ZyXEL Communications 5 Series User Manual
Page 339
ZyWALL 5/35/70 Series User’s Guide
Chapter 18 IPSec VPN
339
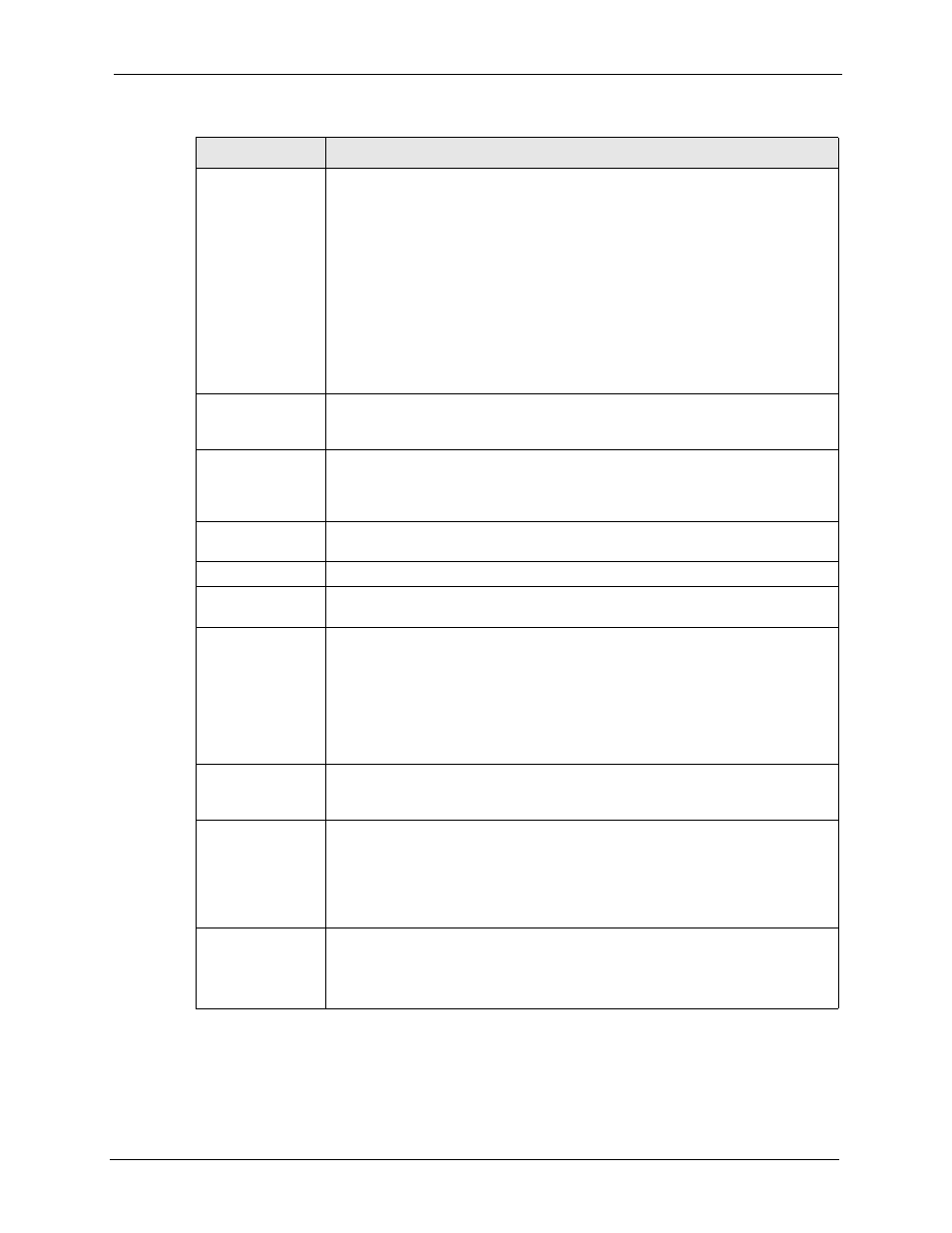
Server Mode
Select Server Mode to have this ZyWALL authenticate extended authentication
clients that request this VPN connection.
You must also configure the extended authentication clients’ usernames and
passwords in the authentication server’s local user database or a RADIUS server
(see
Click Local User to go to the Local User Database screen where you can view
and/or edit the list of user names and passwords. Click RADIUS to go to the
RADIUS screen where you can configure the ZyWALL to check an external
RADIUS server.
During authentication, if the ZyWALL (in server mode) does not find the extended
authentication clients’ user name in its internal user database and an external
RADIUS server has been enabled, it attempts to authenticate the client through
the RADIUS server.
Client Mode
Select Client Mode to have your ZyWALL use a username and password when
initiating this VPN connection to the extended authentication server ZyWALL.
Only a VPN extended authentication client can initiate this VPN connection.
User Name
Enter a user name for your ZyWALL to be authenticated by the VPN peer (in
server mode). The user name can be up to 31 case-sensitive ASCII characters,
but spaces are not allowed. You must enter a user name and password when you
select client mode.
Password
Enter the corresponding password for the above user name. The password can
be up to 31 case-sensitive ASCII characters, but spaces are not allowed.
IKE Proposal
Negotiation Mode
Select Main or Aggressive from the drop-down list box. Multiple SAs connecting
through a secure gateway must have the same negotiation mode.
Encryption
Algorithm
Select which key size and encryption algorithm to use in the IKE SA. Choices are:
DES - a 56-bit key with the DES encryption algorithm
3DES - a 168-bit key with the DES encryption algorithm
AES - a 128-bit key with the AES encryption algorithm
The ZyWALL and the remote IPSec router must use the same algorithms and
keys. Longer keys require more processing power, resulting in increased latency
and decreased throughput.
Authentication
Algorithm
Select which hash algorithm to use to authenticate packet data in the IKE SA.
Choices are SHA1 and MD5. SHA1 is generally considered stronger than MD5,
but it is also slower.
SA Life Time
(Seconds)
Define the length of time before an IKE SA automatically renegotiates in this field.
It may range from 180 to 3,000,000 seconds (almost 35 days).
A short SA Life Time increases security by forcing the two VPN gateways to
update the encryption and authentication keys. However, every time the VPN
tunnel renegotiates, all users accessing remote resources are temporarily
disconnected.
Key Group
Select which Diffie-Hellman key group (DHx) you want to use for encryption keys.
Choices are:
DH1 - use a 768-bit random number
DH2 - use a 1024-bit random number
Table 95 SECURITY > VPN > VPN Rules (IKE) > Edit Gateway Policy (continued)
LABEL
DESCRIPTION
