10 security parameters summary, Figure 28 wpa with radius application example, Table 16 wireless security relational matrix – ZyXEL Communications ADSL VoIP IAD with 802.11g Wireless 2602HW Series User Manual
Page 98
Prestige 2602HW Series User’s Guide
98
Chapter 6 Wireless LAN Setup
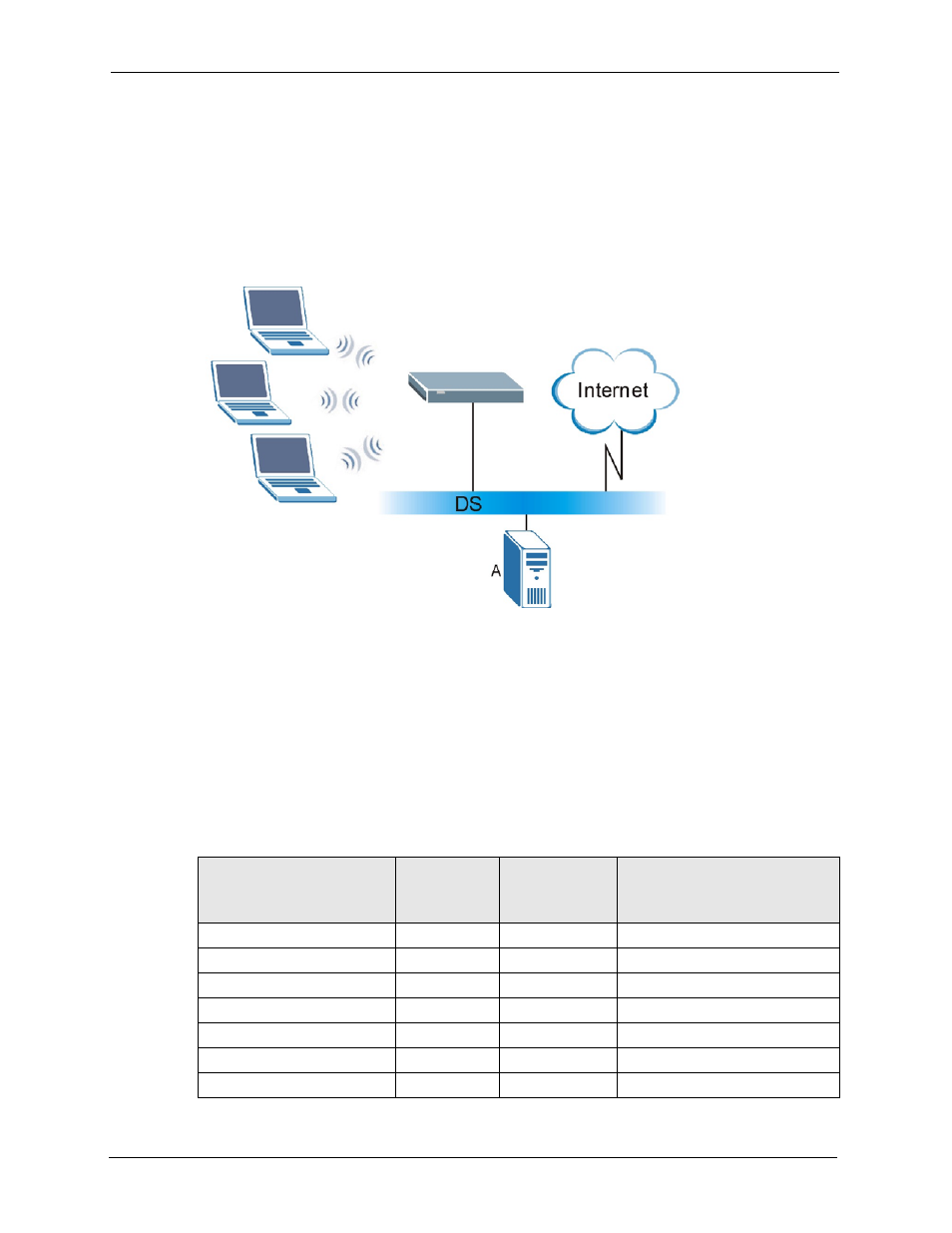
2 The RADIUS server then checks the user's identification against its database and grants
or denies network access accordingly.
3 The RADIUS server distributes a Pairwise Master Key (PMK) key to the AP that then
sets up a key hierarchy and management system, using the pair-wise key to dynamically
generate unique data encryption keys to encrypt every data packet that is wirelessly
communicated between the AP and the wireless clients
Figure 28 WPA with RADIUS Application Example
6.10 Security Parameters Summary
Refer to this table to see what other security parameters you should configure for each
Authentication Method/ key management protocol type. You enter manual keys by first
selecting 64-bit WEP or 128-bit WEP from the WEP Encryption field and then typing the
keys (in ASCII or hexadecimal format) in the key text boxes. MAC address filters are not
dependent on how you configure these security features.
Table 16 Wireless Security Relational Matrix
AUTHENTICATION
METHOD/ KEY
MANAGEMENT PROTOCOL
ENCRYPTION
METHOD
ENTER
MANUAL KEY
ENABLE IEEE 802.1X
Open None
No
No
Open
WEP
No
Enable with Dynamic WEP Key
Yes
Enable without Dynamic WEP Key
Yes
Disable
Shared
WEP
No
Enable with Dynamic WEP Key
Yes
Enable without Dynamic WEP Key
Yes
Disable
