Amer Networks E5Web GUI User Manual
Page 414
cOS Core supports a variety of SIP usage scenarios. The following three scenarios cover nearly all
possible types of usage:
•
Scenario 1
Protecting local clients - Proxy located on the Internet
The SIP session is between a client on the local, protected side of the Clavister Security
Gateway and a client which is on the external, unprotected side. The SIP proxy is located on
the external, unprotected side of the Clavister Security Gateway. Communication typically
takes place across the public Internet with clients on the internal, protected side registering
with a proxy on the public, unprotected side.
•
Scenario 2
Protecting proxy and local clients - Proxy on the same network as clients
The SIP session is between a client on the local, protected side of the Clavister Security
Gateway and a client which is on the external, unprotected side. The SIP proxy is located on
the local, protected side of the Clavister Security Gateway and can handle registrations from
both clients located on the same local network as well as clients on the external, unprotected
side. Communication can take place across the public Internet or between clients on the local
network.
•
Scenario 3
Protecting proxy and local clients - Proxy on a DMZ interface
The SIP session is between a client on the local, protected side of the Clavister Security
Gateway and a client which is on the external, unprotected side. The SIP proxy is located on
the DMZ interface and is physically separated from the local client network as well as the
remote client network and proxy network.
All the above scenarios will also deal with the situation where two clients in a session reside on
the same network.
These scenarios will now be examined in detail.
Scenario 1
Protecting local clients - Proxy located on the Internet
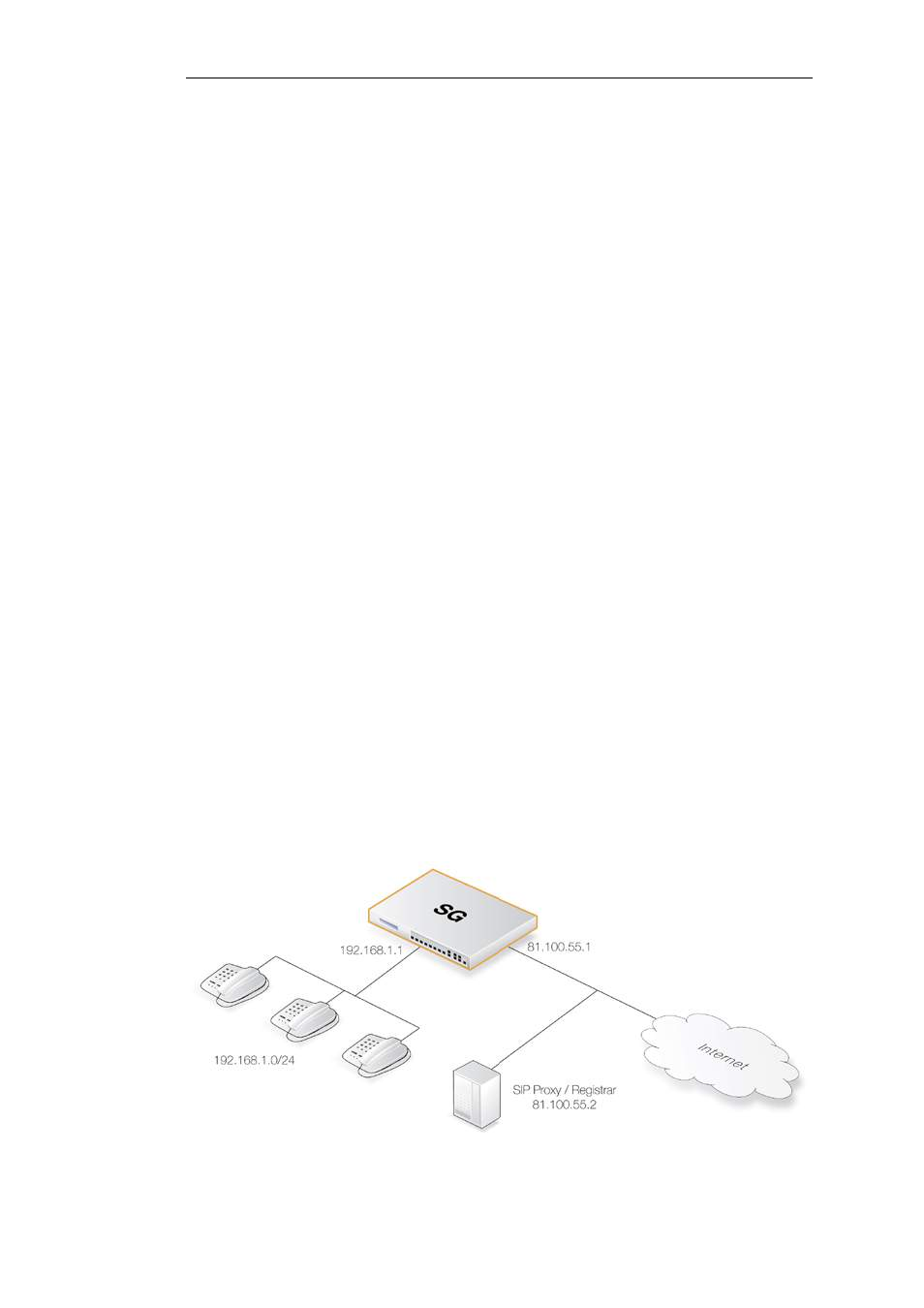
The scenario assumed is an office with VoIP users on a private internal network where the
network's topology will be hidden using NAT. This is illustrated below.
The SIP proxy in the above diagram could alternatively be located remotely across the Internet.
Chapter 6: Security Mechanisms
414
