Configuring the ssh server, Ssh server configuration tasks – H3C Technologies H3C WX3000 Series Unified Switches User Manual
Page 476
46-4
SSH provides two authentication methods: password authentication and publickey authentication.
z
In password authentication, the client encrypts the username and password, encapsulates them
into a password authentication request, and sends the request to the server. Upon receiving the
request, the server decrypts the username and password, compares them with those it maintains,
and then informs the client of the authentication result.
z
The publickey authentication method authenticates clients using digital signatures. Currently, the
device supports two publickey algorithms to implement digital signatures: RSA and DSA. The client
sends to the server a publickey authentication request containing its user name, public key and
algorithm. The server verifies the public key. If the public key is invalid, the authentication fails;
otherwise, the server generates a digital signature to authenticate the client, and then sends back a
message to inform the success or failure of the authentication.
Session request
After passing authentication, the client sends a session request to the server, while the server listens to
and processes the request from the client. If the client passes authentication, the server sends back to
the client an SSH_SMSG_SUCCESS packet and goes on to the interactive session stage with the
client. Otherwise, the server sends back to the client an SSH_SMSG_FAILURE packet, indicating that
the processing fails or it cannot resolve the request. The client sends a session request to the server,
which processes the request and establishes a session.
Data exchange
In this stage, the server and the client exchanges data in this way:
z
The client encrypts and sends the command to be executed to the server.
z
The server decrypts and executes the command, and then encrypts and sends the result to the
client.
z
The client decrypts and displays the result on the terminal.
Configuring the SSH Server
You must perform necessary configurations on the SSH server for SSH clients to access.
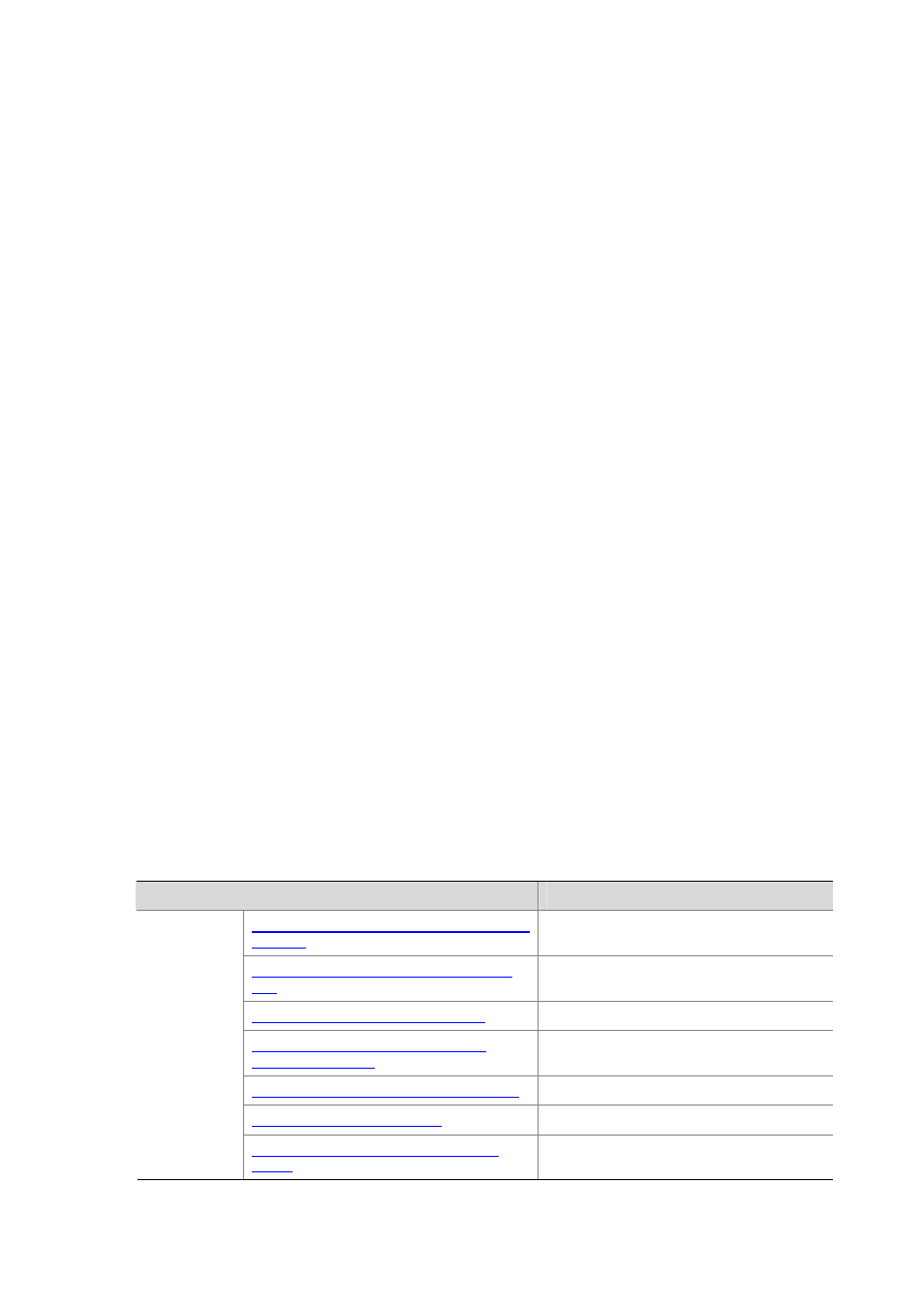
SSH Server Configuration Tasks
Complete the following tasks to configure SSH server:
Task
Remark
Configuring the Protocol Support for the User
Interface
Required
Generating/Destroying a RSA or DSA Key
Pair
Required
Exporting the RSA or DSA Public Key
Optional
Creating an SSH User and Specify an
Authentication Type
Required
Specifying a Service Type for an SSH User
Optional
Optional
Configuring
the SSH
server
Configuring the Client Public Key on the
Server
Required for pubilckey authentication;
unnecessary for password authentication
