Vpn encryption – Amer Networks E5Web GUI User Manual
Page 566
2.
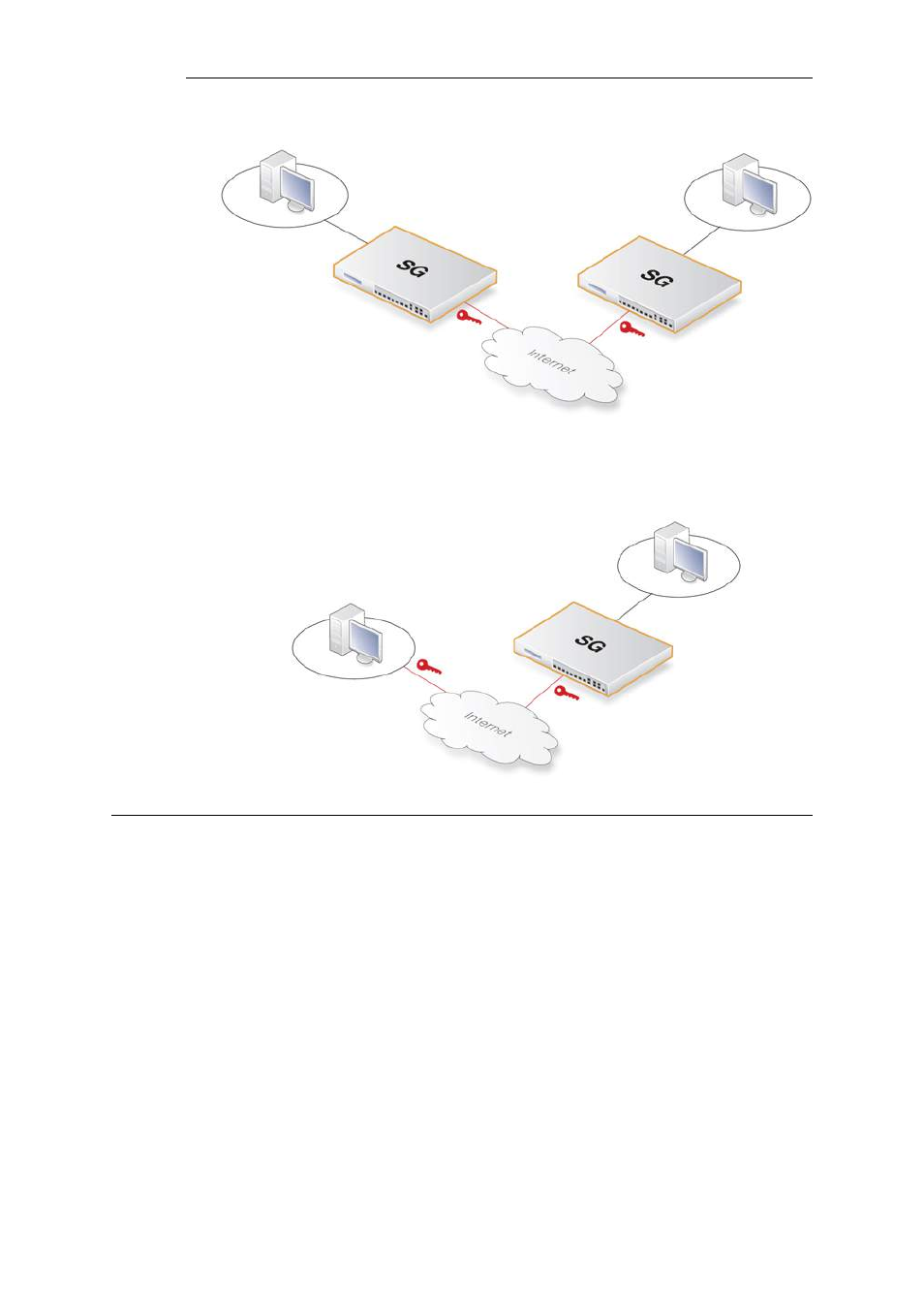
Client to LAN connection - Where many remote clients need to connect to an internal
network over the Internet. In this case, the internal network is protected by the Clavister
Security Gateway to which the client connects and the VPN tunnel is set up between them.
9.1.2. VPN Encryption
Encryption of VPN traffic is done using the science of cryptography. Cryptography is an umbrella
expression covering 3 techniques and benefits:
Confidentiality
No one but the intended recipients is able to receive and
understand
the
communication.
Confidentiality
is
accomplished by encryption.
Authentication and Integrity
Proof for the recipient that the communication was actually
sent by the expected sender, and that the data has not
been modified in transit. This is accomplished by
authentication, and is often implemented through the use
of cryptographic keyed hashing.
Non-repudiation
Proof that the sender actually sent the data; the sender
cannot later deny having sent it. Non-repudiation is usually
a side-effect of authentication.
VPNs are normally only concerned with confidentiality and authentication. Non-repudiation is
Chapter 9: VPN
566
