4 vpn rules (ike) > network policy move, Move – ZyXEL Communications Centralized Network Management Vantage CNM User Manual
Page 133
Chapter 6 Device Security Settings
Vantage CNM User’s Guide
133
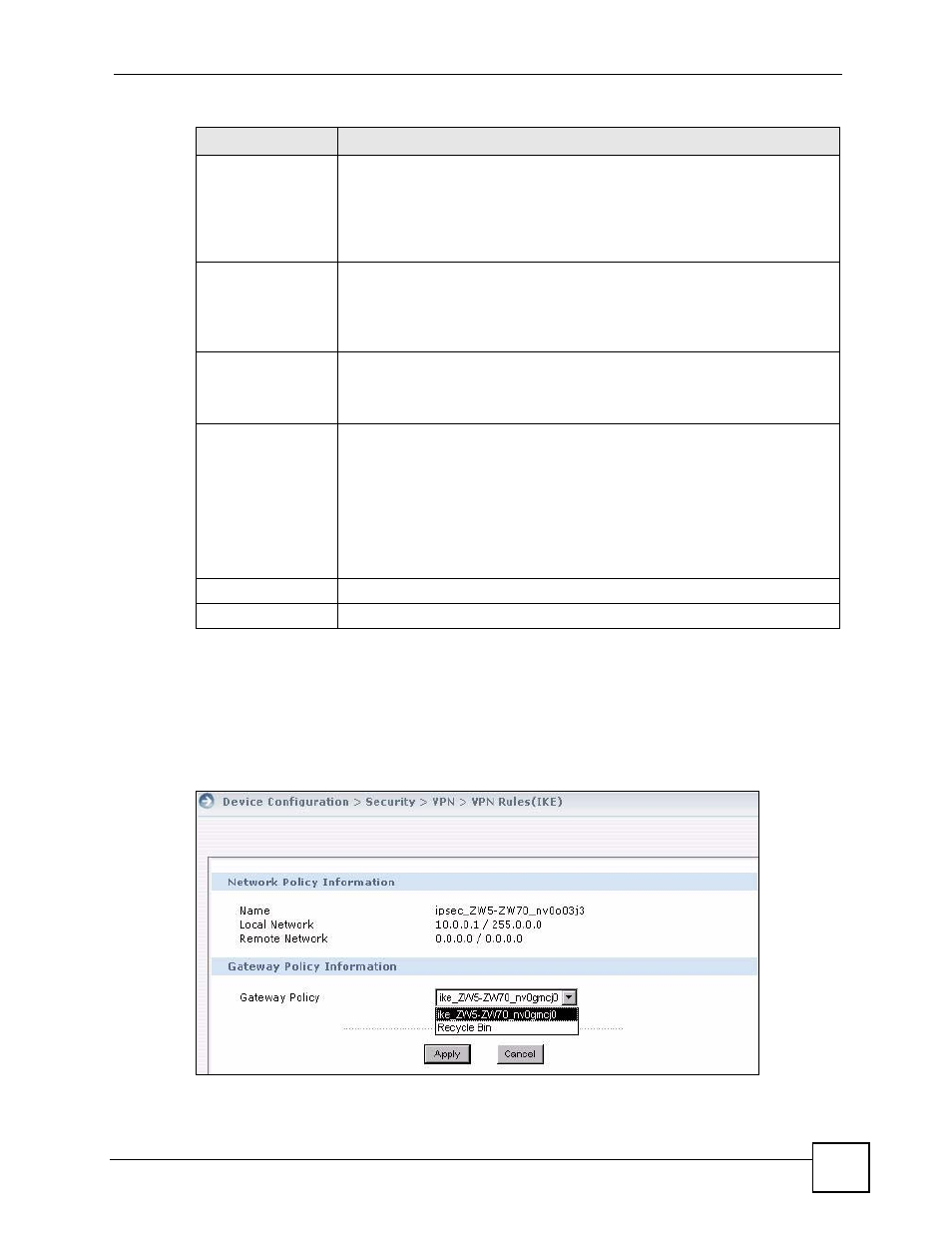
6.3.4 VPN Rules (IKE) > Network Policy Move
In the VPN Rule (IKE) screen, click the move icon to display the screen shown next.Use this
screen to associate a network policy to a gateway policy.
Figure 61 Device Operation > Device Configuration > Security > VPN > VPN Rules (IKE) >
Network Policy Move
SA Life Time
(Seconds)
Define the length of time before an IPSec SA automatically renegotiates in this
field. The minimum value is 180 seconds.
A short SA Life Time increases security by forcing the two VPN gateways to
update the encryption and authentication keys. However, every time the VPN
tunnel renegotiates, all users accessing remote resources are temporarily
disconnected.
Perfect Forward
Secret (PFS)
Perfect Forward Secret (PFS) is disabled (NONE) by default in phase 2 IPSec
SA setup. This allows faster IPSec setup, but is not so secure.
Select DH1 or DH2 to enable PFS. DH1 refers to Diffie-Hellman Group 1 a 768
bit random number. DH2 refers to Diffie-Hellman Group 2 a 1024 bit (1Kb)
random number (more secure, yet slower).
Enable Replay
Detection
As a VPN setup is processing intensive, the system is vulnerable to Denial of
Service (DOS) attacks. The IPSec receiver can detect and reject old or
duplicate packets to protect against replay attacks. Enable replay detection by
selecting this check box.
Enable Multiple
Proposals
Select this check box to allow the device to use any of its phase 1 or phase 2
encryption and authentication algorithms when negotiating an IPSec SA.
When you enable multiple proposals, the device allows the remote IPSec router
to select which encryption and authentication algorithms to use for the VPN
tunnel, even if they are less secure than the ones you configure for the VPN
rule.
Clear this check box to have the device use only the phase 1 or phase 2
encryption and authentication algorithms configured below when negotiating an
IPSec SA.
Apply
Click Apply to save the changes.
Cancel Click
Cancel to discard all changes and return to the main VPN screen.
Table 49 Device Operation > Device Configuration > VPN > IKE IPSec (continued)
LABEL
DESCRIPTION
