Vpn screens, 1 vpn/ipsec overview, 2 ipsec algorithms – ZyXEL Communications ADSL VoIP IAD with 802.11g Wireless 2602HW Series User Manual
Page 201: 1 ah (authentication header) protocol, Chapter 17 vpn screens, 1 vpn/ipsec overview 17.2 ipsec algorithms
Prestige 2602HW Series User’s Guide
Chapter 17 VPN Screens
201
C
H A P T E R
17
VPN Screens
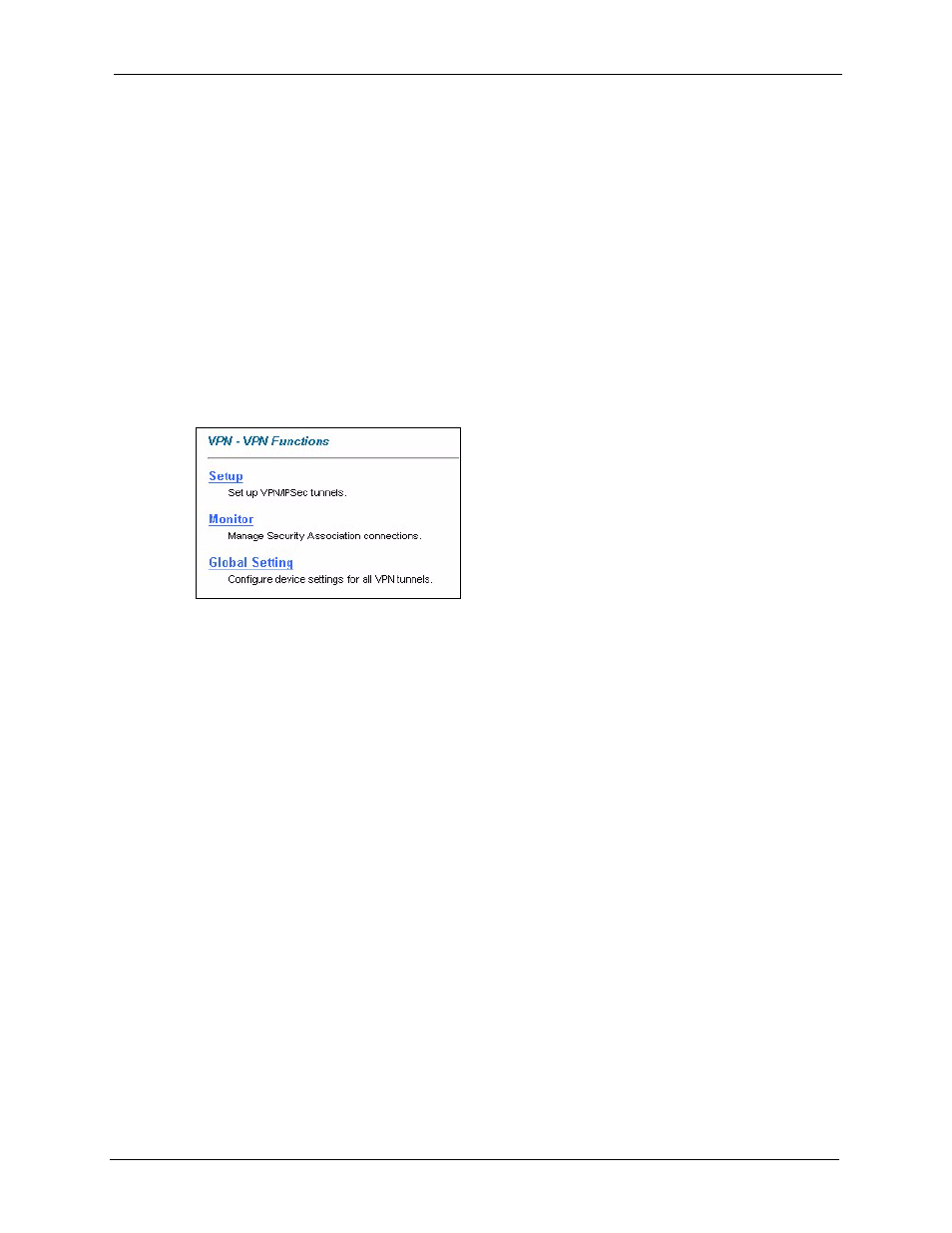
This chapter introduces the VPN screens. See the chapter on logs for information on viewing
logs and the appendix on logs for IPSec log descriptions.
17.1 VPN/IPSec Overview
Use the screens documented in this chapter to configure rules for VPN connections and
manage VPN connections.
17.2 IPSec Algorithms
The ESP and AH protocols are necessary to create a Security Association (SA), the
foundation of an IPSec VPN. An SA is built from the authentication provided by the AH and
ESP protocols. The primary function of key management is to establish and maintain the SA
between systems. Once the SA is established, the transport of data may commence.
17.2.1 AH (Authentication Header) Protocol
AH protocol (RFC 2402) was designed for integrity, authentication, sequence integrity (replay
resistance), and non-repudiation but not for confidentiality, for which the ESP was designed.
In applications where confidentiality is not required or not sanctioned by government
encryption restrictions, an AH can be employed to ensure integrity. This type of
implementation does not protect the information from dissemination but will allow for
verification of the integrity of the information and authentication of the originator.
