, AppleTalk and
bridge users. Only users configured for user level authentication will be required to do so. Refer to
the following illustration of a sample IP network configured for multilevel security.
The network security level has been configured for both device level and user level security.
Certain remote devices, such as Ollie, are able to dial-in and are only authenticated at the device
level. However, remote devices, such as Sparky, are configured in the device level database to be
authenticated at the user level as well as at the device level.
For example, Scally is using the PC on the LAN attached to Sparky, a CSX1200. Scally needs to
download some files off of the Service Server, which is on the LAN connecting to Zoe, a CSX5500.
Upon initiation of Scally’s call, device level authentication begins. Zoe checks its on-node device
database to see if Sparky is a valid device, and whether its IP address and password are also valid.
If valid, Zoe allows the connection, however a data filter is placed on the connection. This filter only
allows Telnet session traffic to flow over the connection between Zoe and Sparky. User level
authentication begins when Scally telnets to the IP address 1.1.1.1, port 7003, which is the port
assigned to the ACE server. Zoe sends the user level login prompt to Scally’s PC. Once Scally
completes the login and password information, Zoe relays this data to the ACE Server. If Scally is
a valid user in the ACE database and provides the correct login and password, Zoe removes the
restrictive filter so he may access the Service Server, or any other system on that LAN. Now that
Scally has been properly authenticated, any users on his LAN may access the systems attached to
Zoe. For example, while Scally is downloading files, Simon could boot up his PC and access the
Internet without going through the authentication process.
ISDN
Ace Server
Internet
Service
Server
CSX5500
1.1.1.1
sys name: Zoe
1.1.1.2
Device Table
name: Sparky
name: Ollie
CSX1200
sys name: Sparky
Device Table
name: Zoe
CSX1200
sys name: Ollie
Device Table
name: Zoe
Scally
PC
PC
Simon
PC
B25 B27
B26 B28
WORKGROUP REMOTE ACCESS SWITCH
B29
E1 ONLY
B-CHANNELS
LAN
10BASE-T
RX
TX
SERVICE
B31
B30 L1
B21 B23
B22 B24
B17 B19
B18 B20
B13 B15
B14 B16
E1
D
T1
D
B9
B11
B10 B12
B5
B7
B6
B8
B1
B3
B2
B4
POWER
B25 B27
B26 B28
WORKGROUP REMOTE ACCESS SWITCH
B29
E1 ONLY
B-CHANNELS
LAN
10BASE-T
RX
TX
SERVICE
B31
B30 L1
B21 B23
B22 B24
B17 B19
B18 B20
B13 B15
B14 B16
E1
D
T1
D
B9
B11
B10 B12
B5
B7
B6
B8
B1
B3
B2
B4
POWER
