3 restricted access, 4 hide zywall identity, 3 security parameters summary – ZyXEL Communications ZyXEL ZyWALL 5 User Manual
Page 104: 3 restricted access 6.2.4 hide zywall identity, Table 23 wireless security relational matrix
ZyWALL 5 User’s Guide
Chapter 6 Wireless LAN
103
6.2.3 Restricted Access
The MAC Filter screen allows you to configure the AP to give exclusive access to devices
(Allow Association) or exclude them from accessing the AP (Deny Association).
6.2.4 Hide ZyWALL Identity
If you hide the ESSID, then the ZyWALL cannot be seen when a wireless client scans for local
APs. The trade-off for the extra security of “hiding” the ZyWALL may be inconvenience for
some valid WLAN clients. If you don’t hide the ESSID, at least you should change the default
one.
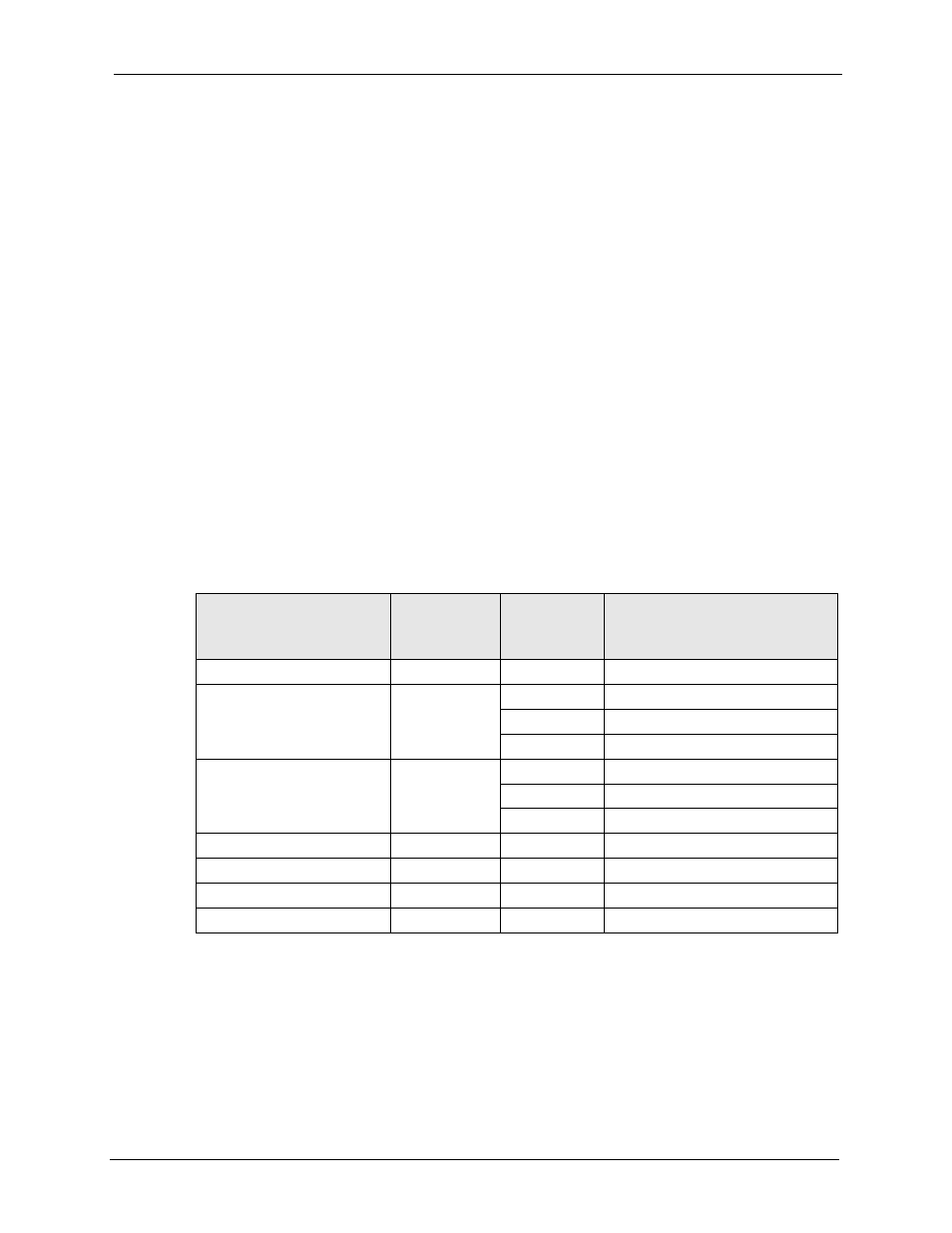
6.3 Security Parameters Summary
Refer to this table to see what other security parameters you should configure for each
Authentication Method/ key management protocol type. You enter manual keys by first
selecting 64-bit WEP or 128-bit WEP from the WEP Encryption field and then typing the
keys (in ASCII or hexadecimal format) in the key text boxes. MAC address filters are not
dependent on how you configure these security features.
Table 23 Wireless Security Relational Matrix
AUTHENTICATION
METHOD/ KEY
MANAGEMENT PROTOCOL
ENCRYPTION
METHOD
ENTER
MANUAL KEY
IEEE 802.1X
Open
None
No
Disable
Open
WEP
No
Enable with Dynamic WEP Key
Yes
Enable without Dynamic WEP Key
Yes
Disable
Shared
WEP
No
Enable with Dynamic WEP Key
Yes
Enable without Dynamic WEP Key
Yes
Disable
WPA
WEP
No
Enable
WPA
TKIP
No
Enable
WPA-PSK
WEP
Yes
Enable
WPA-PSK
TKIP
Yes
Enable
