Cisco OL-21636-01 User Manual
Page 147
7-19
Cisco IP Solution Center L2VPN and Carrier Ethernet User Guide, 6.0
OL-21636-01
Chapter 7 Creating an L2VPN Policy
Defining an Ethernet EWS (EPL) Policy with a CE
Step 20
Check the Use Existing ACL Name check box if you want assign your own named access list to the
port. By default, this check box is not checked and ISC automatically assigns a MAC-based ACL on the
customer facing UNI port, based on values you enter in UNI MAC addresses (below).
Step 21
Enter a Port-Based ACL Name (if you checked the Use Existing ACL Name check box, as mentioned
in the previous step).
Note
ISC does not create this ACL automatically. The ACL must already exist on the device, or be
added as part of a template, before the service request is deployed. Otherwise, deployment will
fail.
Step 22
Enter one or more Ethernet MAC addresses in UNI MAC addresses.
This selection is present only if you uncheck the Use Existing ACL Name check box. Click the Edit
button to bring up a pop-up window in which you enter MAC addresses to be allowed or denied on the
port. You can also specify a range of addresses by setting a base MAC address and a filtered MAC
address.
Step 23
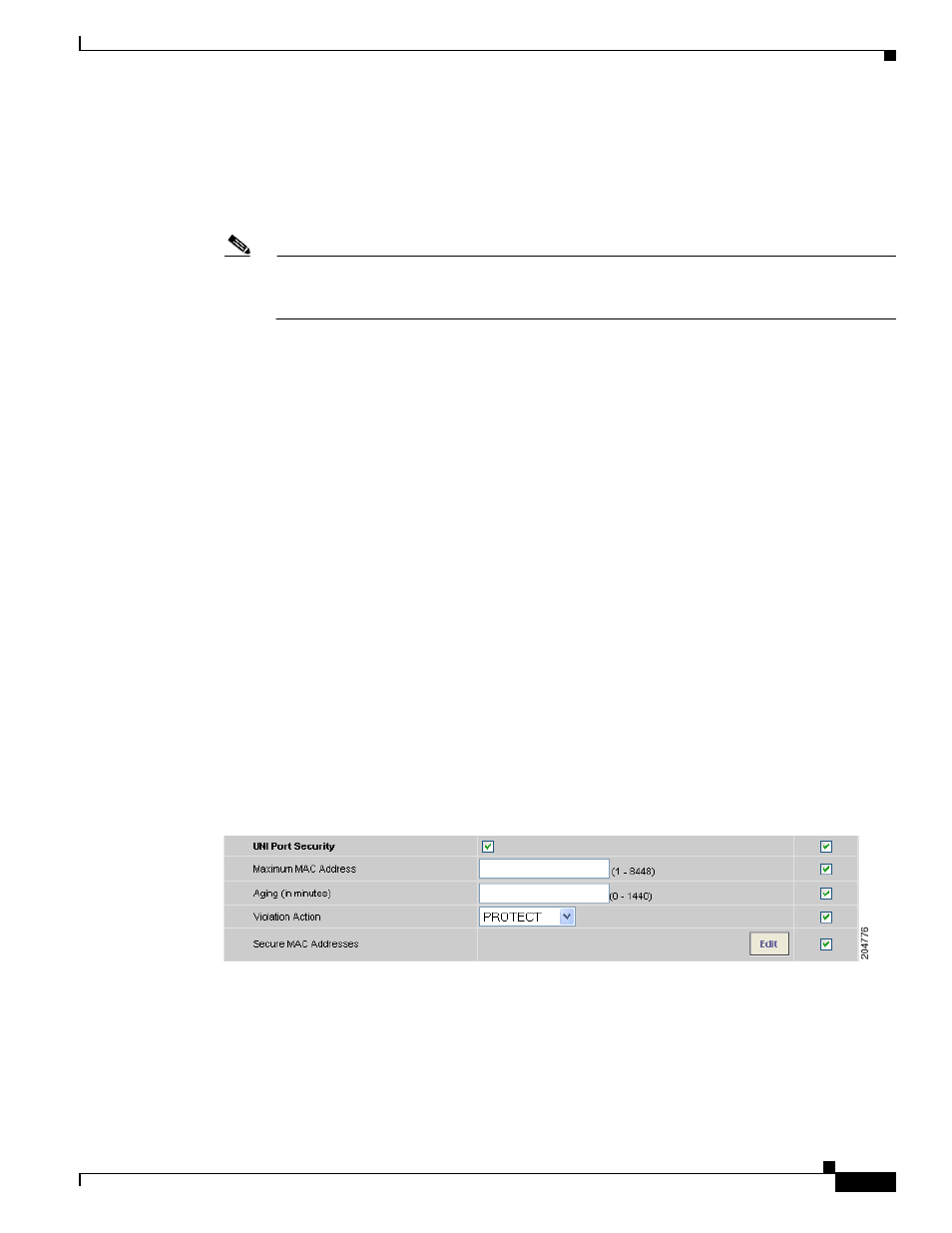
Check the UNI Port Security check box (see
) if you to want to provision port
security-related CLIs to the UNI port by controlling the MAC addresses that are allowed to go through
the interface.
a.
For Maximum Number of MAC address, enter the number of MAC addresses allowed for port
security.
b.
For Aging, enter the length of time the MAC address can stay on the port security table.
c.
For Violation Action, choose what action will occur when a port security violation is detected:
•
PROTECT—Drops packets with unknown source addresses until a sufficient number of secure
MAC addresses are removed to drop below the maximum value.
•
RESTRICT—Drops packets with unknown source addresses until a sufficient number of secure
MAC addresses are removed to drop below the maximum value and causes the Security Violation
counter to increment.
•
SHUTDOWN—Puts the interface into the error-disabled state immediately and sends an SNMP
trap notification.
d.
In the Secure MAC Addresses field, enter one or more Ethernet MAC addresses.
Figure 7-12
UNI Port Security
Step 24
Check the Enable Storm Control check box (see
) to help prevent the UNI port from being
disrupted by a broadcast, multicast, or unicast storm. Enter a threshold value for each type of traffic.
The value, which can be specified to two significant digits, represents the percentage of the total
available bandwidth of the port. If the threshold of a traffic type is reached, further traffic of that type is
suppressed until the incoming traffic falls below the threshold level.
