4 crypto map transform sets, Crypto map transform sets – Motorola Series Switch WS5100 User Manual
Page 282
6-58 WS5100 Series Switch System Reference Guide
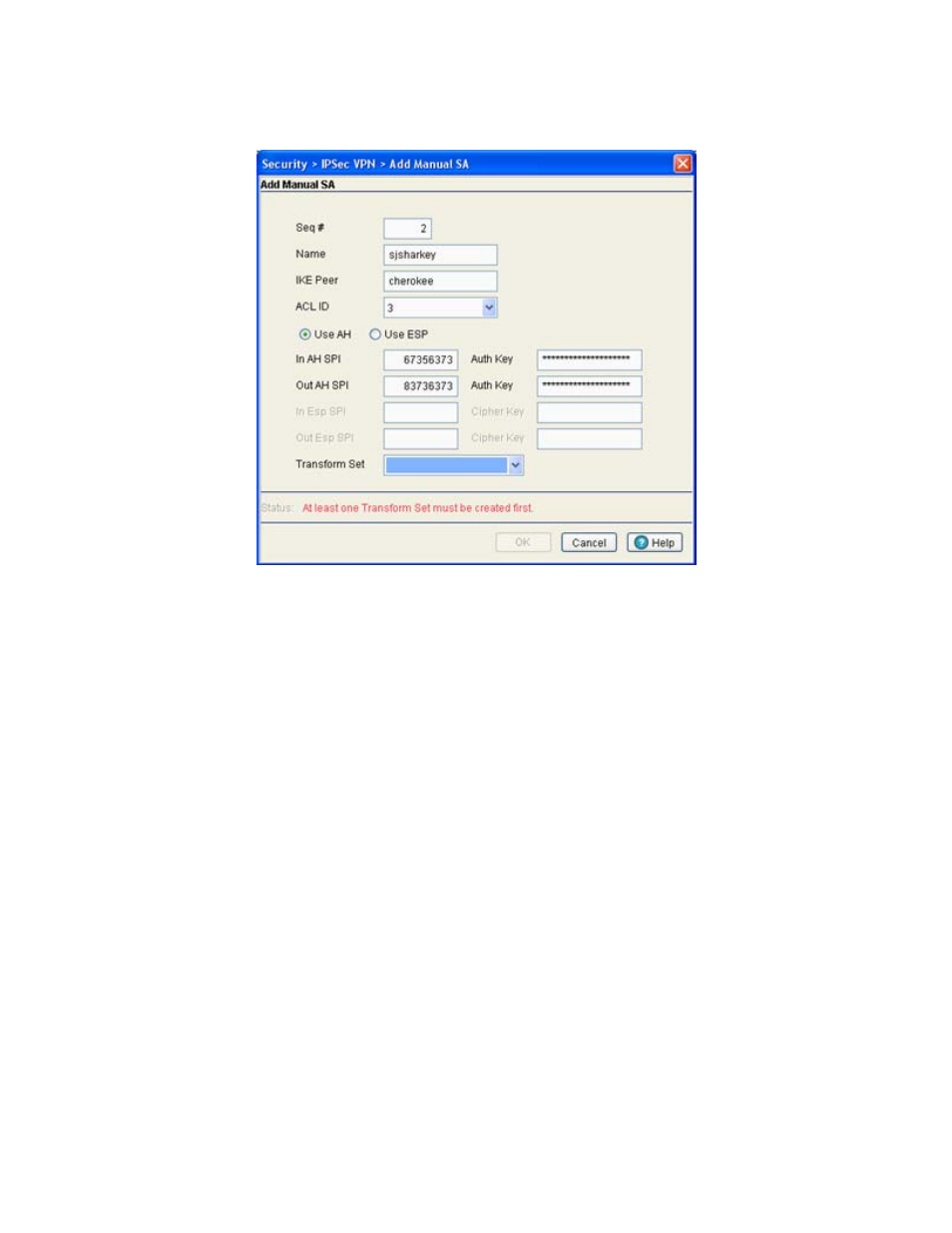
6. If a new Crypto Map manual security association requires creation, click the
Add
button.
a. Define the
Seq #
. The sequence number determines priority among Crypto Maps. The lower the
number, the higher the priority.
b. Provide a unique
Name
for this Crypto Map with the manual security association to differentiate it
from others with similar configurations.
c. Enter the name of the
IKE Peer
used to build an IPSec security association.
d. Use the
ACL ID
drop-down menu to permit a Crypto Map data flow using the permissions within the
selected ACL.
e. Select either the
AH
or
ESP
radio button to define whether the Crypto Map’s manual security
association is an AH Transform Authentication scheme or an ESP Encryption Transform scheme. The
AH SPI or ESP SPI fields and key fields become enabled depending on which radio button is selected.
f. Define the
In AH SPI
and
Auth Keys
or
In Esp
and
Cipher Keys
depending on which option has
been selected.
g. Use the
Transform Set
drop-down menu to select the transform set representing a combination of
security protocols and algorithms. During the IPSec security association negotiation, peers agree to
use the transform set for protecting the data flow. A new manual security association cannot be
generated without the selection of a transform set. A default transform set is available if none are
defined.
7. Click
OK
when completed to save the configuration of the Crypto Map security association.
6.8.4.4 Crypto Map Transform Sets
A transform set is a combination of security protocols and algorithms that define how the switch protects
data.
To review, revise or add a Crypto Map transform set:
