Anti-virus malicious file message, Anti-virus malicious url message – Amer Networks E5Web GUI User Manual
Page 463
and can determine, with a high degree of certainty, if a virus is in the process of being
downloaded to a user behind the Clavister Security Gateway. Once a virus is recognized in the
contents of a file, the download can be terminated before it completes.
Types of Data Scanned
As described above, anti-virus scanning is enabled on a per ALG basis and can scan data
downloads associated with the HTTP, FTP, SMTP and POP3 ALGs. More specifically:
•
Any uncompressed file type transferred through these ALGs can be scanned.
•
If the download has been compressed, ZIP and GZIP file downloads can be scanned.
•
For the HTTP ALG, webpage scripts and URLs are scanned.
Messages displayed by the HTTP ALG
If enabled through the HTTP ALG, webpage scripts and URLs as well as files can be scanned for
malicious code. If a threat is encounted, the connection is dropped and cOS Core will generate a
log message for the event. HTTPS traffic cannot be scanned so this does not apply for that
protocol.
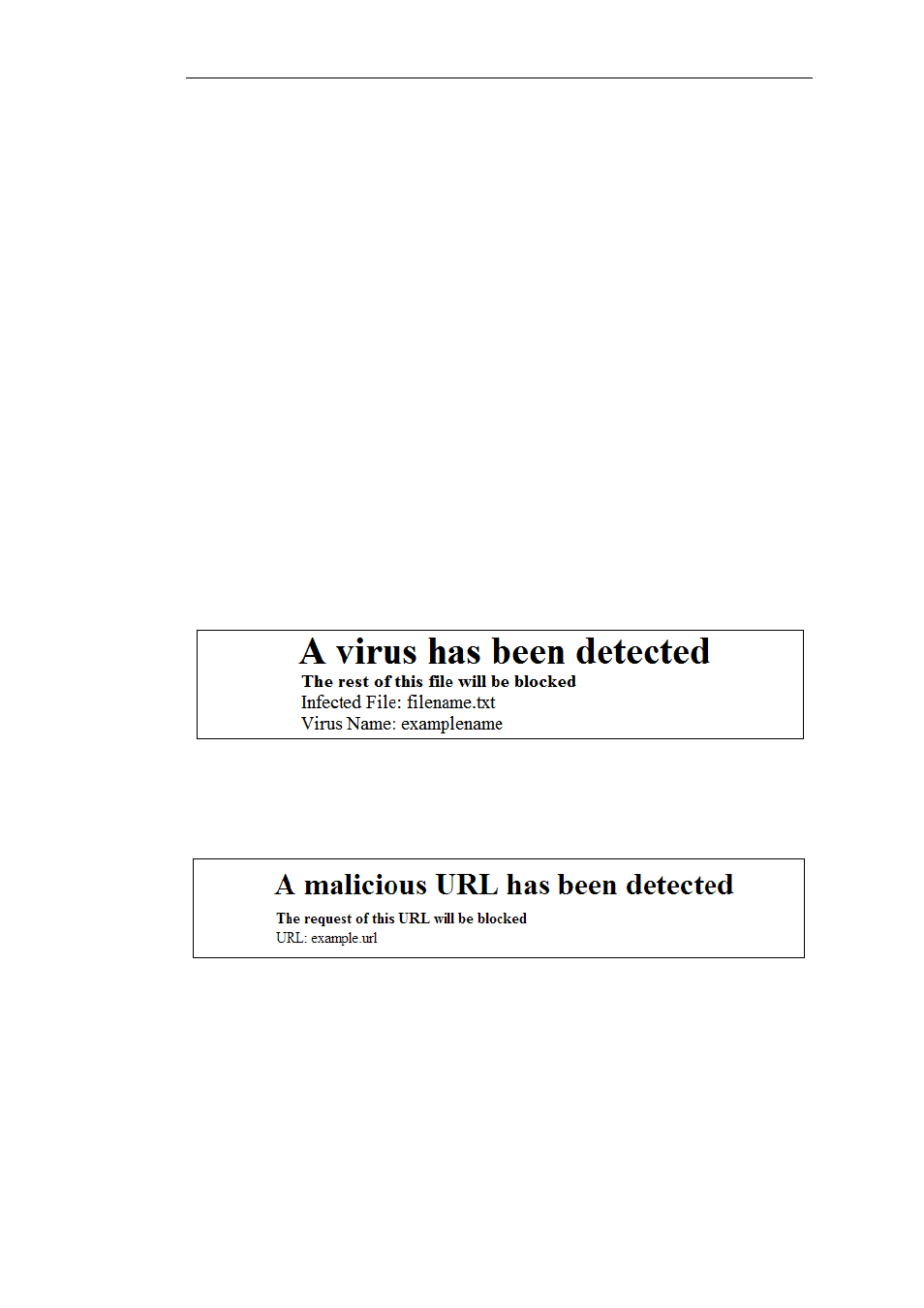
As well as the connection being dropped, cOS Core will try to insert a message into the web
browser HTML of the affected user indicating the action taken (in some cases it might not be
possible to do this successfully). For malicious files and scripts, the following is an example of an
inserted message:
Figure 6.9. Anti-Virus Malicious File Message
For malicious URLs, the message displayed will be similar to the following:
Figure 6.10. Anti-Virus Malicious URL Message
Simultaneous Scans
There is no fixed limit on how many anti-virus scans can take place simultaneously in a single
Clavister Security Gateway. However, the available free memory can place a limit on the number
of concurrent scans that can be initiated.
Chapter 6: Security Mechanisms
463
