Security check for pcs, Configuration procedure, Table 6 – H3C Technologies H3C Intelligent Management Center User Manual
Page 28
12
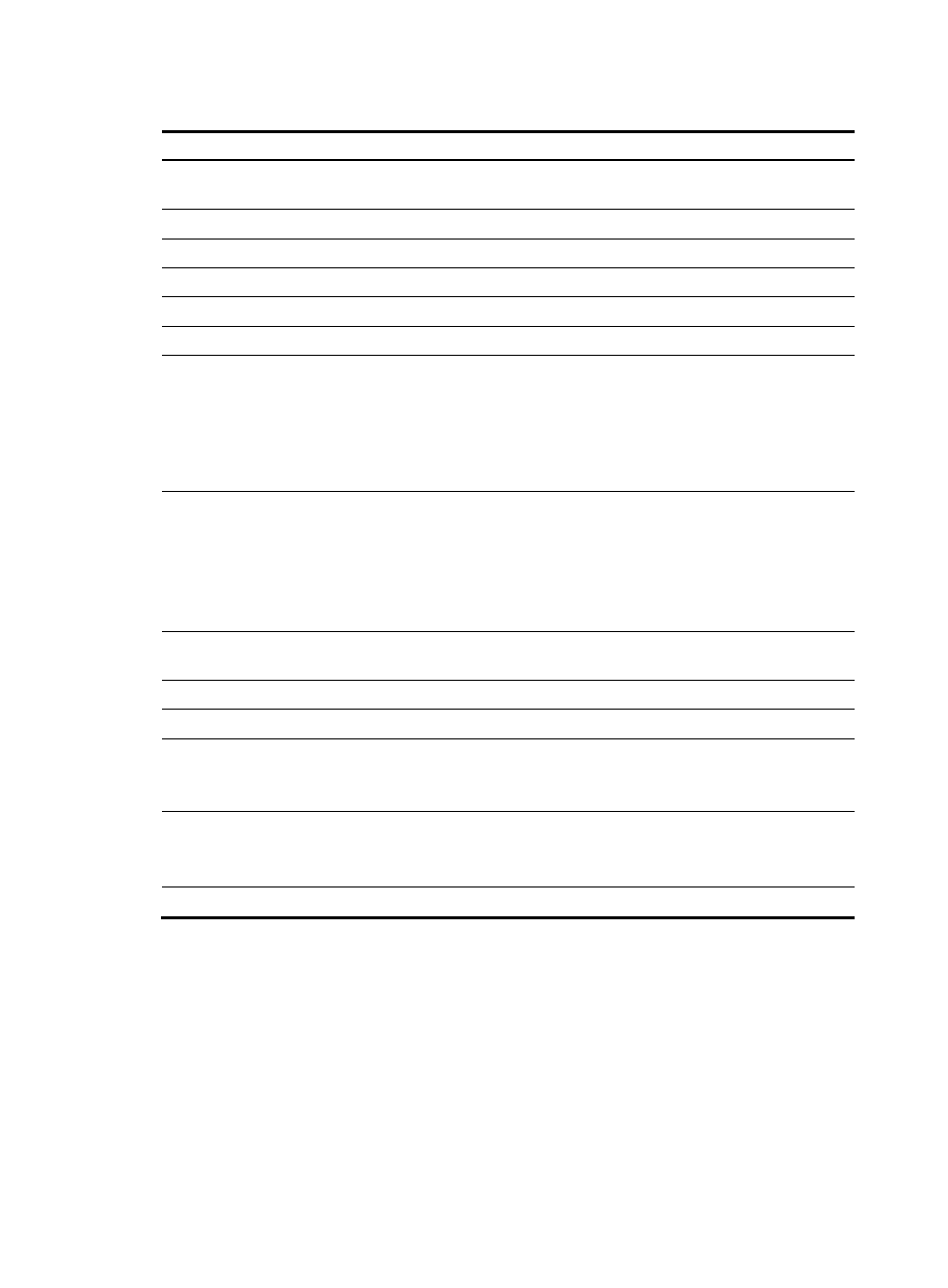
Table 6 Desktop asset applications
Application Task
Quick Start
View the general operation process for the DAM module and links to
configuration tasks.
Asset Group
Query, view, add, modify, and delete asset groups.
All Assets
Query, view, add, modify, and delete assets.
Asset Hardware
Query and view assets' hardware changes.
Asset Software
Query and view assets' software changes.
Control Scheme
View, add, modify, and delete desktop control schemes.
Desktop Control Policy
Navigate to the following desktop control policy pages:
•
Peripheral—View, add, modify, and delete peripheral policies.
•
Energy-Saving—View, add, modify, and delete energy-saving
policies.
•
Monitoring Alarm—View, add, modify, and delete monitoring alarm
policies.
Desktop Control Audit
Navigate to the following desktop control audit pages:
•
USB File Transfer—Query, view, and export USB file transfer logs.
•
Printer Use—Query, view, and export printer monitor logs.
•
Peripheral Use—Query, view, and export logs for unauthorized use of
peripheral devices.
•
Asset File Check—Check suspicious files on assets in real time.
Asset Statistics
Displays the asset statistics by asset type, CPU, hard disk, OS, and
software.
Software Deploy Task
Query, view, add, modify, and delete software deploy tasks.
Software Server
View, add, modify, and delete servers for software distribution.
Verify Asset
Verify assets submitted for registration.
This application is available only when Verify Asset is enabled in DAM
service parameters.
Service Parameters
Navigate to the following service parameter configuration pages:
•
System Settings—Configure DAM service parameters.
•
Validate—Validate the DAM service parameter settings immediately.
Export Task
Schedule a task to periodically export USB file transfer logs.
Security check for PCs
Configuration procedure
To configure security checking for PCs:
1.
Install the iNode client on PCs according to your operating system.
2.
Configure check items to meet the network security requirements.
