Figure 486 wep authentication steps, Dynamic wep key exchange – ZyXEL Communications 5 Series User Manual
Page 766
ZyWALL 5/35/70 Series User’s Guide
766
Appendix G Wireless LANs
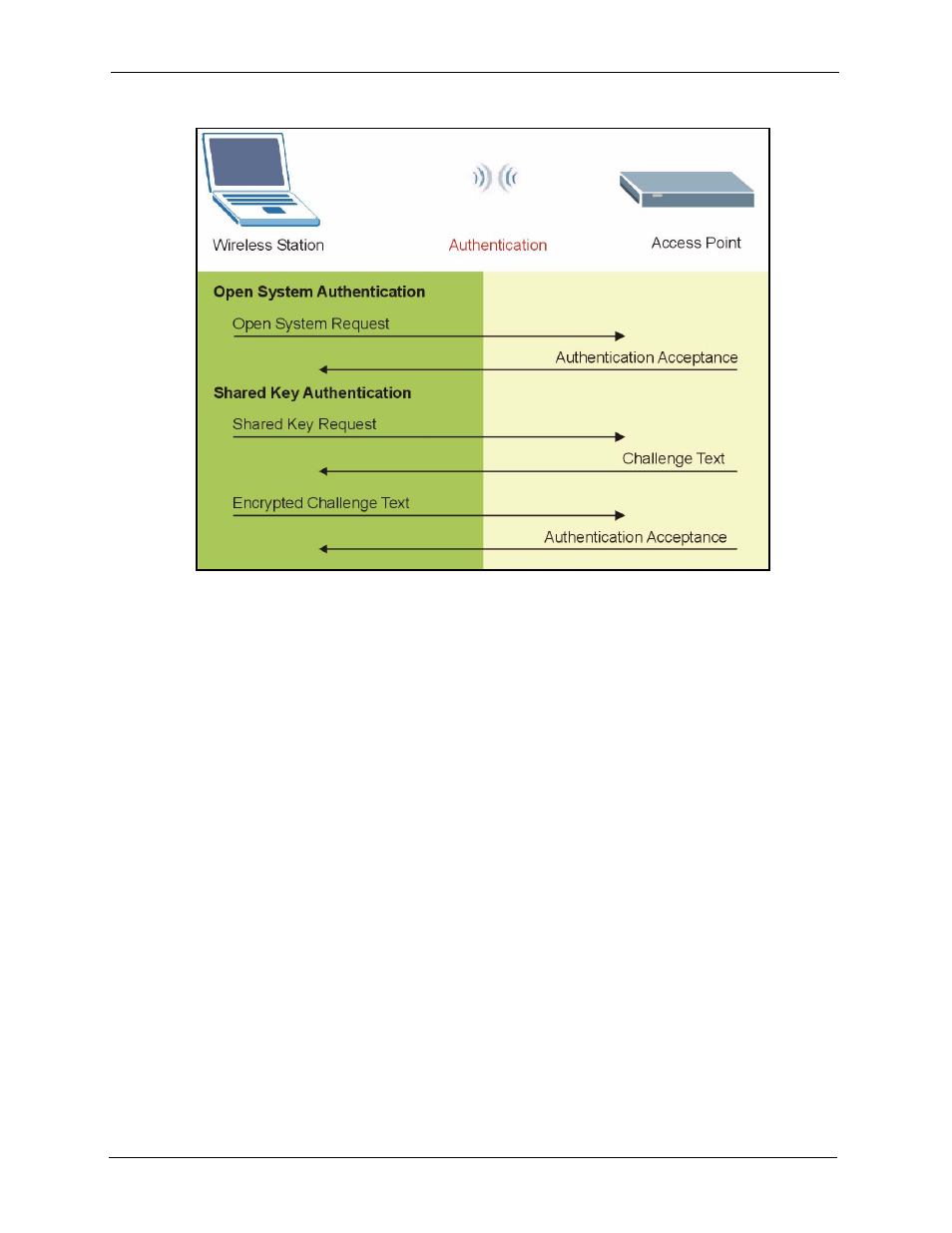
Figure 486 WEP Authentication Steps
Open system authentication involves an unencrypted two-message procedure. A wireless
station sends an open system authentication request to the AP, which will then automatically
accept and connect the wireless station to the network. In effect, open system is not
authentication at all as any station can gain access to the network.
Shared key authentication involves a four-message procedure. A wireless station sends a
shared key authentication request to the AP, which will then reply with a challenge text
message. The wireless station must then use the AP’s default WEP key to encrypt the
challenge text and return it to the AP, which attempts to decrypt the message using the AP’s
default WEP key. If the decrypted message matches the challenge text, the wireless station is
authenticated.
When your device authentication method is set to open system, it will only accept open system
authentication requests. The same is true for shared key authentication. However, when it is
set to auto authentication, the device will accept either type of authentication request and the
device will fall back to use open authentication if the shared key does not match.
Dynamic WEP Key Exchange
The AP maps a unique key that is generated with the RADIUS server. This key expires when
the wireless connection times out, disconnects or reauthentication times out. A new WEP key
is generated each time reauthentication is performed.
