9 firewall rule summary – ZyXEL Communications ZyXEL ZyWALL 2WG User Manual
Page 215
Chapter 11 Firewall
ZyWALL 2WG User’s Guide
215
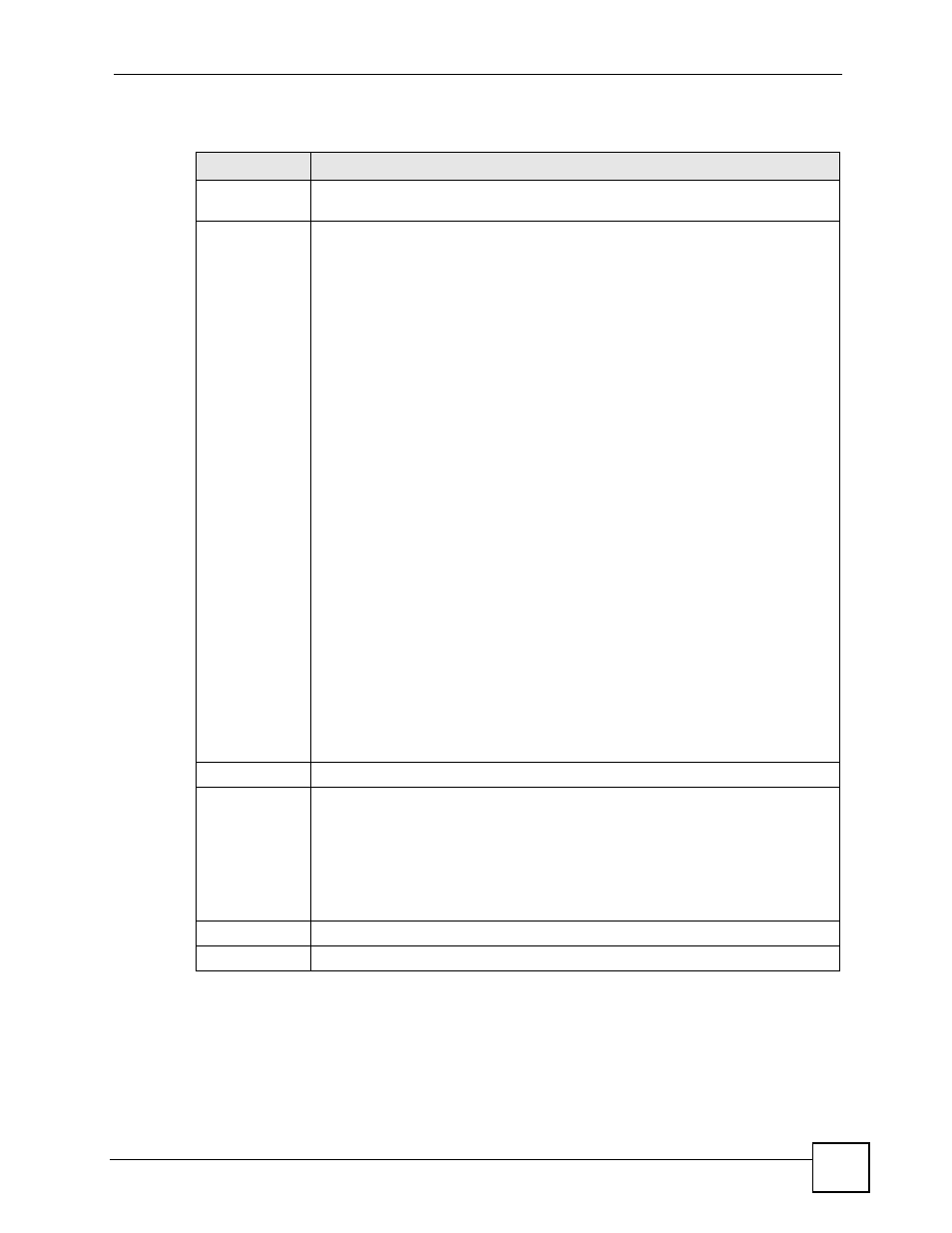
The following table describes the labels in this screen.
11.9 Firewall Rule Summary
Click SECURITY > FIREWALL > Rule Summary to open the screen. This screen displays
a list of the configured firewall rules.
Table 70 SECURITY > FIREWALL > Default Rule (Bridge Mode)
LABEL
DESCRIPTION
Enable Firewall
Select this check box to activate the firewall. The ZyWALL performs access control
and protects against Denial of Service (DoS) attacks when the firewall is activated.
From, To
Set the firewall’s default actions based on the direction of travel of packets. Here are
some example descriptions of the directions of travel.
From LAN To LAN means packets traveling from a computer on one LAN subnet to
a computer on another LAN subnet on the LAN interface of the ZyWALL or the
ZyWALL itself. The ZyWALL does not apply the firewall to packets traveling from a
LAN computer to another LAN computer on the same subnet.
From VPN means traffic that came into the ZyWALL through a VPN tunnel and is
going to the selected “to” interface. For example, From VPN To LAN specifies the
VPN traffic that is going to the LAN. The ZyWALL applies the firewall to the traffic
after decrypting it.
To VPN is traffic that comes in through the selected “from” interface and goes out
through any VPN tunnel. For example, From LAN To VPN specifies the traffic that
is coming from the LAN and going out through a VPN tunnel. The ZyWALL applies
the firewall to the traffic before encrypting it.
From VPN To VPN means traffic that comes in through a VPN tunnel and goes out
through (another) VPN tunnel or terminates at the ZyWALL. This is the case when
the ZyWALL is the hub in a hub-and-spoke VPN. This is also the case if you allow
someone to use a service (like Telnet or HTTP) through a VPN tunnel to manage
the ZyWALL. The ZyWALL applies the firewall to the traffic after decrypting it.
Note: The VPN connection directions apply to the traffic going to or
from the ZyWALL’s VPN tunnels. They do not apply to other
VPN traffic for which the ZyWALL is not one of the gateways
(VPN pass-through traffic).
Here are the default actions from which you can select.
Select Drop to silently discard the packets without sending a TCP reset packet or
an ICMP destination-unreachable message to the sender.
Select Reject to deny the packets and send a TCP reset packet (for a TCP packet)
or an ICMP destination-unreachable message (for a UDP packet) to the sender.
Select Permit to allow the passage of the packets.
Log
Select this to create a log when the above action is taken.
Log Broadcast
Frame
Select this to create a log for any broadcast frames traveling in the selected
direction. Many of these logs in a short time period could indicate a broadcast storm.
A broadcast storm occurs when a packet triggers multiple responses from all hosts
on a network or when computers attempt to respond to a host that never replies. As
a result, duplicated packets are continuously created and circulated in the network,
thus reducing network performance or even rendering it inoperable. A broadcast
storm can be caused by an attack on the network, an incorrect network topology
(such as a bridge loop) or a malfunctioning network device.
Apply
Click Apply to save your changes back to the ZyWALL.
Reset
Click Reset to begin configuring this screen afresh.
