Figure 448 wpa(2)-psk authentication, Table 271 wireless security relational matrix, Security parameters summary – ZyXEL Communications ZyXEL ZyWALL 2WG User Manual
Page 686: Roaming
Appendix G Wireless LANs
ZyWALL 2WG User’s Guide
686
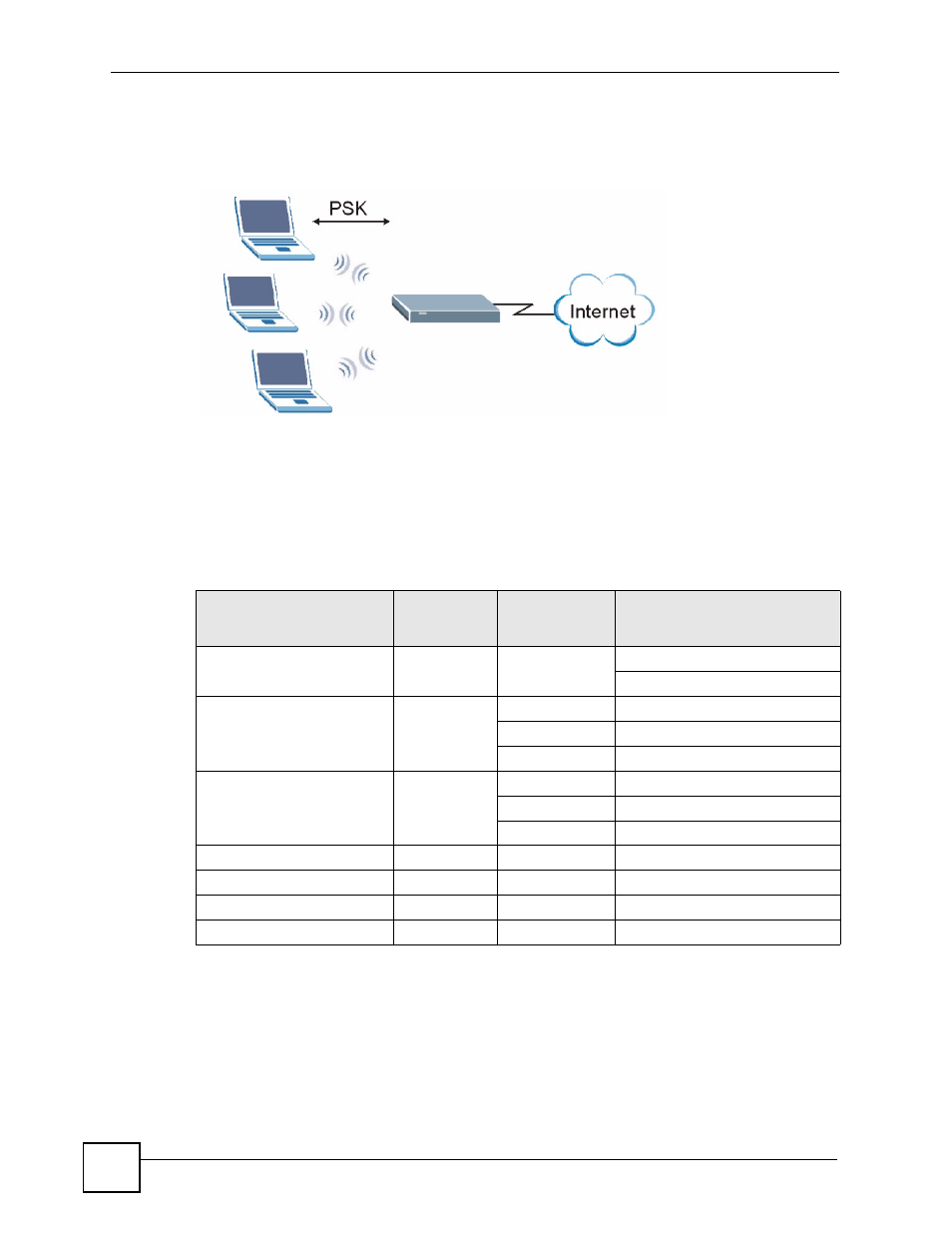
4 The AP and wireless clients use the TKIP or AES encryption process to encrypt data
exchanged between them.
Figure 448 WPA(2)-PSK Authentication
Security Parameters Summary
Refer to this table to see what other security parameters you should configure for each
Authentication Method/ key management protocol type. MAC address filters are not
dependent on how you configure these security features.
Roaming
An AP creates its own wireless coverage area. A wireless station can associate with a
particular access point only if it is within the access point’s coverage area.
Table 271 Wireless Security Relational Matrix
AUTHENTICATION
METHOD/ KEY
MANAGEMENT PROTOCOL
ENCRYPTIO
N METHOD
ENTER
MANUAL KEY
IEEE 802.1X
Open
None
No
Disable
Enable without Dynamic WEP Key
Open
WEP
No
Enable with Dynamic WEP Key
Yes
Enable without Dynamic WEP Key
Yes
Disable
Shared
WEP
No
Enable with Dynamic WEP Key
Yes
Enable without Dynamic WEP Key
Yes
Disable
WPA
TKIP/AES
No
Enable
WPA-PSK
TKIP/AES
Yes
Disable
WPA2
TKIP/AES
No
Enable
WPA2-PSK
TKIP/AES
Yes
Disable
