ZyXEL Communications 802.11g Wireless ADSL2+ 4-port VoIP IAD P-2602HWNLI User Manual
Page 326
P-2602HWNLI User’s Guide
326
Chapter 24 Logs
Triangle route packet forwarded:
[ TCP | UDP | IGMP | ESP | GRE |
OSPF ]
The firewall allowed a triangle route session to pass
through.
Packet without a NAT table entry
blocked: [ TCP | UDP | IGMP | ESP
| GRE | OSPF ]
The router blocked a packet that didn't have a
corresponding NAT table entry.
Router sent blocked web site
message: TCP
The router sent a message to notify a user that the router
blocked access to a web site that the user requested.
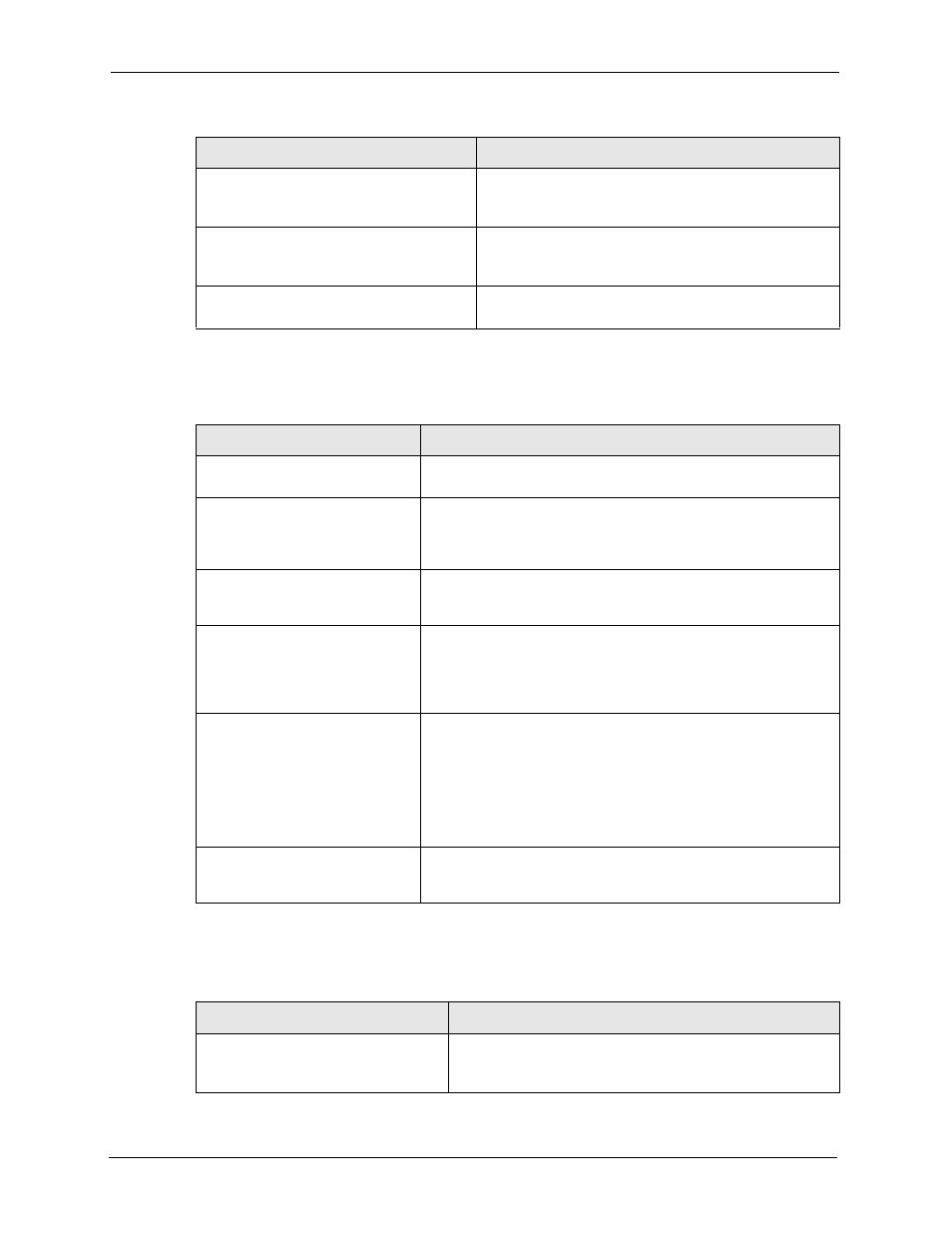
Table 128 TCP Reset Logs
LOG MESSAGE
DESCRIPTION
Under SYN flood attack,
sent TCP RST
The router sent a TCP reset packet when a host was under a SYN
flood attack (the TCP incomplete count is per destination host.)
Exceed TCP MAX
incomplete, sent TCP RST
The router sent a TCP reset packet when the number of TCP
incomplete connections exceeded the user configured threshold.
(the TCP incomplete count is per destination host.) Note: Refer to
TCP Maximum Incomplete in the Firewall Attack Alerts screen.
Peer TCP state out of
order, sent TCP RST
The router sent a TCP reset packet when a TCP connection state
was out of order.Note: The firewall refers to RFC793 Figure 6 to
check the TCP state.
Firewall session time
out, sent TCP RST
The router sent a TCP reset packet when a dynamic firewall
session timed out.Default timeout values:ICMP idle timeout (s):
60UDP idle timeout (s): 60TCP connection (three way
handshaking) timeout (s): 30TCP FIN-wait timeout (s): 60TCP idle
(established) timeout (s): 3600
Exceed MAX incomplete,
sent TCP RST
The router sent a TCP reset packet when the number of
incomplete connections (TCP and UDP) exceeded the user-
configured threshold. (Incomplete count is for all TCP and UDP
connections through the firewall.)Note: When the number of
incomplete connections (TCP + UDP) > “Maximum Incomplete
High”, the router sends TCP RST packets for TCP connections
and destroys TOS (firewall dynamic sessions) until incomplete
connections < “Maximum Incomplete Low”.
Access block, sent TCP
RST
The router sends a TCP RST packet and generates this log if you
turn on the firewall TCP reset mechanism (via CI command: "sys
firewall tcprst").
Table 129 Packet Filter Logs
LOG MESSAGE
DESCRIPTION
[ TCP | UDP | ICMP | IGMP |
Generic ] packet filter
matched (set: %d, rule: %d)
Attempted access matched a configured filter rule (denoted by
its set (%d) and rule number (%d)) and was blocked or
forwarded according to the rule.
Table 127 Access Control Logs (continued)
LOG MESSAGE
DESCRIPTION
