SMC Networks SMC TigerStack III SMC6824MPE User Manual
Page 310
C
OMMAND
L
INE
I
NTERFACE
4-48
The SSH server on this switch supports both password and public key
authentication. If password authentication is specified by the SSH client, then
the password can be authenticated either locally or via a RADIUS or
TACACS+ remote authentication server, as specified by the authentication
login command on page 4-100. If public key authentication is specified by
the client, then you must configure authentication keys on both the client and
the switch as described in the following section. Note that regardless of
whether you use public key or password authentication, you still have to
generate authentication keys on the switch and enable the SSH server.
To use the SSH server, complete these steps:
1. Generate a Host Key Pair – Use the ip ssh crypto host-key generate
command to create a host public/private key pair.
2. Provide Host Public Key to Clients – Many SSH client programs
automatically import the host public key during the initial connection
setup with the switch. Otherwise, you need to manually create a known
hosts file on the management station and place the host public key in it.
An entry for a public key in the known hosts file would appear similar to
the following example:
10.1.0.54 1024 35 15684995401867669259333946775054617325313674890836547254
15020245593199868544358361651999923329781766065830956 10825913212890233
76546801726272571413428762941301196195566782 59566410486957427888146206
51941746772984865468615717739390164779355942303577413098022737087794545240839717
52646358058176716709574804776117
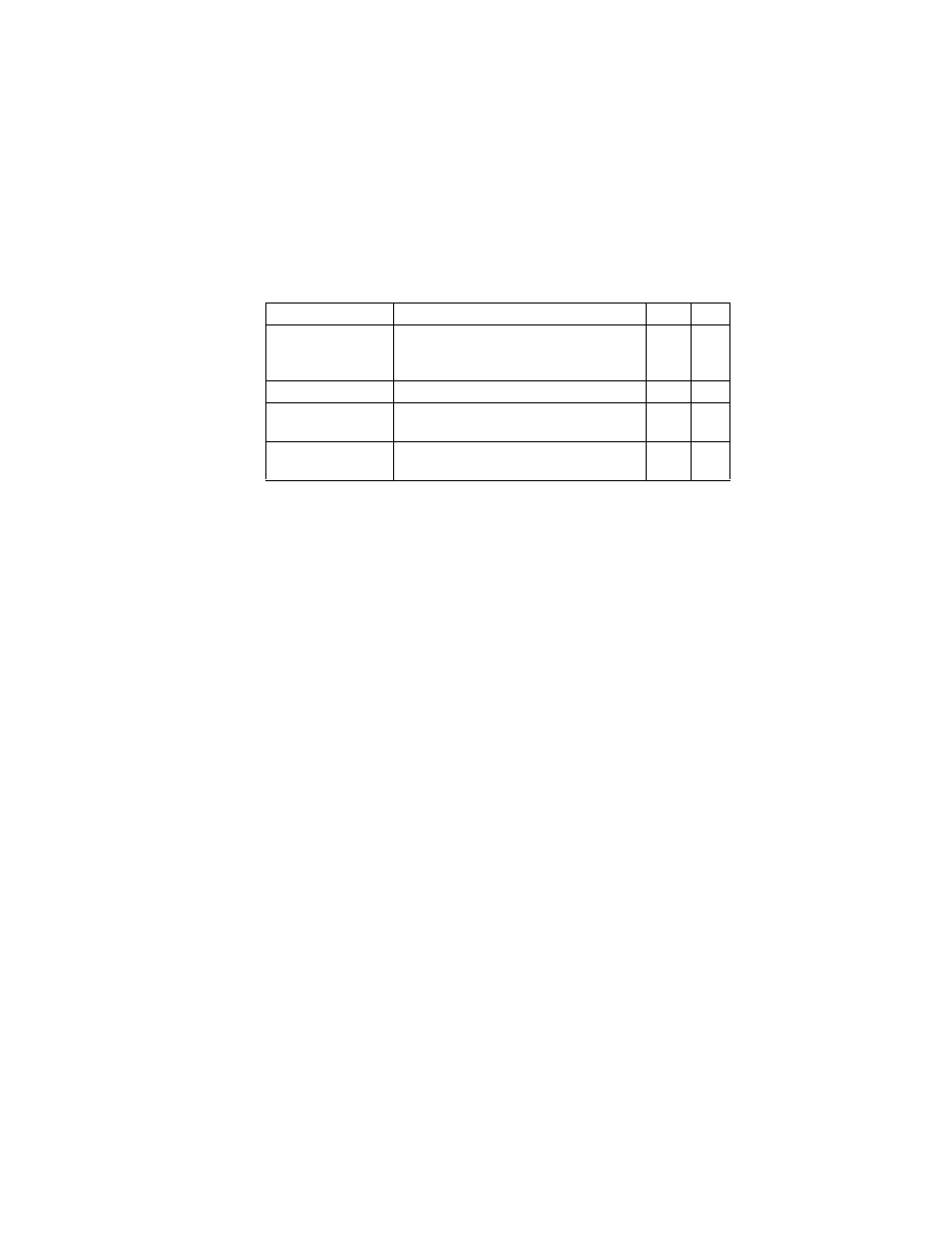
show ip ssh
Displays the status of the SSH server and the
configured values for authentication timeout
and retries
PE
show ssh
Displays the status of current SSH sessions
PE
show public-key
Shows the public key for the specified user or
for the host
PE
show users
Shows SSH users, including privilege level
and public key type
PE
Table 4-15 Secure Shell Commands
Command
Function
Mode Page
