0 key management, 1 key generation, 248 hsm security policy – Nortel Networks NN46120-104 User Manual
Page 248
248
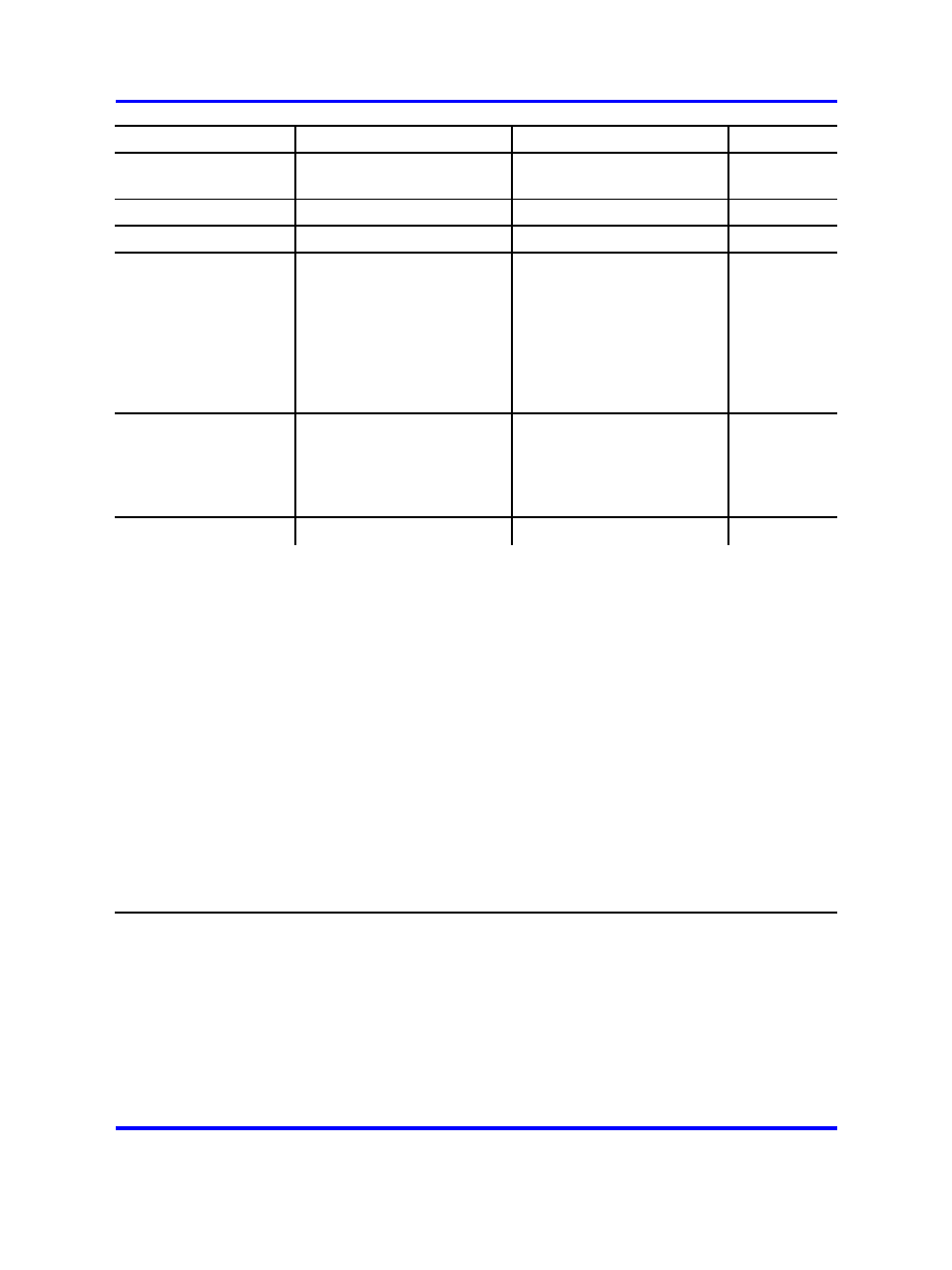
HSM Security Policy
Service
FIPS140-1 Level 3 Mode
Non- FIPS140-1 Mode
Not auth
enticated
User
Role
SO Role
Not auth
enticated
User
Role
SO Role
SRDIs Access
ed
RSA Verify
NO
YES
YES
NO
YES
YES
VPK (use)
Generate Key (note 6)
NO
YES
YES
NO
YES
YES
KWK (create)
Split Key
NO
YES
YES
NO
YES
YES
KWK (split), PR
NGKey (create,
destroy), Two
KWKShares
(created
and written
to trusted
interface)
Combine Key
NO
YES
YES
NO
YES
YES
KWK (created),
two KWKS
hares (read
from trusted
interface)
Set LED State
YES
YES
YES
YES
YES
YES
None.
Note 1 =
The key for these commands is input through the PCI bus (data input interface)
Note 2 =
This is a PKCS 12 method for deriving a 3DES key from a password, salt and iteration count.
Note 3 =
The Exponentiation Using CRT and Exponentiation functions are generic math functions; all
parameters are input through the PCI interface (data input interface).
Note 4 =
When operating in the FIPS140-1 mode, it is not possible for secret keys, private keys or critical
security parameters to cross the PCI bus without being wrapped (encrypted) using the Key-Wrapping
Key.
Note 5 =
User Login is the process that takes the board from an unauthenticated state to the authenticated
state. Only one user may be authenticated at a particular time. Consequently, the User Login process
cannot be started from the authenticated state. Nonetheless, the User Login process cannot be
completed successfully without authentication.
Note 6 =
This command is used for generating the key-wrapping-key.
Note 7 =
When the board is in the zeroized state, it is possible to for an unauthenticated user to uninitialize
the board.
Note 8 =
These operations must access stored cryptographic keys. The keys may not be input through the
PCI interface.
10.0 Key Management
10.1 Key Generation
Random number generation for key generation is accomplished using
the algorithm described by appendix C of ANSI standard X9.17. This
algorithm will use a seed value V (from appendix C) that is generated by
the random number generator in the FastMap chip. Using this algorithm
ensures that the keys generated will be consistent with the requirements
of FIPS 140-1. Performing the key generation in this manner will ensure
Nortel VPN Gateway
User Guide
NN46120-104
02.01
Standard
14 April 2008
Copyright © 2007-2008 Nortel Networks
.
