1 stateful inspection process, Figure 64 stateful inspection – ZyXEL Communications ADSL VoIP IAD with 802.11g Wireless 2602HW Series User Manual
Page 162
Prestige 2602HW Series User’s Guide
162
Chapter 13 Firewalls
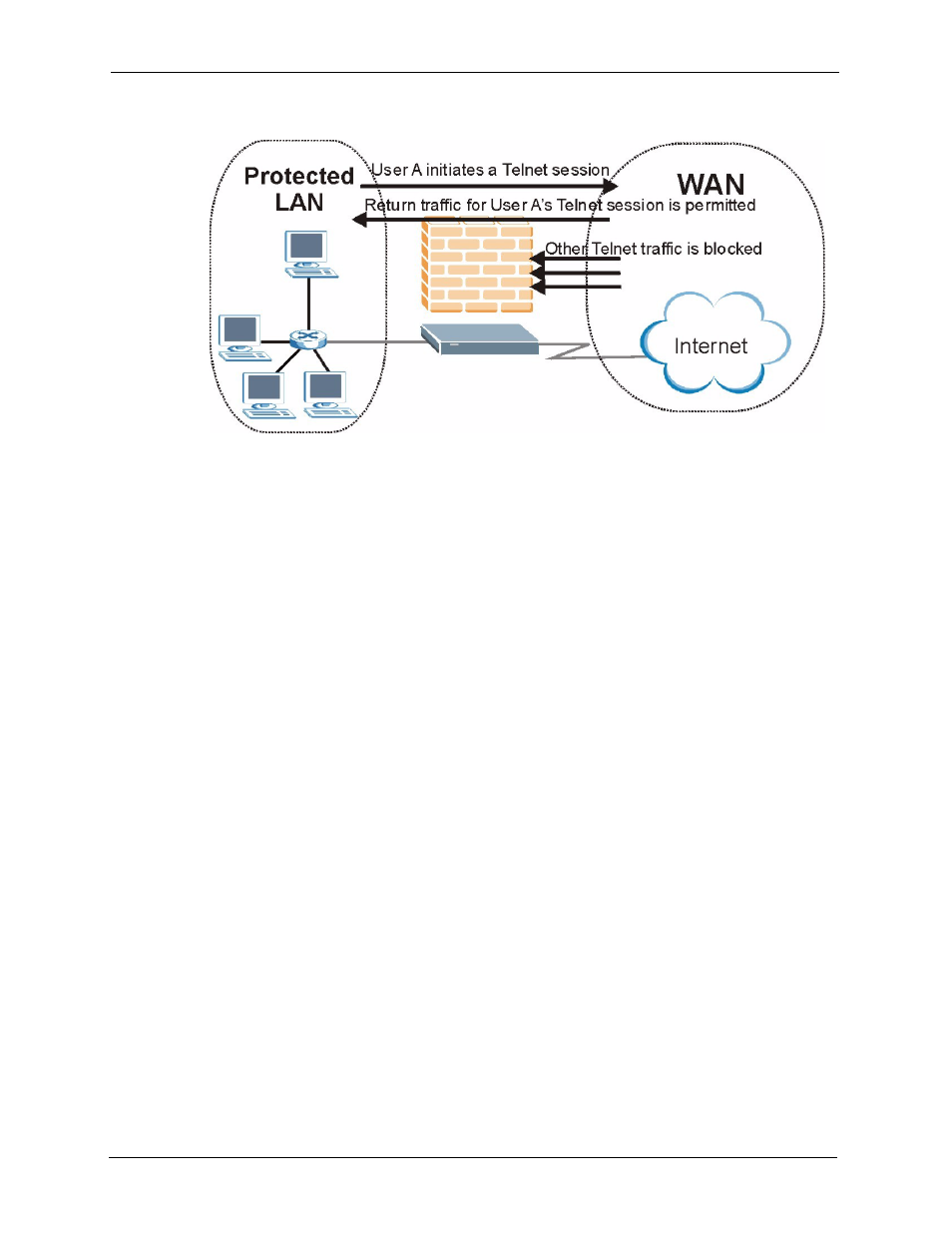
Figure 64 Stateful Inspection
The previous figure shows the Prestige’s default firewall rules in action as well as
demonstrates how stateful inspection works. User A can initiate a Telnet session from within
the LAN and responses to this request are allowed. However other Telnet traffic initiated from
the WAN is blocked.
13.5.1 Stateful Inspection Process
In this example, the following sequence of events occurs when a TCP packet leaves the LAN
network through the firewall's WAN interface. The TCP packet is the first in a session, and the
packet's application layer protocol is configured for a firewall rule inspection:
1 The packet travels from the firewall's LAN to the WAN.
2 The packet is evaluated against the interface's existing outbound access list, and the
packet is permitted (a denied packet would simply be dropped at this point).
3 The packet is inspected by a firewall rule to determine and record information about the
state of the packet's connection. This information is recorded in a new state table entry
created for the new connection. If there is not a firewall rule for this packet and it is not an
attack, then the settings in the Default Policy screen determine the action for this packet.
4 Based on the obtained state information, a firewall rule creates a temporary access list
entry that is inserted at the beginning of the WAN interface's inbound extended access
list. This temporary access list entry is designed to permit inbound packets of the same
connection as the outbound packet just inspected.
5 The outbound packet is forwarded out through the interface.
6 Later, an inbound packet reaches the interface. This packet is part of the connection
previously established with the outbound packet. The inbound packet is evaluated against
the inbound access list, and is permitted because of the temporary access list entry
previously created.
7 The packet is inspected by a firewall rule, and the connection's state table entry is updated
as necessary. Based on the updated state information, the inbound extended access list
