3 configuring the security check for pcs, Security policy contents, Security level – H3C Technologies H3C Intelligent Management Center User Manual
Page 40: Isolation mode
24
3 Configuring the security check for PCs
EAD works with the iNode client to perform security check on PCs. When a user accesses the network,
the iNode client requests security policies from the EAD server according to the access service of the user.
The iNode client then performs a security check on the user's PC and reports the check results to the EAD
server.
Security policy contents
A security policy consists of a security level, an isolation mode, and security check items.
Security level
A security level specifies the security modes (actions) to implement in response to the detected security
violations. When the detected security violations of a single user require security modes of different
severities, the most severe security mode is implemented.
EAD supports the following system-defined security levels in descending order of severity, as shown
in
. For more information about configuring security levels, see "
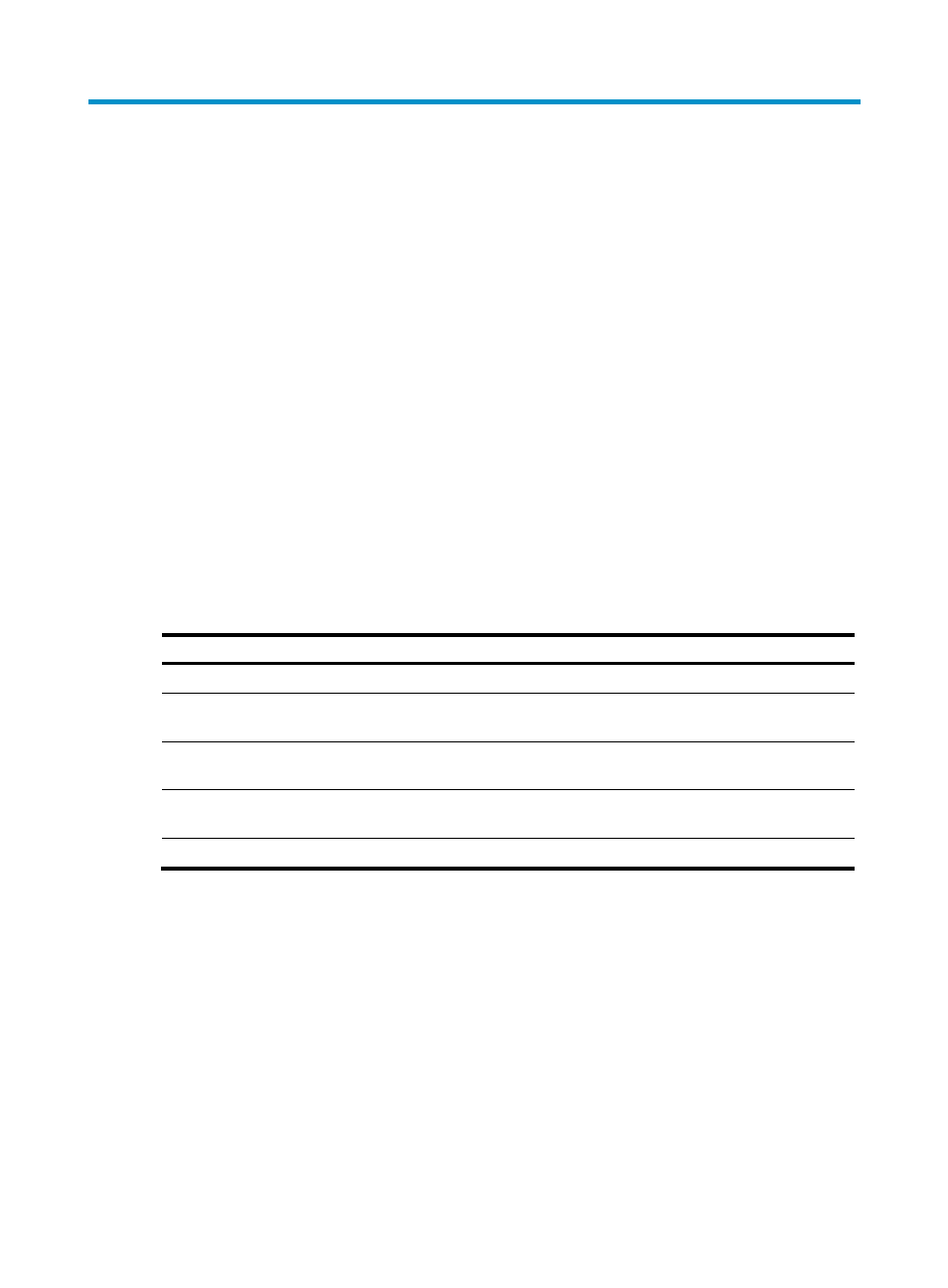
Table 12 Security levels and actions
Security level
Actions in response to detected security violations
Kick out mode
Logs off non-compliant users and generates security logs for violations.
Guest mode
Informs non-compliant users of the security vulnerability and generates security logs for
violations.
Isolate mode
Isolates non-compliant users in a restricted area, informs the users of the security
vulnerability and remediation methods, and generates security logs for violations.
VIP mode
Informs non-compliant users of the security vulnerability and remediation methods and
generates security logs for violations.
Monitor mode
Generates security logs for violations.
Isolation mode
EAD provides the following isolation modes for PCs, as shown in
.
