2 security parameters summary, 3 wep overview, 1 data encryption – ZyXEL Communications G-2000 Plus User Manual
Page 91: 1 authentication, 2 security parameters summary 7.3 wep overview, Table 23 wireless security relational matrix
ZyAIR G-2000 Plus User’s Guide
Chapter 7 Wireless Security
90
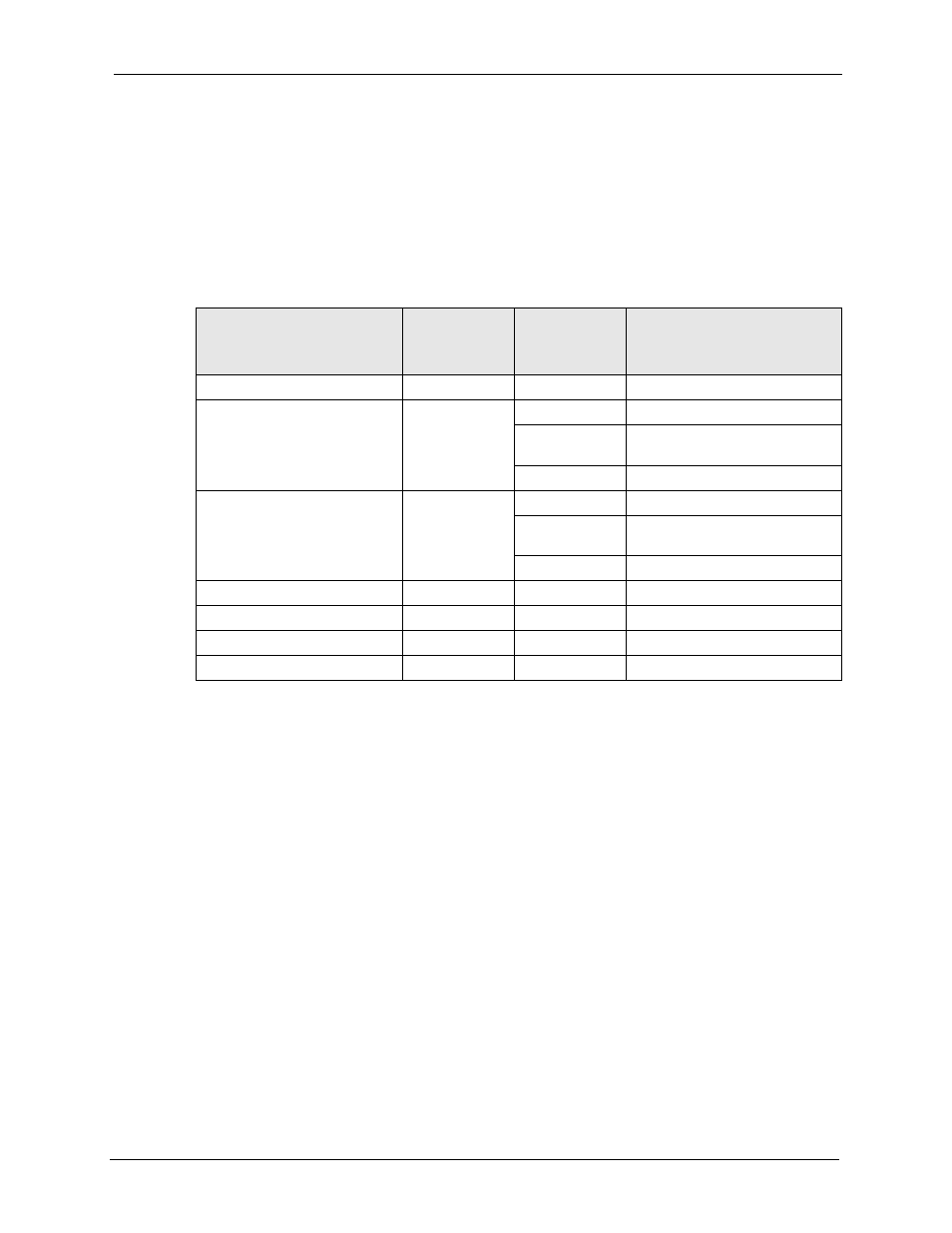
7.2 Security Parameters Summary
Refer to this table to see what other security parameters you should configure for each
Authentication Method/ key management protocol type. You enter manual keys by first
selecting 64-bit WEP or 128-bit WEP from the WEP Encryption field and then typing the
keys (in ASCII or hexadecimal format) in the key text boxes. MAC address filters are not
dependent on how you configure these security features.
Table 23 Wireless Security Relational Matrix
AUTHENTICATION METHOD/
KEY MANAGEMENT
PROTOCOL
ENCRYPTION
METHOD
ENTER
MANUAL KEY IEEE 802.1X
Open
None
No
Disable
Open
WEP
No
Enable with Dynamic WEP Key
Yes
Enable without Dynamic WEP
Key
Yes
Disable
Shared
WEP
No
Enable with Dynamic WEP Key
Yes
Enable without Dynamic WEP
Key
Yes
Disable
WPA
WEP
No
Enable
WPA
TKIP
No
Enable
WPA-PSK
WEP
Yes
Enable
WPA-PSK
TKIP
Yes
Enable
7.3 WEP Overview
WEP (Wired Equivalent Privacy) as specified in the IEEE 802.11 standard provides methods
for both data encryption and wireless station authentication.
7.3.1 Data Encryption
WEP provides a mechanism for encrypting data using encryption keys. Both the AP and the
wireless stations must use the same WEP key to encrypt and decrypt data. Your ZyAIR allows
you to configure up to four 64-bit or 128-bit WEP keys, but only one key can be enabled at
any one time.
7.3.1.1 Authentication
Three different methods can be used to authenticate wireless stations to the network: Open
System, Shared Key, and Auto. The following figure illustrates the steps involved.
