Verifying a trusted remote host’s certificate, 13 verifying a trusted remote host’s certificate – ZyXEL Communications Internet Security Gateway ZyWALL 2 Series User Manual
Page 269
ZyWALL 2 Series User’s Guide
Certificates
15-23
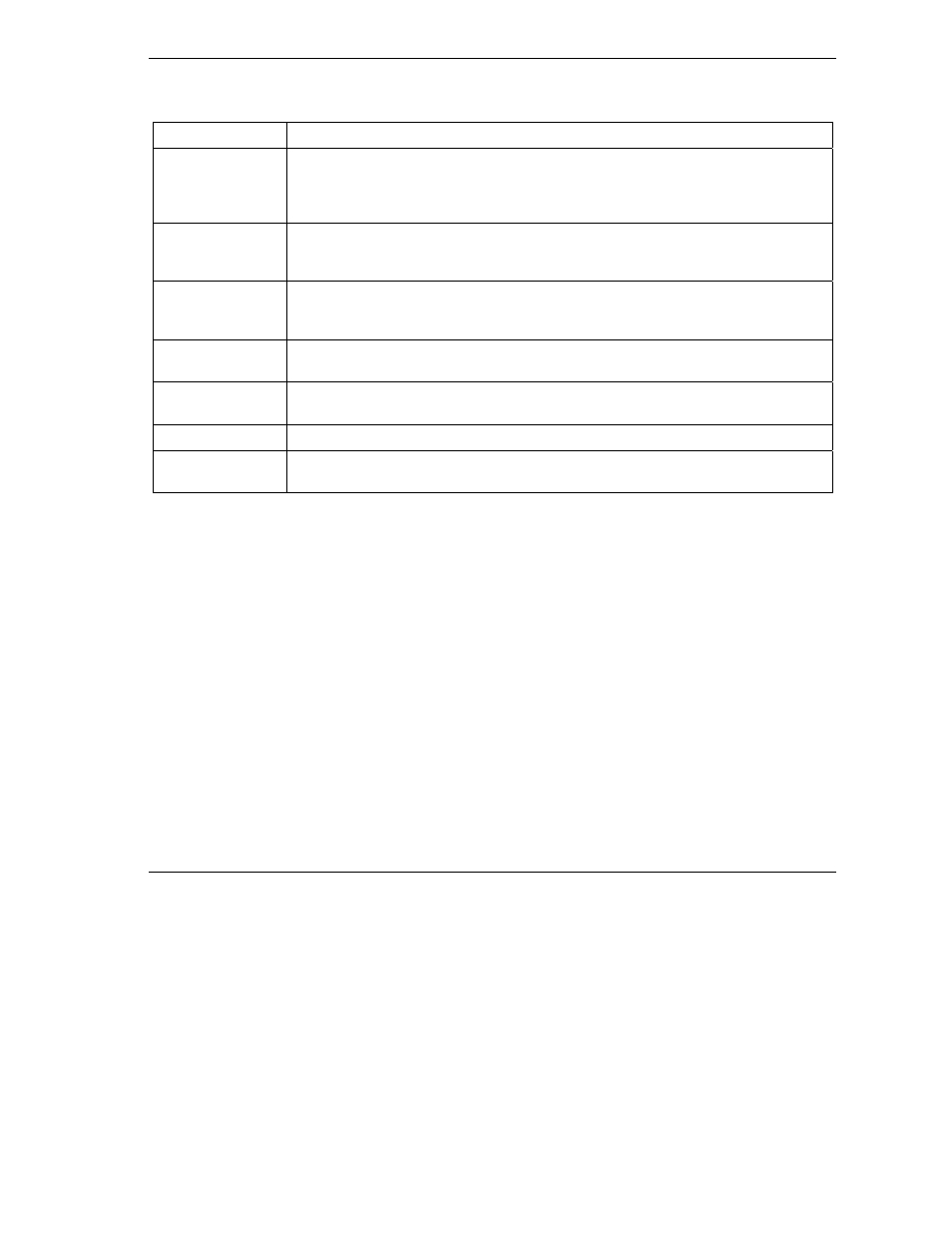
Table 15-8 Trusted Remote Hosts
LABEL DESCRIPTION
Subject
This field displays identifying information about the certificate’s owner, such as CN
(Common Name), OU (Organizational Unit or department), O (Organization or
company) and C (Country). It is recommended that each certificate have unique
subject information.
Valid From
This field displays the date that the certificate becomes applicable. The text displays
in red and includes a “Not Yet Valid!” message if the certificate has not yet become
applicable.
Valid To
This field displays the date that the certificate expires. The text displays in red and
includes an “Expiring!” or “Expired!” message if the certificate is about to expire or
has already expired.
Import
Click Import to open a screen where you can save the certificate of a remote host
(which you trust) from your computer to the ZyWALL.
Details
Select the radio button next to a certificate’s index number and then click Details to
open a screen with an in-depth list of information about that certificate.
Refresh
Click this button to display the current validity status of the certificates.
Delete
Select the radio button next to the index number of a certificate that you want to
delete and then click Delete to remove that certificate.
15.13 Verifying a Trusted Remote Host’s Certificate
Certificates issued by certification authorities have the certification authority’s signature for you to check.
Self-signed certificates only have the signature of the host itself. This means that you must be very careful
when deciding to import (and thereby trust) a remote host’s self-signed certificate.
15.13.1
Trusted Remote Host Certificate Fingerprints
A certificate’s fingerprints are message digests calculated using the MD5 or SHA1 algorithms. The following
procedure describes how to use a certificate’s fingerprint to verify that you have the remote host’s actual
certificate.
Step 1.
Browse to where you have the remote host’s certificate saved on your computer.
Step 2.
Make sure that the certificate has a “.cer” or “.crt” file name extension.
