Creating named standard ip acls, Applying the acl to an interface, Applying the acl to an – Cisco 15327 User Manual
Page 250
16-4
Ethernet Card Software Feature and Configuration Guide, R7.2
Chapter 16 Configuring Access Control Lists
Creating IP ACLs
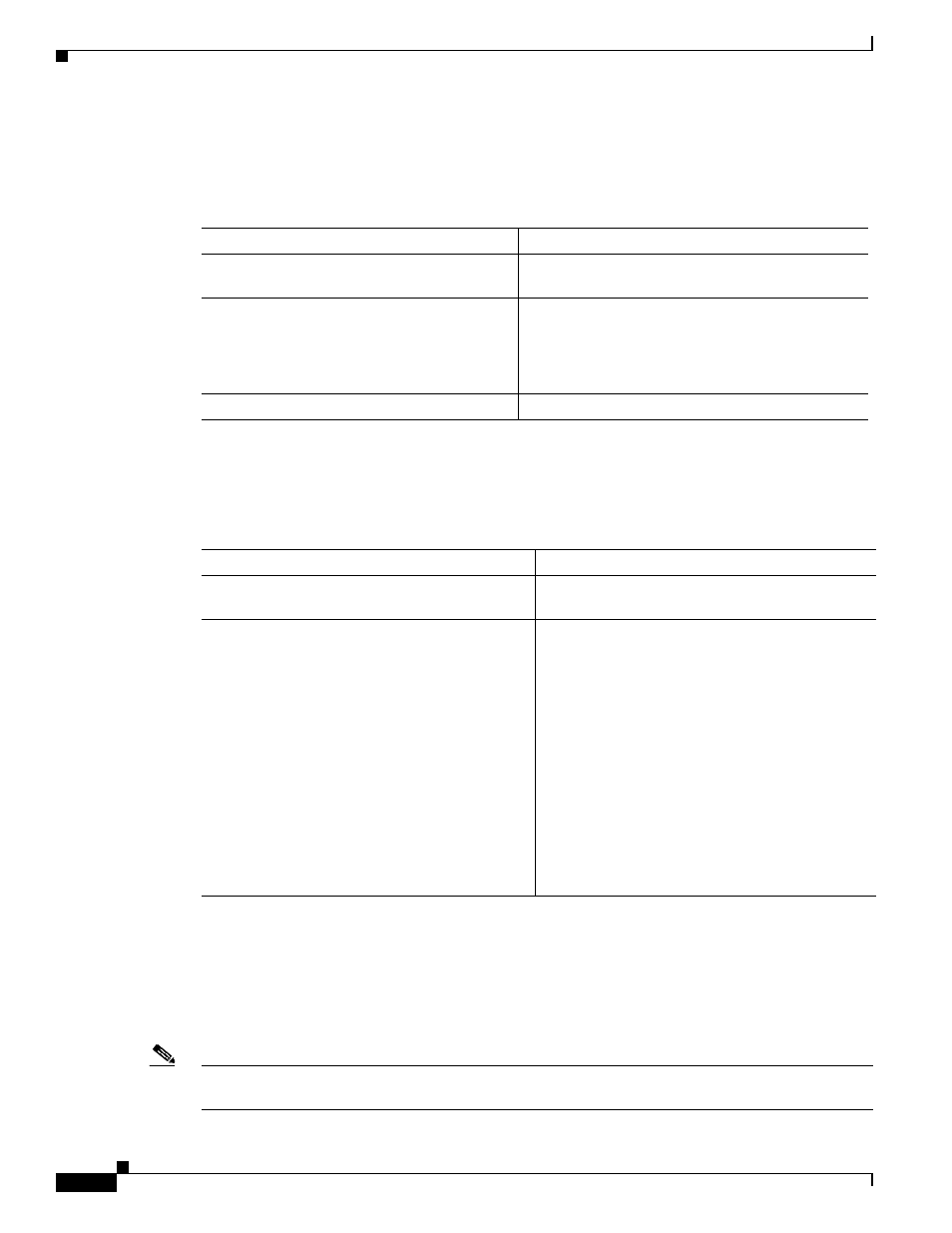
Creating Named Standard IP ACLs
To create a named standard IP ACL, perform the following procedure, beginning in global configuration
mode:
Creating Named Extended IP ACLs (Control Plane Only)
To create a named extended IP ACL, perform the following procedure, beginning in global configuration
mode:
Applying the ACL to an Interface
After you create an ACL, you can apply it to one or more interfaces. ACLs can be applied on either the
inbound or the outbound direction of an interface. When controlling access to an interface, you can use
a name or number. If a standard ACL is applied, the ML-Series card compares the source IP address with
the ACL. To apply an ACL to one or more interfaces, use the command in
.
Note
IP standard ACLs applied to the ingress of a Bridge Group Virtual Interface (BVI) will be applied to all
bridged IP traffic in the associated bridge-group, in addition to the BVI ingress traffic.
Command
Purpose
Step 1
Router(config)# ip access-list standard
name
Defines a standard IP ACL using an alphabetic
name.
Step 2
Router(config-std-nac1)# deny {
source
[
source-wildcard] | any}
or
permit
{
source [source-wildcard] | any}
In access-list configuration mode, specifies one or
more conditions as permitted or denied. This
determines whether the packet is passed or dropped.
Step 3
Router(config)# exit
Exits access-list configuration mode.
Command
Purpose
Step 1
Router(config)# ip access-list extended
name
Defines an extended IP ACL using an alphabetic
name.
Step 2
Router(config-ext-nacl)# {deny | permit}
protocol source source-wildcard destination
destination-wildcard [precedence
precedence] [tos tos]
or
{deny | permit}
protocol any any
or
{deny | permit}
protocol host source host
destination
In access-list configuration mode, specifies the
conditions allowed or denied.
Or:
Defines an extended IP ACL using an abbreviation
for a source and source wildcard of 0.0.0.0
255.255.255.255, and an abbreviation for a
destination and destination wildcard of 0.0.0.0
255.255.255.255.
Or:
Defines an extended IP ACL using an abbreviation
for a source and source wildcard of source 0.0.0.0,
and an abbreviation for a destination and
destination wildcard of destination 0.0.0.0.
