Custom security features using ip filters, How filtering works – Eicon Networks 1550 User Manual
Page 63
Security
63
Custom Security Features using IP Filters
By using IP filters you can create your own custom security solutions. For example,
you can limit local access to the Eicon 1550/1551 for specific computers, accept
incoming traffic only from certain remote users or networks, or drop incoming or
outgoing nuisance traffic.
•
................................................................................ 63
•
............................................................................... 64
•
..................................................................... 66
•
Example: Dropping incoming traffic from a specific network
•
Example: Allowing incoming traffic only from a specific network
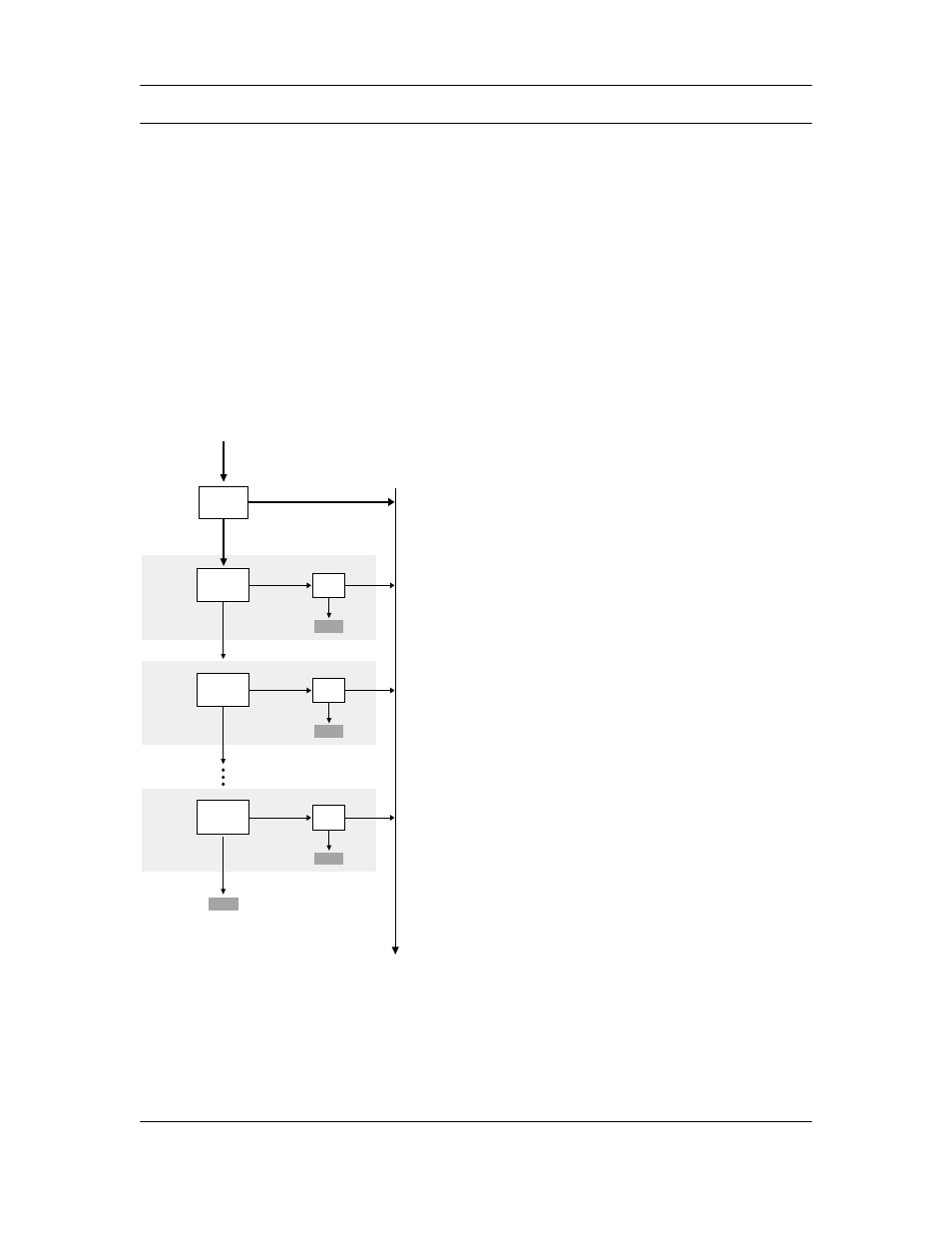
How Filtering Works
Each profile you define for a
particular connection has its
own set of filters (called the
‘filter stack’). All data packets,
incoming and outgoing, pass
through the filter stack of the
profile being used for a
particular connection. A filter
stack can have up to 8 filters,
allowing for sophisticated
results.
Data cascades through the
filter stack as shown in the
following diagram. If a packet
matches one of the filters in
the stack, the filter action is
performed.
Note: All incoming and outgoing
data passes through the filter
stack. Once any filter is activated,
data transfer will be affected.
Filter #2
Filter #1
Data that matches
Data that matches
Drop
Drop
Forward
Forward
Apply filter
conditions
Apply filter
conditions
Action
Action
Data that does
not match
Data that does
not match
Filter #8
Output from filter stack
Input to filter stack
Data that matches
Drop
Forward
Apply filter
conditions
Action
Data that does
not match
No
Yes
Are any filters
active?
Bypass filter stack
Send all data into filter stack
Discard
Discard
Discard
Discard
