Configuring bfd for ospfv3, Applying ipsec policies for ospfv3 – H3C Technologies H3C S12500 Series Switches User Manual
Page 336
320
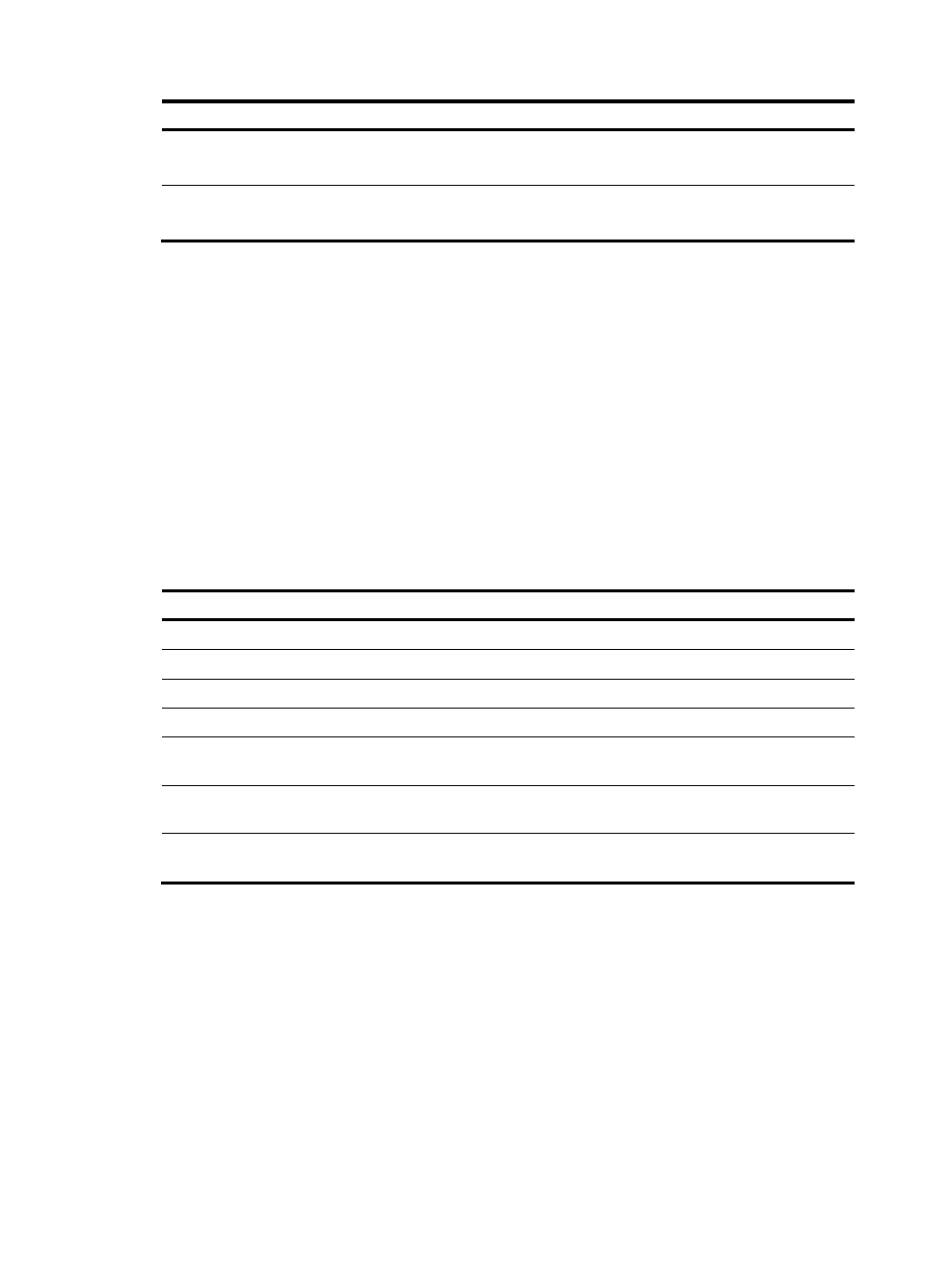
Step Command
Remarks
3.
Enable the GR helper
capability.
graceful-restart helper enable
Optional.
Enabled by default.
4.
Enable strict LSA
checking.
graceful-restart helper
strict-lsa-checking
Optional.
Disabled by default.
Configuring BFD for OSPFv3
Bidirectional forwarding detection (BFD) provides a mechanism to quickly detect the connectivity of links
between OSPFv3 neighbors, thus to improve the convergence speed of OSPFv3. For more information
about BFD, see High Availability Configuration Guide.
After discovering neighbors by sending hello packets, OSPFv3 notifies BFD of the neighbor addresses,
and BFD uses these addresses to establish sessions. Before a BFD session is established, it is in down state.
In this state, BFD control packets are sent at an interval of no less than 1 second to reduce BFD control
packet traffic. After the BFD session is established, BFD control packets are sent at the negotiated interval,
thereby implementing fast fault detection.
To configure BFD for OSPFv3, you need to configure OSPFv3 first.
To configure BFD for OSPFv3:
Step Command
Remarks
1.
Enter system view.
system-view
N/A
2.
Enter OSPFv3 view.
ospfv3 [ process-id ]
N/A
3.
Specify a router ID.
router-id router-id
N/A
4.
Quit the OSPFv3 view.
quit
N/A
5.
Enter interface view.
interface interface-type
interface-number
N/A
6.
Enable an OSPFv3 process
on the interface.
ospfv3 process-id area area-id
[ instance instance-id ]
Not enabled by default.
7.
Enable BFD on the interface. ospfv3 bfd enable [ instance
instance-id ]
Not enabled by default.
Applying IPsec policies for OSPFv3
To protect routing information and defend attacks, OSPFv3 supports using an IPsec policy to authenticate
protocol packets as follows.
Outbound OSPFv3 packets carry the Security Parameter Index (SPI) defined in the corresponding IPsec
policy. A switch uses the SPI carried in a received packet to match against the configured IPsec policy. If
they match, the switch accepts the packet; otherwise, it discards the packet and thus will not establish a
neighbor relationship with the sending switch.
You can configure an IPsec policy for an area, an interface or a virtual link.
