Configuring nd attack defense, Overview – H3C Technologies H3C SecBlade LB Cards User Manual
Page 275
264
Configuring ND attack defense
ND attack defense can be configured only at the CLI.
Overview
The IPv6 Neighbor Discovery (ND) protocol provides rich functions, such as address resolution, neighbor
reachability detection, duplicate address detection, router/prefix discovery and address
autoconfiguration, and redirection. However, it does not provide any security mechanisms. Attackers can
easily exploit the ND protocol to attack hosts and gateways by sending forged packets.
The ND protocol implements its function by using five types of ICMPv6 messages:
•
Neighbor Solicitation (NS)
•
Neighbor Advertisement (NA)
•
Router Solicitation (RS)
•
Router Advertisement (RA)
•
Redirect (RR)
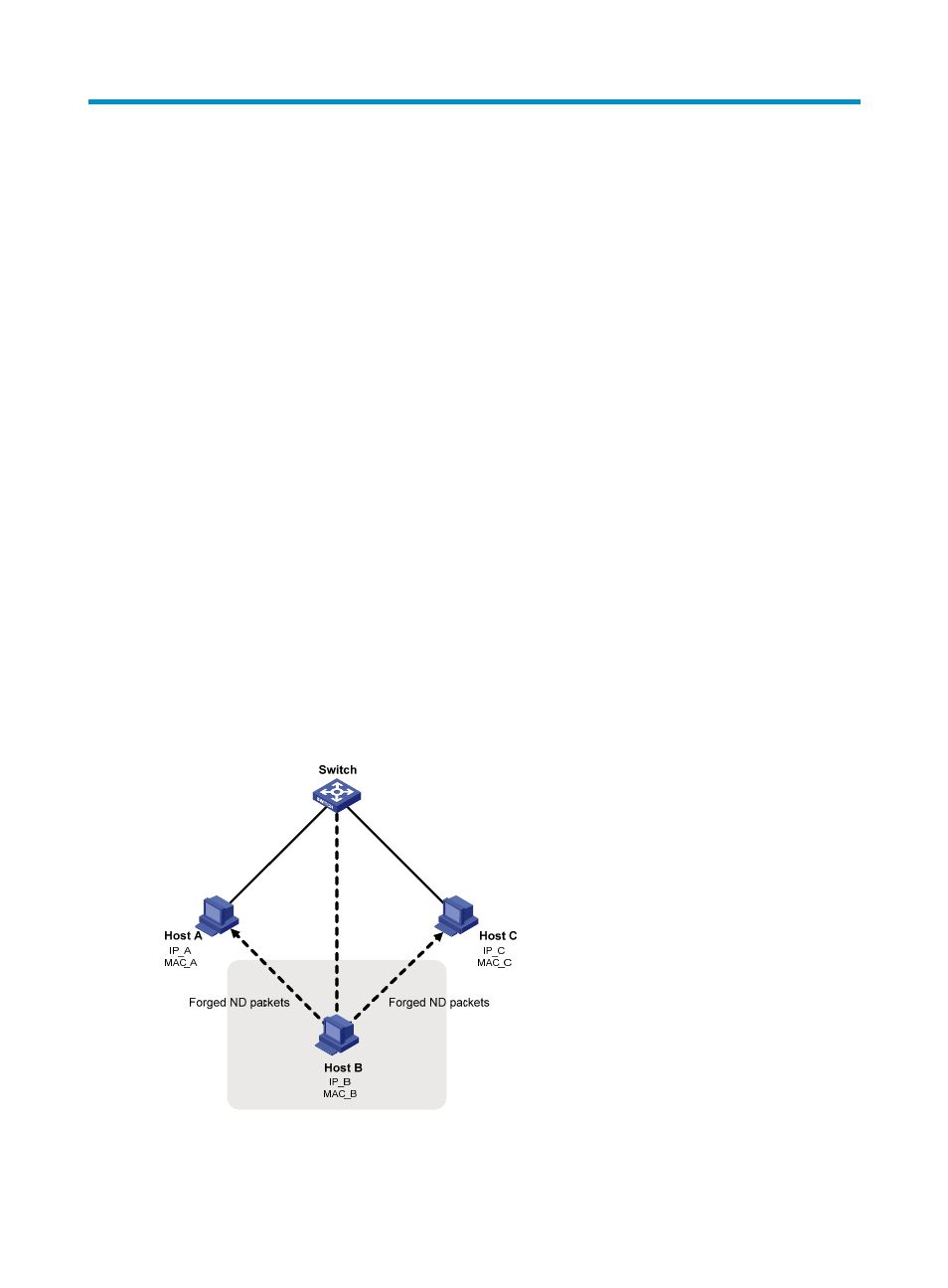
An attacker can attack a network by sending forged ICMPv6 messages, as shown in
:
•
Sending forged NS/NA/RS packets with the IPv6 address of a victim host. The gateway and other
hosts update the ND entry for the victim host with incorrect address information. As a result, all
packets intended for the victim host are sent to the attacking host.
•
Sending forged RA packets with the IPv6 address of a victim gateway. As a result, all hosts attached
to the victim gateway maintain incorrect IPv6 configuration parameters and ND entries.
Figure 146 ND attack diagram
All forged ND packets have two common features:
