Configuring the security system – Grass Valley iTX System v.2.6 User Manual
Page 74
Security in an iTX system
Attribute
Rights
System Manager
Grants user the right to access various System Management
features.
Metadata Management
Indicates that a user, group, application or computer has permission
to perform administration of the business metadata configuration.
Asset Lock
Indicates that a user, group, application or computer has permission
to lock an asset or media location.
Asset Unlock
Indicates that a user, group, application or computer has permission
to unlock an asset or media location.
Administrator
Enables Administrative rights
Ignore Security
Ignores Privilege checks
Ignore Permissions
Ignores Permission checks
Configuring the security system
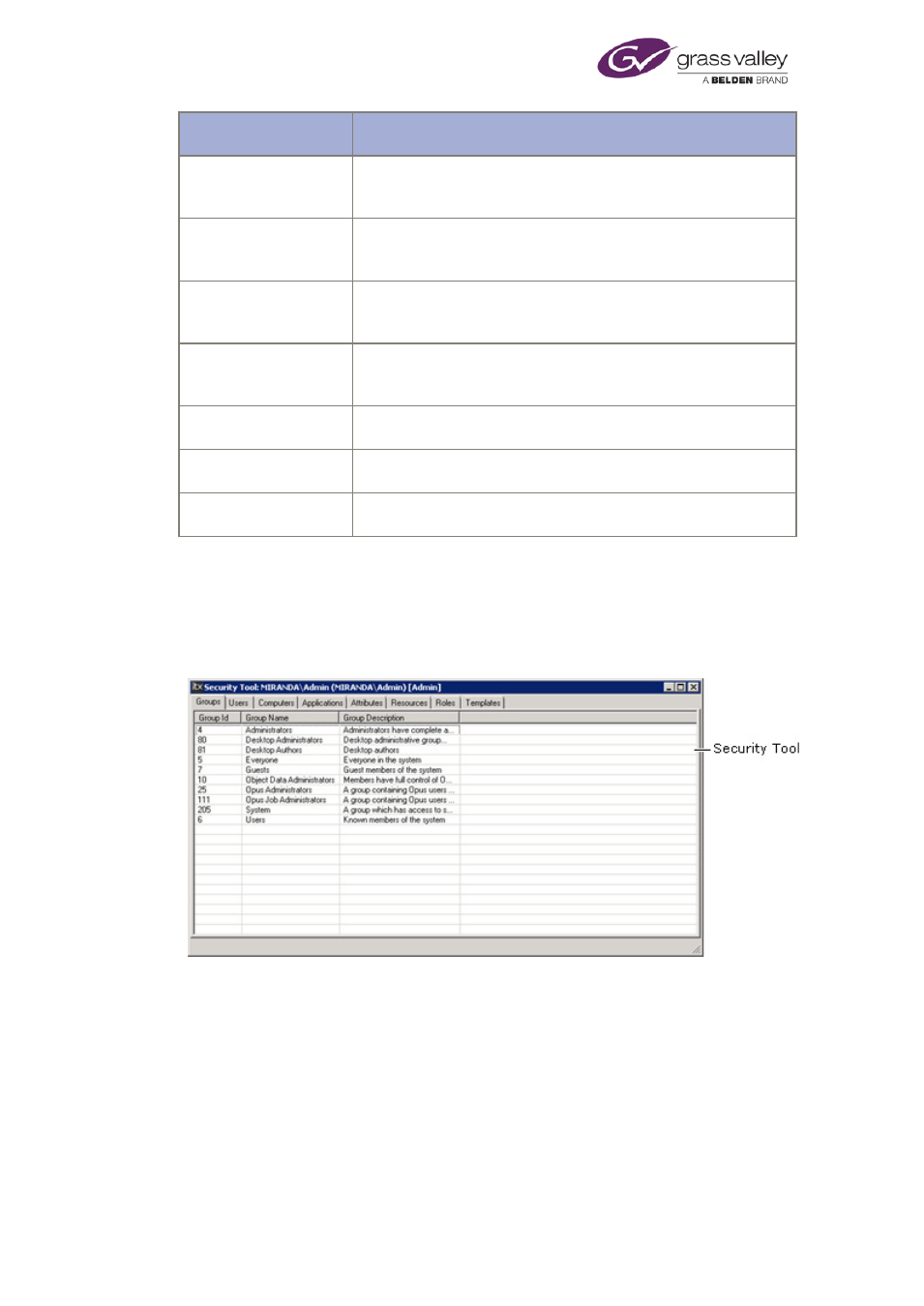
A tool for configuring the security system is installed with the System Service. Called the
Security Tool, it has a window with tabs, under which it displays tables of security-system
information:
The basic steps for configuring the security system are:
1.
Open the Security Tool and manually log onto it as the built-in administrator (or any
member of the Administrators group).
2.
Create user accounts.
3.
Create groups and add users to them.
4.
Assign security attributes to your system-administrator account and to groups.
5.
Close the Security Tool.
March 2015
System Administrator Guide
Page 74 of 404
