Appendix b: idp signature groups, B. idp signature groups – Amer Networks E5Web GUI User Manual
Page 751
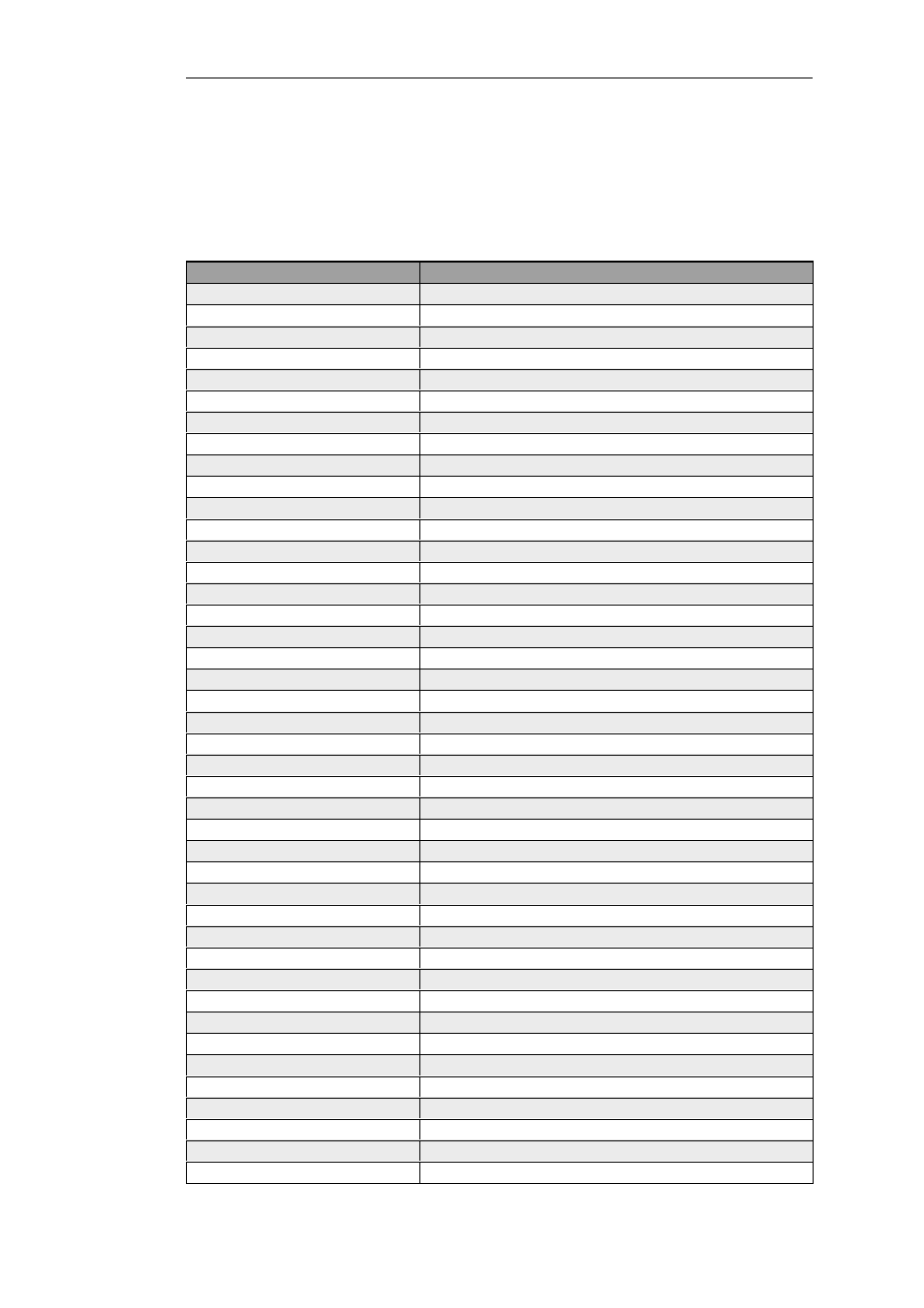
Appendix B: IDP Signature Groups
For IDP scanning, the following signature groups are available for selection. There is a version of
each group under the three Types of IDS, IPS and Policy. For further information see Section 6.5,
“Intrusion Detection and Prevention”.
Group Name
Intrusion Type
APP_AMANDA
Amanda, a popular backup software
APP_ETHEREAL
Ethereal
APP_ITUNES
Apple iTunes player
APP_REALPLAYER
Media player from RealNetworks
APP_REALSERVER
RealNetworks RealServer player
APP_WINAMP
WinAMP
APP_WMP
MS Windows Media Player
AUTHENTICATION_GENERAL
Authenticantion
AUTHENTICATION_KERBEROS
Kerberos
AUTHENTICATION_XTACACS
XTACACS
BACKUP_ARKEIA
Network backup solution
BACKUP_BRIGHTSTOR
Backup solutions from CA
BACKUP_GENERAL
General backup solutions
BACKUP_NETVAULT
NetVault Backup solution
BACKUP_VERITAS
Backup solutions
BOT_GENERAL
Activities related to bots, including those controlled by IRC channels
BROWSER_FIREFOX
Mozilla Firefox
BROWSER_GENERAL
General attacks targeting web browsers/clients
BROWSER_IE
Microsoft IE
BROWSER_MOZILLA
Mozilla Browser
COMPONENT_ENCODER
Encoders, as part of an attack.
COMPONENT_INFECTION
Infection, as part of an attack
COMPONENT_SHELLCODE
Shell code, as part of the attacks
DB_GENERAL
Database systems
DB_MSSQL
MS SQL Server
DB_MYSQL
MySQL DBMS
DB_ORACLE
Oracle DBMS
DB_SYBASE
Sybase server
DCOM_GENERAL
MS DCOM
DHCP_CLIENT
DHCP Client related activities
DHCP_GENERAL
DHCP protocol
DHCP_SERVER
DHCP Server related activities
DNS_EXPLOIT
DNS attacks
DNS_GENERAL
Domain Name Systems
DNS_OVERFLOW
DNS overflow attack
DNS_QUERY
Query related attacks
ECHO_GENERAL
Echo protocol and implementations
ECHO_OVERFLOW
Echo buffer overflow
FINGER_BACKDOOR
Finger backdoor
FINGER_GENERAL
Finger protocol and implementation
FINGER_OVERFLOW
Overflow for Finger protocol/implementation
FS_AFS
Andrew File System
751
