Traffic policing, Traffic shaping – H3C Technologies H3C S3100 Series Switches User Manual
Page 589
1-10
Traffic policing
The typical application of traffic policing is to supervise specific traffic into the network and limit it to a
reasonable range, or to "discipline" the extra traffic. In this way, the network resources and the interests
of the operators are protected. For example, you can limit HTTP packets to be within 50% of the
network bandwidth. If the traffic of a certain connection is excess, traffic policing can choose to drop the
packets or to reset the priority of the packets.
Traffic policing is widely used in policing the traffic into the network of internet service providers (ISPs).
Traffic policing can identify the policed traffic and perform pre-defined policing actions based on
different evaluation results. These actions include:
z
Discarding the nonconforming packets.
z
Forwarding the conforming packets or nonconforming packets.
z
Marking the conforming packets with 802.1p precedence and then forwarding the packets.
z
Marking the conforming packets or nonconforming packets with DSCP precedence and forwarding
the packets.
Traffic shaping
Traffic shaping is a measure to regulate the output rate of traffic actively. Its typical application is to
control local traffic output based on the traffic policing indexes of downstream network nodes.
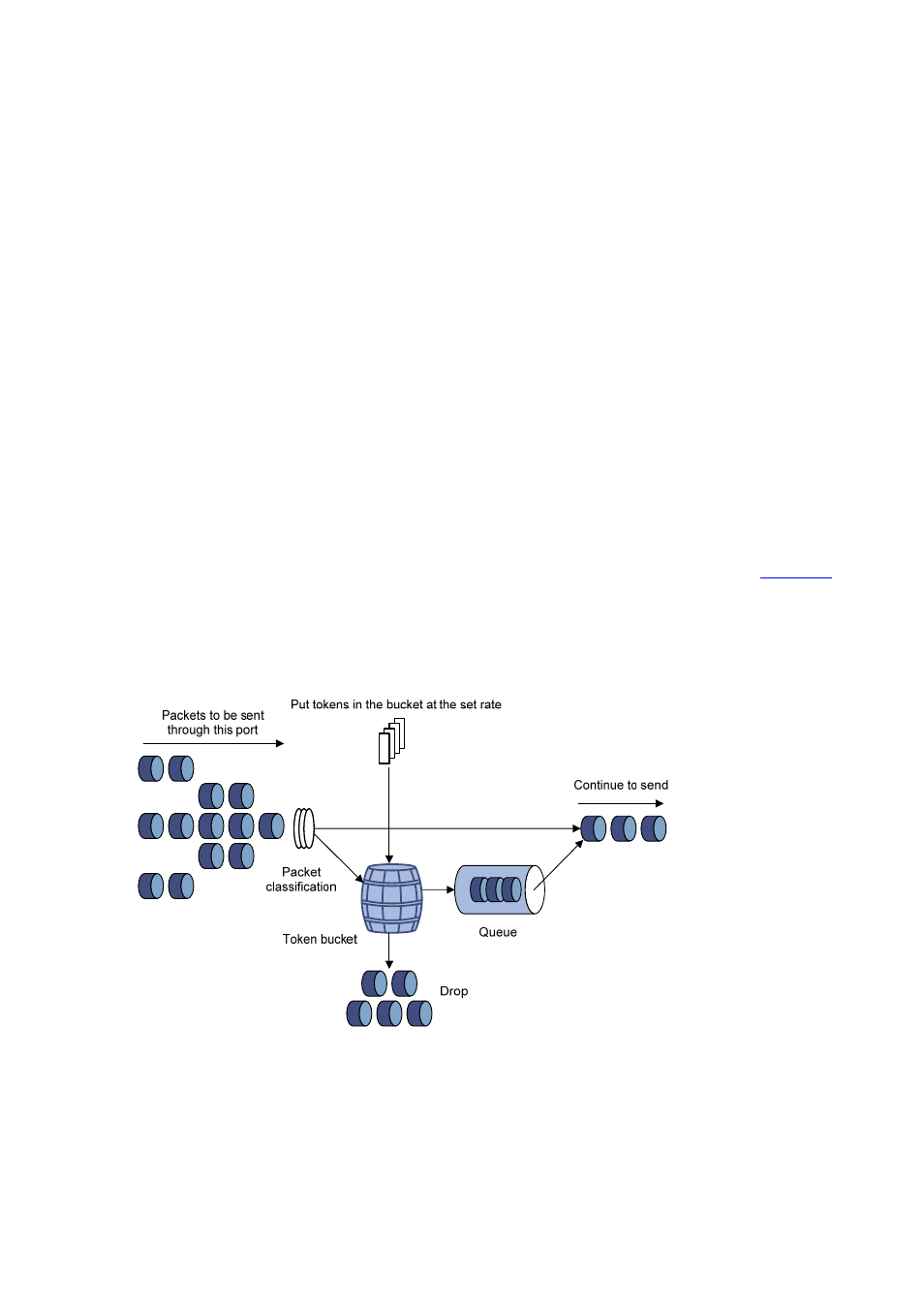
The major difference between traffic shaping and traffic policing is that the packets to be dropped in
traffic policing are cached in traffic shaping——usually in buffers or queues, as shown in
.
When there are enough tokens in the token bucket, the cached packets are sent out evenly. Another
difference between traffic policing and traffic shaping is that traffic shaping may increase the delay while
traffic policing hardly increases the delay.
Figure 1-6 Diagram for traffic shaping
For example, if the device A sends packets to the device B. The device B will perform traffic policing on
packets from the device A to drop the packets beyond the specification.
In order to avoid meaningless packet loss, you can perform traffic shaping on the packets on the egress
of the device A and cache the packets beyond the traffic policing specification in the device A. When the
next packets can be sent, the packets cached in the buffer queues will be taken out and sent. In this way,
all the packets sent to the device B conforms to the traffic specification of the device B.
