ZyXEL Communications ZyWALL 2 Plus User Manual
Page 436
Chapter 25 Logs Screens
ZyWALL 2 Plus User’s Guide
436
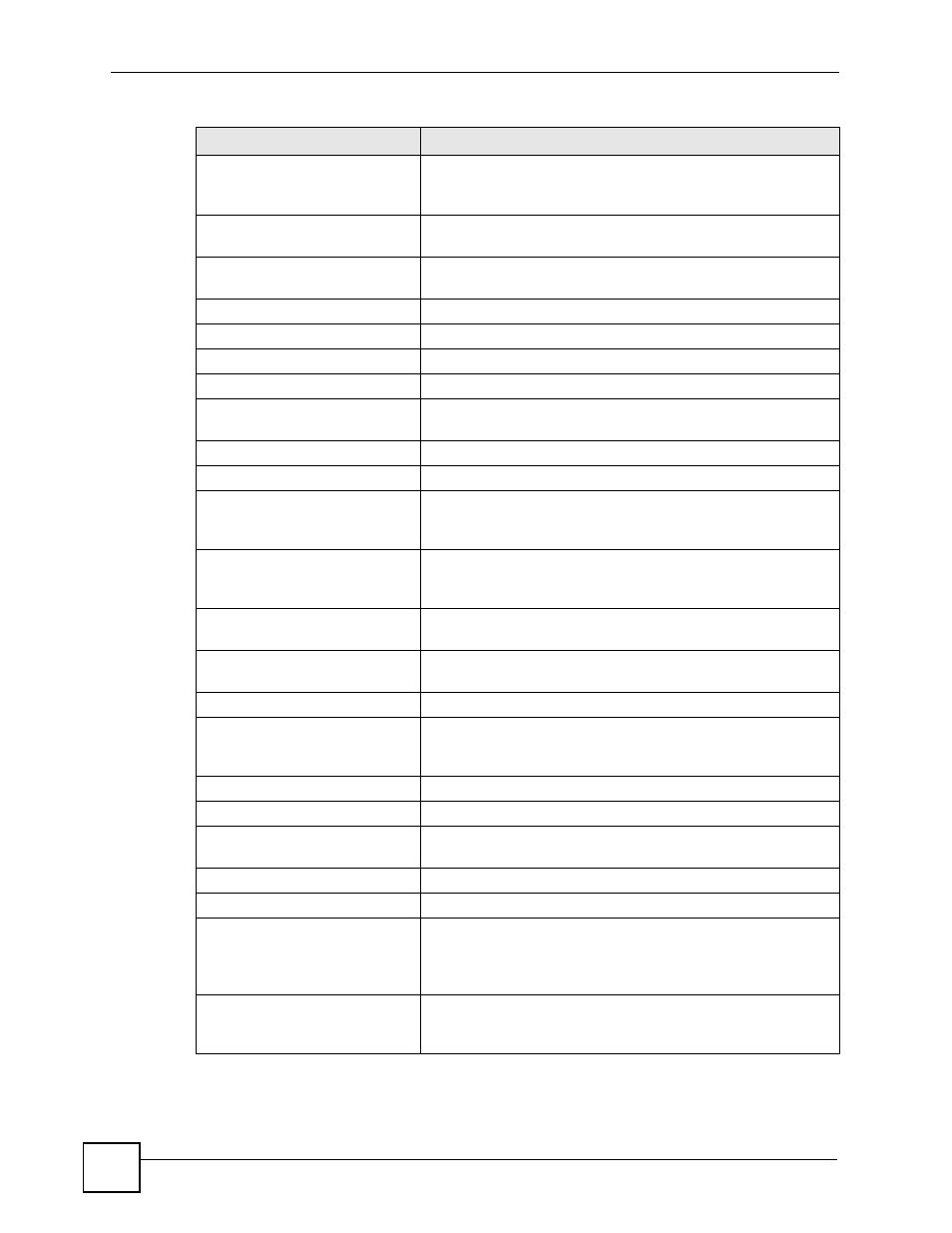
ip spoofing - WAN [ TCP |
UDP | IGMP | ESP | GRE |
OSPF ]
The firewall detected an IP spoofing attack on the WAN port.
ip spoofing - WAN ICMP
(type:%d, code:%d)
The firewall detected an ICMP IP spoofing attack on the WAN
port.
icmp echo : ICMP
(type:%d, code:%d)
The firewall detected an ICMP echo attack.
syn flood TCP
The firewall detected a TCP syn flood attack.
ports scan TCP
The firewall detected a TCP port scan attack.
teardrop TCP
The firewall detected a TCP teardrop attack.
teardrop UDP
The firewall detected an UDP teardrop attack.
teardrop ICMP (type:%d,
code:%d)
The firewall detected an ICMP teardrop attack.
illegal command TCP
The firewall detected a TCP illegal command attack.
NetBIOS TCP
The firewall detected a TCP NetBIOS attack.
ip spoofing - no routing
entry [ TCP | UDP | IGMP
| ESP | GRE | OSPF ]
The firewall classified a packet with no source routing entry as an
IP spoofing attack.
ip spoofing - no routing
entry ICMP (type:%d,
code:%d)
The firewall classified an ICMP packet with no source routing
entry as an IP spoofing attack.
vulnerability ICMP
(type:%d, code:%d)
The firewall detected an ICMP vulnerability attack.
traceroute ICMP (type:%d,
code:%d)
The firewall detected an ICMP traceroute attack.
ports scan UDP
The firewall detected a UDP port scan attack.
Firewall sent TCP packet
in response to DoS attack
TCP
The firewall sent TCP packet in response to a DoS attack
ICMP Source Quench ICMP
The firewall detected an ICMP Source Quench attack.
ICMP Time Exceed ICMP
The firewall detected an ICMP Time Exceed attack.
ICMP Destination
Unreachable ICMP
The firewall detected an ICMP Destination Unreachable attack.
ping of death. ICMP
The firewall detected an ICMP ping of death attack.
smurf ICMP
The firewall detected an ICMP smurf attack.
IP address in FTP port
command is different from
the client IP address. It
maybe a bounce attack.
The IP address in an FTP port command is different from the
client IP address. It may be a bounce attack.
Fragment packet size is
smaller than the MTU size
of output interface.
The fragment packet size is smaller than the MTU size of output
interface.
Table 150 Attack Logs (continued)
LOG MESSAGE
DESCRIPTION
