4 security considerations, 5 firewall rules example – ZyXEL Communications ZyXEL ZyWALL 2WG User Manual
Page 209
Chapter 11 Firewall
ZyWALL 2WG User’s Guide
209
11.4 Security Considerations
"
Incorrectly configuring the firewall may block valid access or introduce security
risks to the ZyWALL and your protected network. Use caution when creating or
deleting firewall rules and test your rules after you configure them.
Consider these security ramifications before creating a rule:
1 Does this rule stop LAN users from accessing critical resources on the Internet? For
example, if IRC is blocked, are there users that require this service?
2 Is it possible to modify the rule to be more specific? For example, if IRC is blocked for
all users, will a rule that blocks just certain users be more effective?
3 Does a rule that allows Internet users access to resources on the LAN create a security
vulnerability? For example, if FTP ports (TCP 20, 21) are allowed from the Internet to
the LAN, Internet users may be able to connect to computers with running FTP servers.
4 Does this rule conflict with any existing rules?
Once these questions have been answered, adding rules is simply a matter of entering the
information into the correct fields in the web configurator screens.
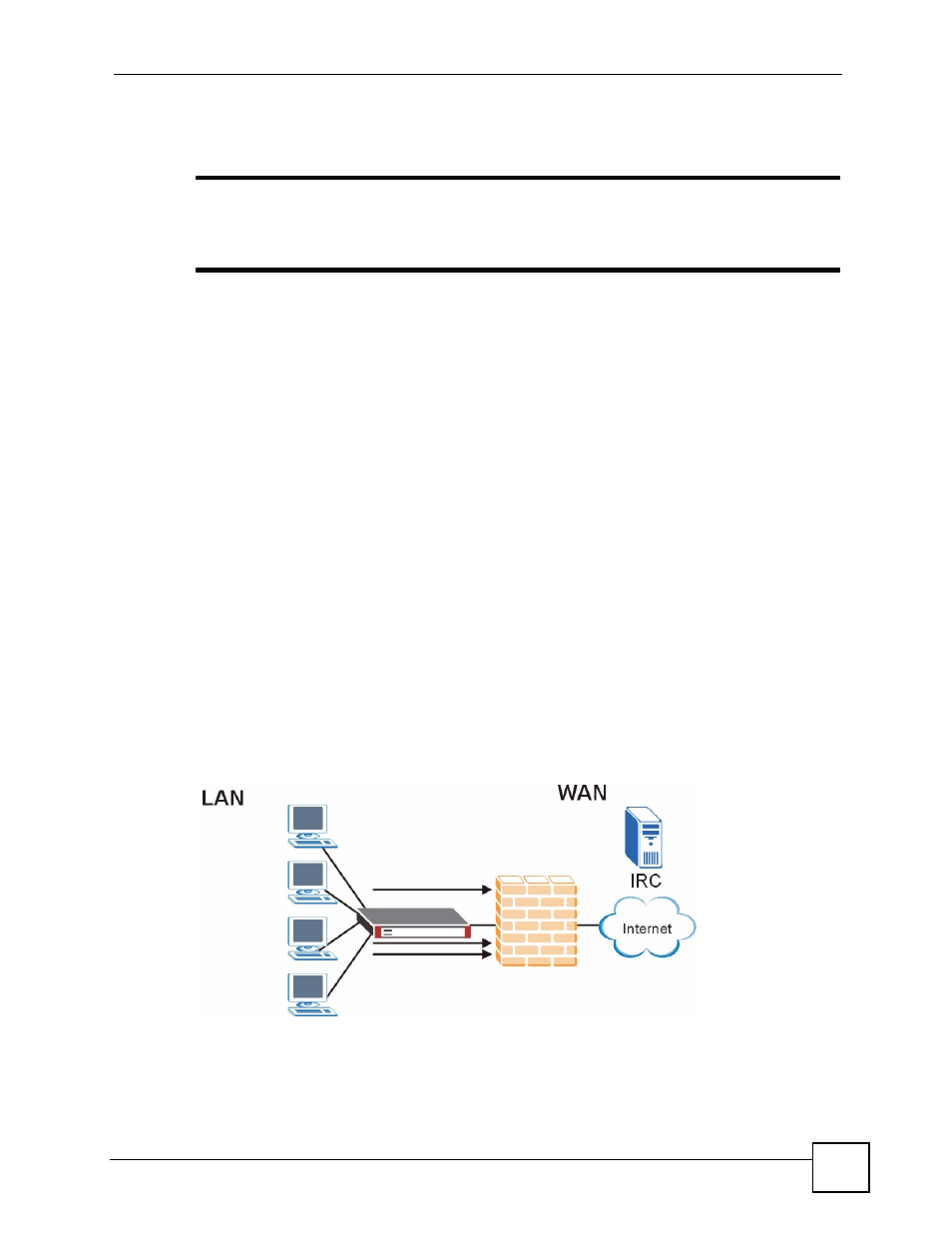
11.5 Firewall Rules Example
Suppose that your company decides to block all of the LAN users from using IRC (Internet
Relay Chat) through the Internet. To do this, you would configure a LAN to WAN firewall
rule that blocks IRC traffic from any source IP address from going to any destination address.
You do not need to specify a schedule since you need the firewall rule to always be in effect.
The following figure shows the results of this rule.
Figure 108 Blocking All LAN to WAN IRC Traffic Example
