Table 166 802.1x logs – ZyXEL Communications P-2602HWLNI User Manual
Page 396
Chapter 27 Logs
P-2602HWLNI User’s Guide
396
ip spoofing - WAN [ TCP |
UDP | IGMP | ESP | GRE |
OSPF ]
The firewall detected an IP spoofing attack on the WAN port.
ip spoofing - WAN ICMP
(type:%d, code:%d)
The firewall detected an ICMP IP spoofing attack on the WAN
port.
icmp echo : ICMP
(type:%d, code:%d)
The firewall detected an ICMP echo attack.
syn flood TCP
The firewall detected a TCP syn flood attack.
ports scan TCP
The firewall detected a TCP port scan attack.
teardrop TCP
The firewall detected a TCP teardrop attack.
teardrop UDP
The firewall detected an UDP teardrop attack.
teardrop ICMP (type:%d,
code:%d)
The firewall detected an ICMP teardrop attack.
illegal command TCP
The firewall detected a TCP illegal command attack.
NetBIOS TCP
The firewall detected a TCP NetBIOS attack.
ip spoofing - no routing
entry [ TCP | UDP | IGMP
| ESP | GRE | OSPF ]
The firewall classified a packet with no source routing entry as an
IP spoofing attack.
ip spoofing - no routing
entry ICMP (type:%d,
code:%d)
The firewall classified an ICMP packet with no source routing
entry as an IP spoofing attack.
vulnerability ICMP
(type:%d, code:%d)
The firewall detected an ICMP vulnerability attack.
traceroute ICMP (type:%d,
code:%d)
The firewall detected an ICMP traceroute attack.
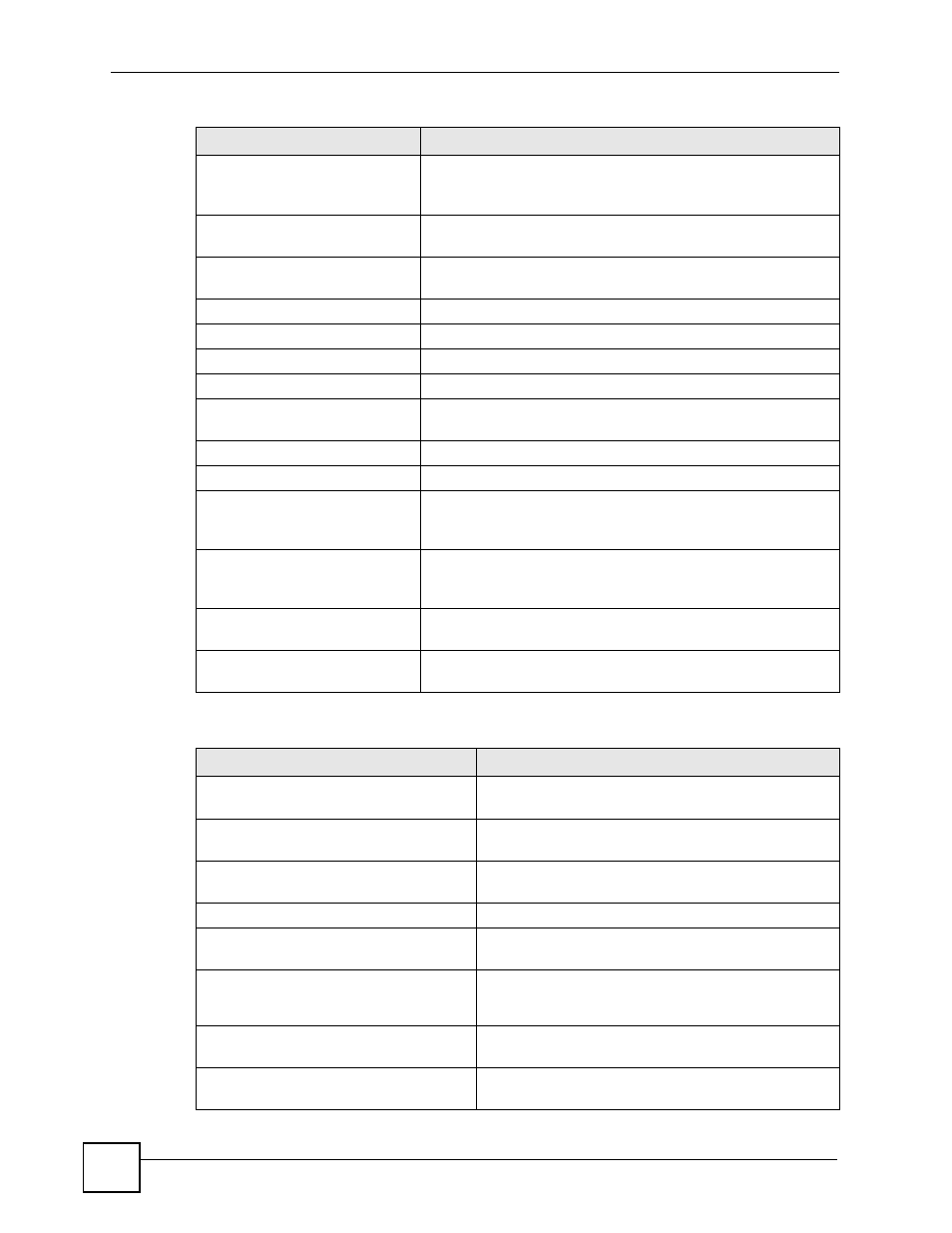
Table 166 802.1X Logs
LOG MESSAGE
DESCRIPTION
Local User Database accepts
user.
A user was authenticated by the local user database.
Local User Database reports user
credential error.
A user was not authenticated by the local user database
because of an incorrect user password.
Local User Database does not
find user`s credential.
A user was not authenticated by the local user database
because the user is not listed in the local user database.
RADIUS accepts user.
A user was authenticated by the RADIUS Server.
RADIUS rejects user. Pls check
RADIUS Server.
A user was not authenticated by the RADIUS Server.
Please check the RADIUS Server.
Local User Database does not
support authentication method.
The local user database only supports the EAP-MD5
method. A user tried to use another authentication
method and was not authenticated.
User logout because of session
timeout expired.
The router logged out a user whose session expired.
User logout because of user
deassociation.
The router logged out a user who ended the session.
Table 165 Attack Logs (continued)
LOG MESSAGE
DESCRIPTION
