Ssl configuration, Ssl overview, Ssl security mechanism – H3C Technologies H3C SecPath F1000-E User Manual
Page 91
1
SSL Configuration
This chapter includes these sections:
•
•
•
Displaying and Maintaining SSL
•
SSL Overview
Secure Sockets Layer (SSL) is a security protocol that provides secure connection services for TCP-based
application layer protocols, for example, HTTP protocol. It is widely used in E-business and online bank
fields to ensure secure data transmission over the Internet.
SSL Security Mechanism
Secure connections provided by SSL have these features:
•
Confidentiality – SSL uses a symmetric encryption algorithm to encrypt data and uses the
asymmetric key algorithm of Rivest, Shamir, and Adelman (RSA) to encrypt the key to be used by the
symmetric encryption algorithm.
•
Authentication – SSL supports certificate-based identity authentication of the server and client by
using the digital signatures. The SSL server and client obtain certificates from a certificate authority
(CA) through the Public Key Infrastructure (PKI).
•
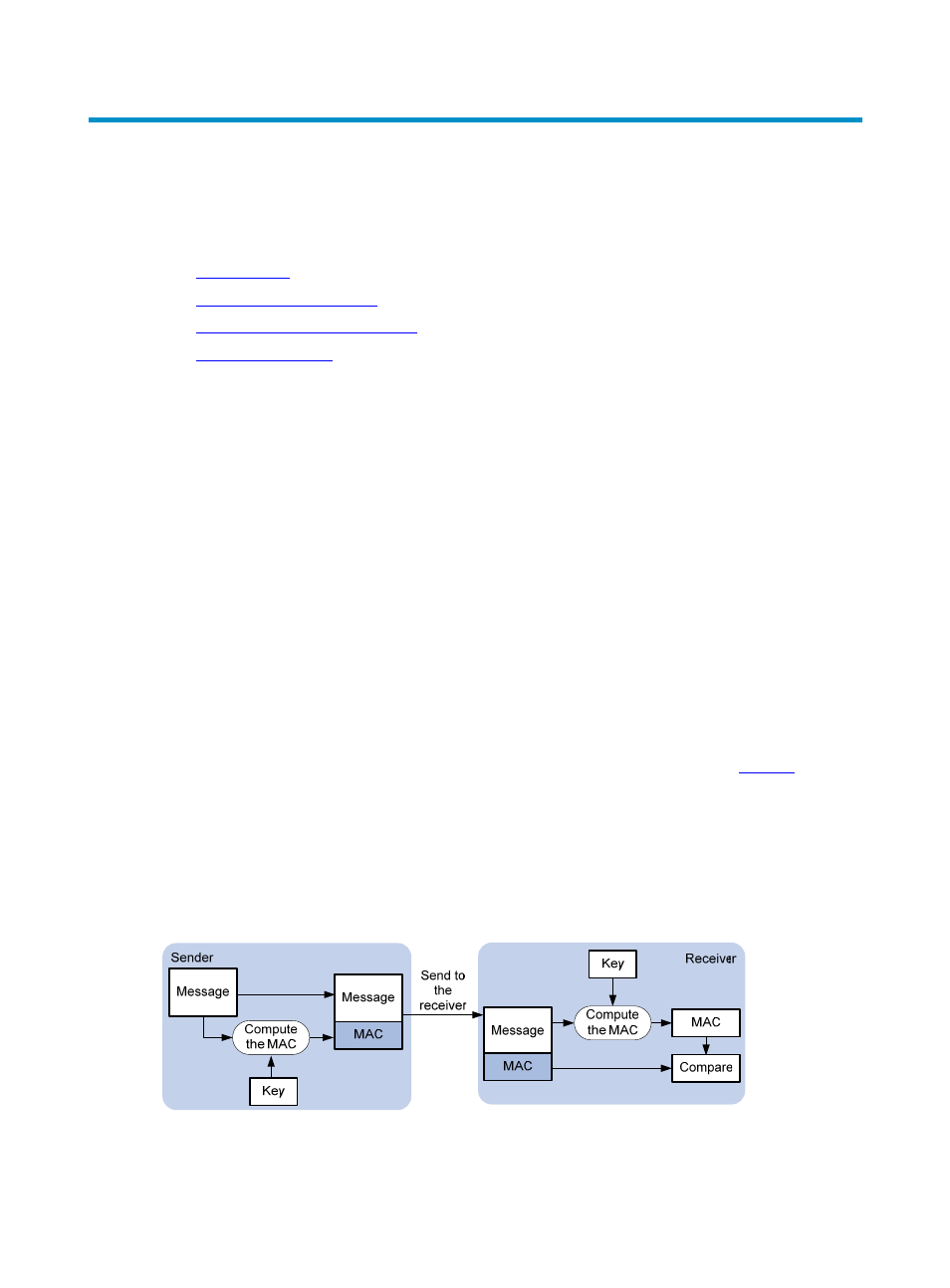
Reliability – SSL uses the key-based message authentication code (MAC) to verify message integrity.
A MAC algorithm transforms a message of any length to a fixed-length message.
illustrates
how SSL uses a MAC algorithm to verify message integrity. With the key, the sender uses the MAC
algorithm to compute the MAC value of a message. Then, the sender suffixes the MAC value to the
message and sends the result to the receiver. The receiver uses the same key and MAC algorithm to
compute the MAC value of the received message, and compares the locally computed MAC value
with that received. If the two matches, the receiver considers the message intact; otherwise, the
receiver considers that the message has been tampered with in transit and discards the message.
Figure 1 Message integrity verification by a MAC algorithm
