Intrusion detection and prevention (idp), 1 introduction to idp, 1 firewalls and intrusions – ZyXEL Communications 5 Series User Manual
Page 251: Figure 130 network intrusions
ZyWALL 5/35/70 Series User’s Guide
Chapter 12 Intrusion Detection and Prevention (IDP)
251
C
H A P T E R
1 2
Intrusion Detection and
Prevention (IDP)
This chapter introduces some background information on IDP. Skip to the next chapter to see
how to configure IDP on your ZyWALL.
12.1 Introduction to IDP
An IDP system can detect malicious or suspicious packets and respond instantaneously. It can
detect anomalies based on violations of protocol standards (RFCs – Requests for Comments)
or traffic flows and abnormal flows such as port scans.
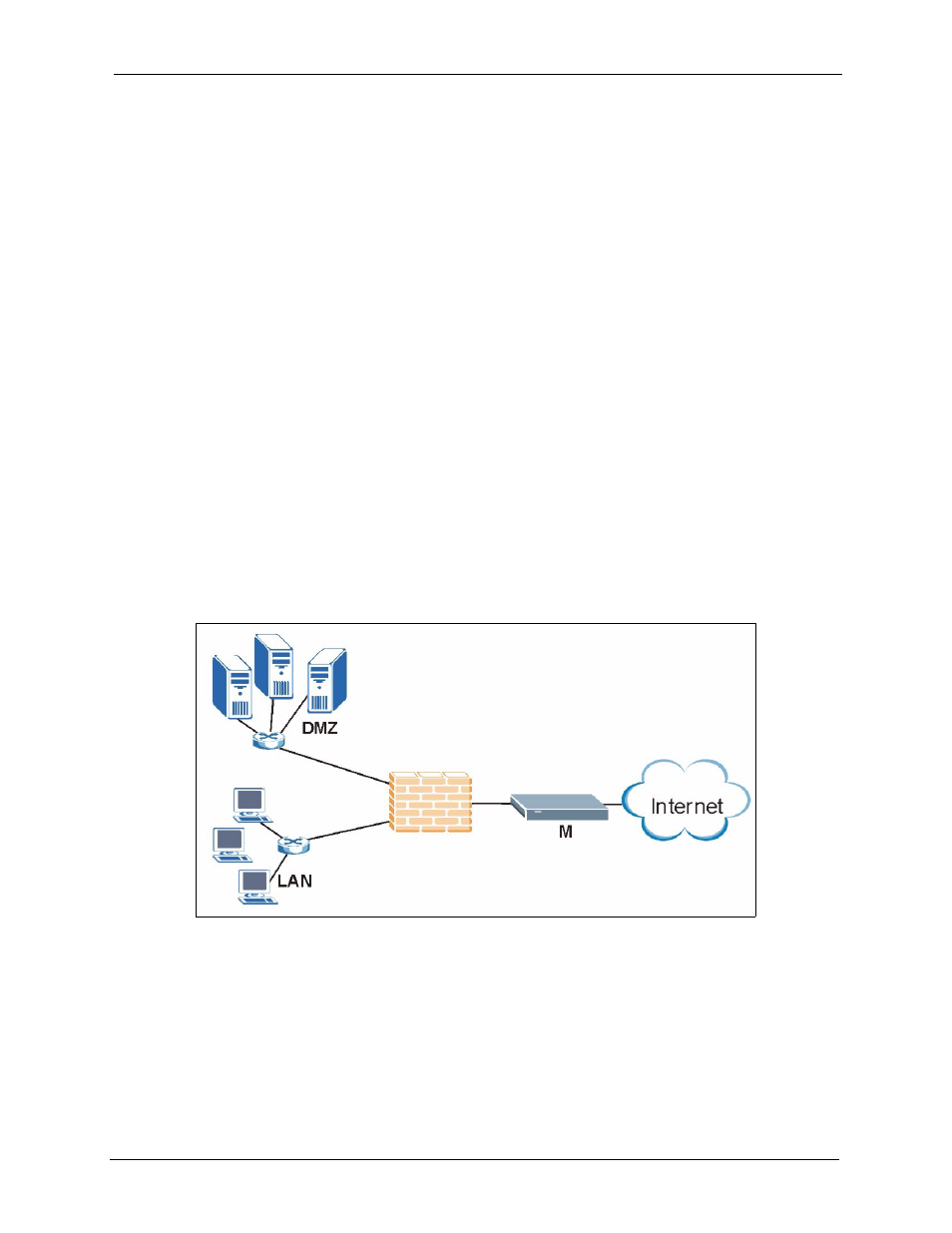
represents a typical business network consisting of a LAN, a DMZ
(DeMilitarized Zone) containing the company web, FTP, mail servers etc., a firewall and/or
NAT router connected to a broadband modem (M) for Internet access.
Figure 130 Network Intrusions
12.1.1 Firewalls and Intrusions
Firewalls are designed to block clearly suspicious traffic and forward other traffic through.
Many exploits take advantage of weaknesses in the protocols that are allowed through the
firewall, so that once an inside server has been compromised it can be used as a backdoor to
launch attacks on other servers.
